Top 15 Cybersecurity Courses in the USA (2026)

Riten Debnath
18 Feb, 2026

The digital landscape is shifting under our feet, and as we move deeper into 2026, the stakes for data protection have never been higher. With the rise of sophisticated AI-driven attacks and the expansion of decentralized networks, companies are no longer just looking for "IT people," they are hunting for specialized defenders who can think like hackers. Whether you are a student looking to break into the field or a professional aiming for a six-figure leadership role, the right training is the only bridge between where you are and where the industry is heading.
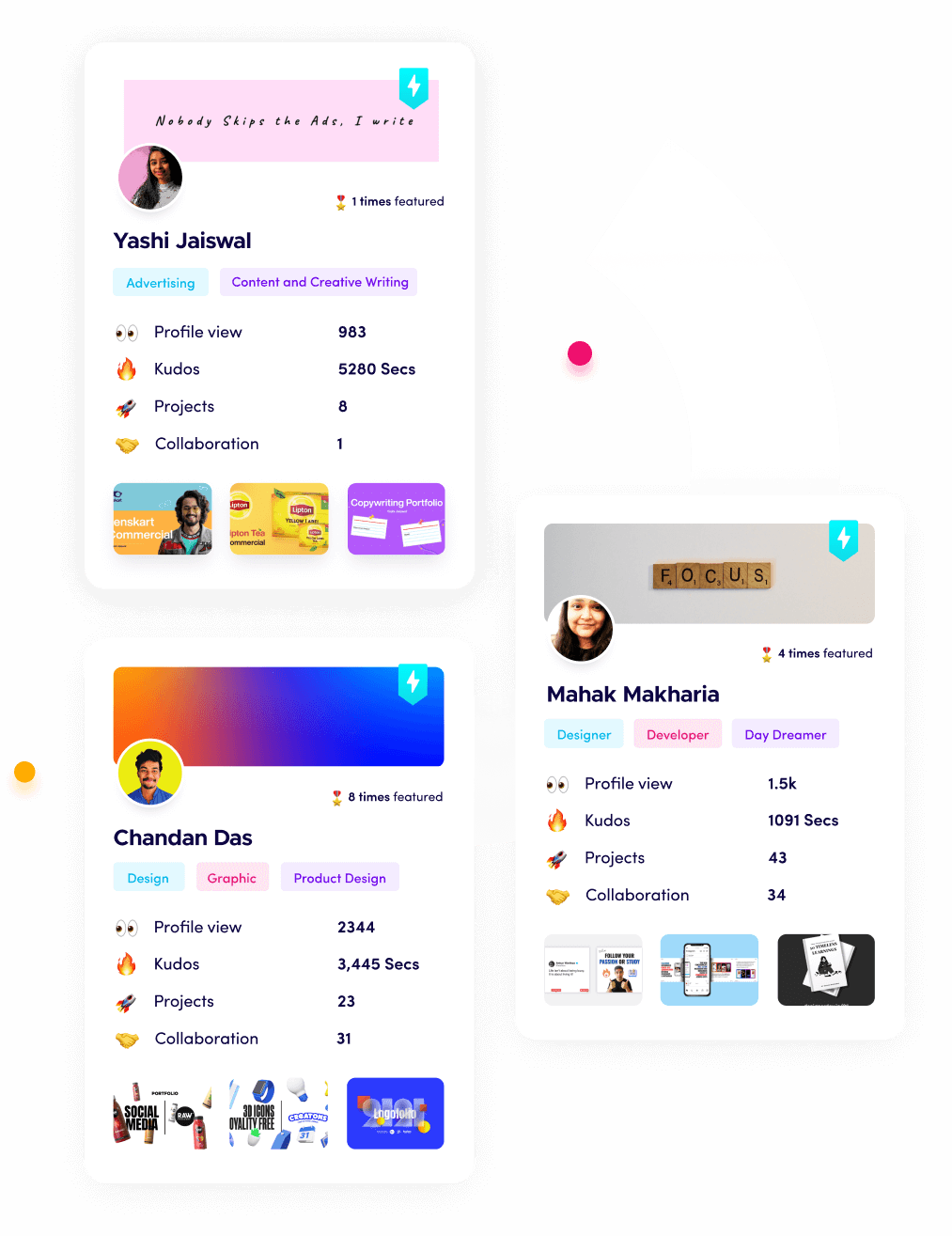
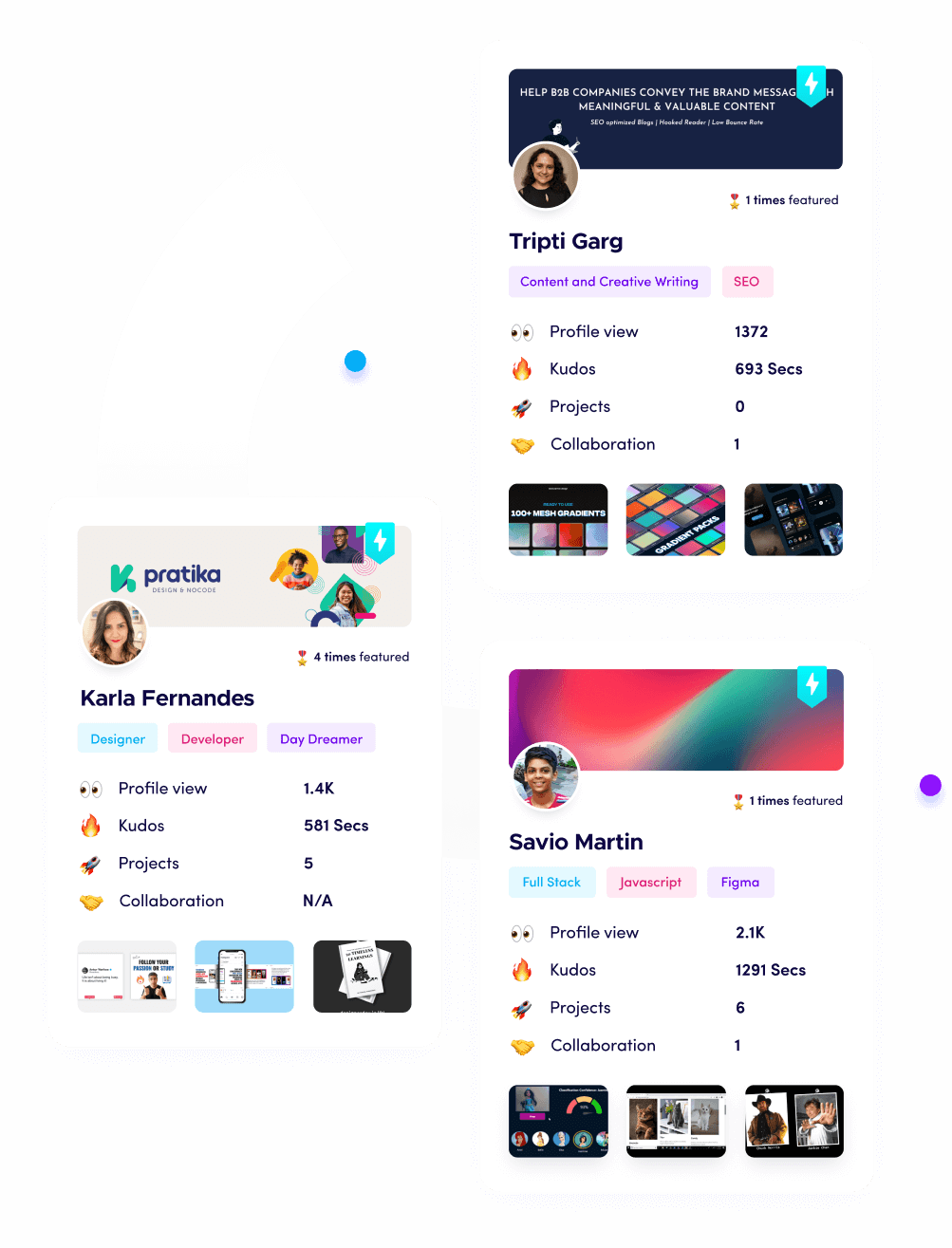
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
Top-Tier Cybersecurity Programs for Career Growth in 2026
1. Google Cybersecurity Professional Certificate (Coursera)
This program has become the gold standard for beginners entering the field because it was built by Google experts specifically to fill entry-level gaps. It provides a massive amount of practical experience by using real security tools like Python, Linux, and SQL to solve modern problems. By the time you finish, you will have a deep understanding of how to identify risks and respond to incidents using the same frameworks used at major tech giants.
- Hands-on Tooling and SIEM Integration: You will gain direct, practical experience with security information and event management (SIEM) tools like Chronicle and Sentinel, which are essential for monitoring live threats and analyzing security logs in real-time environments to catch intruders before they can cause damage.
- Python for Security Automation: The course teaches you how to write custom Python scripts specifically designed to automate repetitive security tasks, extract data from large logs, and create efficient workflows for threat detection and response, making you much more efficient than a manual analyst.
- Deep Dive into Networking Fundamentals: It breaks down the complexities of the TCP/IP model and various network protocols so you understand exactly how data moves across the internet and where the most common vulnerabilities exist within a corporate network infrastructure today.
- NIST Cybersecurity Framework Application: You will learn how to apply the National Institute of Standards and Technology (NIST) Framework to protect an organization’s digital assets, ensuring you follow the most recognized security standards in the industry that high-end firms require.
- Professional Portfolio Development: Every module includes a specific lab or project that helps you build a professional portfolio of work, allowing you to show recruiters that you can actually handle the day-to-day tasks of a cybersecurity analyst rather than just knowing the theory.
Why it matters: In 2026, having a "Google-approved" foundation is a major signal to recruiters that you possess the modern technical skills required for a Junior Cybersecurity Analyst role without needing a traditional degree.
2. CISSP: Certified Information Systems Security Professional (ISC2)
Widely recognized as the "PhD of Cybersecurity," the CISSP is the most sought-after certification for those moving into senior management or security architecture roles. In 2026, its curriculum was updated to reflect the critical importance of AI governance and decentralized identity. It covers eight diverse domains, ensuring you have the breadth of knowledge to oversee an entire organization's security posture and make high-level strategic decisions.
- Security and Risk Management Leadership: You will master the art of aligning security functions with business goals, learning how to manage organizational risk, comply with global legal regulations, and establish a culture of professional ethics throughout the entire enterprise workforce.
- Security Architecture and Engineering Mastery: This domain teaches you how to design and implement secure systems from the ground up, using principles like Bell-LaPadula and Biba models while integrating advanced cryptography to protect data at rest and in transit.
- Identity and Access Management (IAM): You get a deep understanding of how to manage user identities, implement multi-factor authentication (MFA) at scale, and use federated identity systems to ensure only the right people have access to critical company resources at all times.
- Communication and Network Security: The course dives into the design and protection of network infrastructures, teaching you how to secure wireless networks, implement software-defined networking, and defend against complex network-based attacks using modern transmission security protocols.
- Software Development Security Integration: You will learn how to integrate security into the entire software development lifecycle (SDLC), ensuring that applications are built with security-by-design principles and are tested rigorously for vulnerabilities before they are ever deployed to production.
Why it matters: The CISSP remains the ultimate credential for senior roles in 2026, as it proves you have both the technical depth and the managerial foresight to lead security teams in a complex, global threat environment.
3. Offensive Security Certified Professional+ (OSCP+)
The OSCP+ is the industry's most famous "hands-on" penetration testing certification, known for its grueling 24-hour exam that requires you to actually hack into systems. Unlike multiple-choice exams, the OSCP+ forces you to prove you can find and exploit vulnerabilities in a real network environment. The updated 2026 version now includes mandatory Active Directory exploitation, reflecting the current reality of corporate network breaches and how attackers move laterally.
- Mandatory Active Directory Exploitation: The updated curriculum requires you to demonstrate advanced skills in Kerberoasting, Pass-the-Hash, and domain privilege escalation, which are the primary methods used by real attackers to take over entire corporate networks in the modern era.
- Real-World Penetration Testing Methodology: You will learn a structured approach to reconnaissance, vulnerability research, and exploitation, ensuring you can systematically identify and document security flaws in any given target system or network while following professional standards.
- Privilege Escalation Techniques: The course provides deep training on how to move from a low-privilege user to a full system administrator on both Linux and Windows, a critical skill for understanding how hackers gain total control over an organization’s infrastructure.
- Custom Exploit Development Basics: You will learn how to modify existing exploit code to fit specific targets, giving you the ability to bypass security controls that standard automated hacking tools often fail to penetrate during a professional security audit.
- Rigorous 24-Hour Exam Format: The certification is earned through a live, proctored exam where you must complete multiple tasks and write a professional-grade technical report within a strict time limit to prove your competency under real-world pressure.
Why it matters: In a 2026 job market saturated with "paper-certified" individuals, the OSCP+ proves you have the actual technical skills to perform high-level security audits and protect organizations from real-world cyber threats.
4. CISM: Certified Information Security Manager (ISACA)
If your goal is to transition from a technical role into a management position, the CISM is your best bet. It focuses less on how to configure a firewall and more on how to manage a security team and align a security program with business objectives. In 2026, it is highly valued by C-suite executives because it produces leaders who understand risk appetite, budget constraints, and the legal implications of data breaches.
- Information Security Governance Frameworks: You will learn how to develop and maintain an information security governance framework that aligns with business goals and complies with complex international laws like GDPR and the latest US state-level privacy acts.
- Information Risk Management Strategies: This course teaches you how to identify, evaluate, and manage security risks to an acceptable level based on the organization’s risk appetite, ensuring that security investments are prioritized where they are needed most.
- Security Program Development and Management: You will gain the skills to design and oversee a comprehensive security program, managing internal staff and external vendors while ensuring that security technologies are integrated effectively into the business process.
- Incident Management and Response Planning: The curriculum covers the creation and management of an incident response capability, teaching you how to lead a team through a crisis, minimize business disruption, and conduct post-incident reviews for continuous improvement.
- Business Continuity and Disaster Recovery: You will learn how to develop strategies to ensure the business can continue to operate during a major disruption and how to restore critical systems and data quickly after a catastrophic event or cyberattack.
Why it matters: CISM is the premier choice for 2026 professionals who want to lead. It bridges the gap between technical security and business leadership, making you an essential asset to any executive board or management team.
5. CCSP: Certified Cloud Security Professional (ISC2)
With the vast majority of enterprise data now stored in the cloud, the CCSP has become one of the most critical certifications for 2026. It was designed to address the unique challenges of securing cloud environments, where traditional perimeter defenses no longer apply. This course covers everything from cloud architecture and design to data security and the legal requirements of hosting data in different jurisdictions around the world.
- Cloud Data Security and Encryption: You will learn how to implement advanced data protection strategies, including tokenization, masking, and sophisticated encryption key management, to ensure that sensitive information remains secure regardless of where it is stored in the cloud.
- Cloud Platform and Infrastructure Security: This domain focuses on securing the physical and virtual components of the cloud environment, teaching you how to implement secure network configurations, protect hypervisors, and manage the security of cloud-native services.
- Cloud Application Security and DevSecOps: You will gain expertise in securing the entire software development lifecycle for cloud applications, learning how to integrate security testing into automated pipelines and protect APIs from modern web-based threats.
- Cloud Security Operations Management: The course covers the day-to-day management of cloud environments, including security monitoring, incident response, and the implementation of automated security controls to maintain a robust and resilient cloud posture.
- Legal, Risk, and Compliance in the Cloud: You will navigate the complex world of international data privacy laws and learn how to manage the legal risks associated with cloud computing, including contract management and multi-jurisdictional compliance requirements.
Why it matters: As organizations continue their "cloud-first" migration in 2026, the CCSP ensures you are capable of securing these highly complex and dynamic environments, making you a highly specialized and well-paid professional.
6. CompTIA Security+ (SY0-701)
CompTIA Security+ is the definitive entry-point for anyone looking to start a career in information security, often acting as a prerequisite for government and defense contractor roles in the USA. The latest SY0-701 version focuses heavily on the "how-to" of security, covering everything from threat intelligence and risk management to the basics of cryptography. It is widely recognized by employers across the country as the baseline standard for anyone working in an IT environment.
- Comprehensive Threat and Vulnerability Analysis: You will learn how to identify various types of malware, social engineering attacks, and network-based threats, allowing you to recommend and implement the most effective countermeasures for any specific business environment.
- Security Operations and Incident Response Basics: The course covers the foundational steps of detecting and responding to security incidents, ensuring you know how to use monitoring tools to catch anomalies and follow a structured recovery plan after a breach.
- Identity and Access Management (IAM) Implementation: You get a deep understanding of how to manage user permissions, implement multi-factor authentication (MFA), and use directory services to secure sensitive data from unauthorized internal and external access attempts.
- Governance, Risk, and Compliance Standards: It introduces you to the essential laws and regulations governing data security, teaching you how to conduct basic risk assessments and ensure your organization meets its legal and ethical security obligations.
- Architecture and Design Security Principles: You will learn how to design secure network infrastructures, including the use of firewalls, VPNs, and secure cloud configurations, while ensuring that physical security controls are in place to protect hardware assets.
Why it matters: For anyone starting their journey in 2026, Security+ is the most efficient way to prove you have the foundational knowledge required for a career in cybersecurity, opening doors to thousands of entry-level job opportunities.
7. Certified Ethical Hacker (CEH v13) AI-Powered
EC-Council’s CEH remains one of the most popular certifications for ethical hackers, and the v13 update is revolutionary because it integrates AI-driven hacking methodologies. This course teaches you how to use artificial intelligence to automate vulnerability scanning and create intelligent phishing campaigns, which is exactly how modern hackers are operating. It is a comprehensive program that covers the entire "kill chain" of an attack, from initial reconnaissance to covering your tracks.
- AI-Powered Vulnerability Assessment: You will learn how to use machine learning algorithms to scan massive network environments for vulnerabilities at lightning speed, identifying weaknesses that traditional manual or simple automated tools would likely miss.
- Advanced Social Engineering and Phishing: This domain teaches you how to create highly personalized and convincing phishing attacks using AI tools, allowing you to test an organization's human defenses against the most modern and deceptive social engineering tactics.
- Cloud and IoT Hacking Techniques: The course provides specialized training on how to identify and exploit vulnerabilities in cloud infrastructures and Internet of Things (IoT) devices, which are becoming the primary targets for attackers in 2026.
- Mobile Platform and Web Application Security: You will gain the skills to audit mobile apps and complex web applications for security flaws, learning how to use proxies, debuggers, and specialized scanners to find injection and broken authentication vulnerabilities.
- Incident Response and Forensic Awareness: While primarily an offensive course, CEH teaches you the steps attackers take to hide their presence, giving you the knowledge needed to help incident responders find and eradicate threats from a compromised system.
Why it matters: CEH v13 is unique in 2026 for its focus on AI-assisted hacking, making you a defender who truly understands the next generation of threats and how to use the same technology to build better defenses.
8. CompTIA Cybersecurity Analyst (CySA+)
The CySA+ is an intermediate-level certification that focuses on the defensive side of cybersecurity, specifically the role of a security analyst. In 2026, when "threat hunting" is a standard practice, this course is vital for learning how to use behavioral analytics to spot attackers who have bypassed traditional security measures. It is a highly practical certification that bridges the gap between foundational security and advanced incident response.
- Proactive Threat Hunting and Intelligence: You will learn how to gather and analyze threat intelligence data to proactively search for indicators of compromise (IoCs) within your network, catching threats before they can escalate into a major breach.
- Vulnerability Management and Remediation: This course teaches you how to design and manage a comprehensive vulnerability management program, including scanning, prioritizing findings based on risk, and coordinating with IT teams to apply patches and fixes.
- Advanced Security Operations (SecOps): You will gain expertise in using SIEM and SOAR platforms to monitor network traffic, analyze logs, and automate the response to common security alerts, significantly reducing the "dwell time" of attackers in your environment.
- Incident Response and Digital Forensics: The curriculum covers the entire incident response lifecycle, teaching you how to contain threats, perform forensic analysis of compromised systems, and document your findings for legal and regulatory compliance.
- Compliance and Reporting for Security Teams: You will learn how to translate technical security data into professional reports for management and auditors, ensuring that the organization’s security posture is clearly communicated to all stakeholders.
Why it matters: As companies in 2026 focus more on detection and response, CySA+ provides the exact skills needed to be a high-performing member of a Security Operations Center (SOC) or a dedicated incident response team.
9. GIAC Certified Incident Handler (GCIH)
The GCIH is one of the most respected certifications for those who are on the front lines when an attack happens. It teaches you how to manage the entire incident handling process using the PICERL (Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned) framework. In 2026, this certification is critical because it ensures that responders can handle high-pressure situations without making mistakes that could lead to data loss or legal liability.
- Hacker Tools and Techniques Mastery: You will learn exactly how attackers use tools like Nmap, Metasploit, and Netcat to breach systems, giving you the "adversary mindset" needed to effectively detect and stop their progress during a live incident.
- Computer Crime Investigation and Forensics: This domain teaches you how to collect and preserve digital evidence while maintaining a proper chain of custody, ensuring that your findings are legally sound and can be used in a court of law if necessary.
- Incident Handling Process (PICERL): You will master the six-step PICERL framework, learning how to lead a response team from the initial detection of an anomaly through to the final "lessons learned" report that helps prevent future attacks.
- Memory and Network Forensics: The course provides deep-dive training on how to analyze a computer's volatile memory and capture network traffic to find "living off the land" attackers who don't leave traces on a hard drive.
- Malware Analysis and Sandbox Testing: You will learn how to safely analyze suspicious files in a controlled environment to understand their behavior, determine their origin, and create custom signatures to block similar threats in the future.
Why it matters: When a major breach hits in 2026, companies want a GCIH-certified professional leading the charge. It proves you have the technical skills and the leadership ability to save an organization from total disaster.
10. Microsoft Certified: Cybersecurity Architect Expert (SC-100)
For those working in the massive Microsoft ecosystem, the SC-100 is the ultimate architectural credential. It focuses on designing a Zero Trust security strategy that spans identity, devices, applications, and data across both cloud and hybrid environments. In 2026, with the widespread use of Microsoft 365 and Azure, this certification is essential for anyone responsible for the high-level design of an enterprise's digital defenses.
- Zero Trust Security Strategy Design: You will learn how to design a comprehensive Zero Trust architecture that assumes every access request is a potential threat, requiring continuous verification of identity, device health, and context before granting access.
- Governance, Risk, and Compliance (GRC) Integration: This course teaches you how to align your Microsoft security architecture with industry standards like ISO 27001 and NIST, ensuring that your technical controls also meet the legal requirements of your business.
- Security Operations and Threat Response Architecture: You will gain expertise in designing modern Security Operations Centers using Microsoft Sentinel and Microsoft Defender XDR, automating the detection and response to threats across the entire enterprise.
- Securing Data and Applications in Azure: The curriculum covers the design of secure data storage and application environments in the Microsoft cloud, including the use of encryption, private links, and advanced identity protection to prevent unauthorized access.
- Hybrid and Multi-Cloud Security Strategy: You will learn how to extend your Microsoft security architecture to protect resources in other clouds (like AWS or Google) and in on-premises data centers, creating a unified and consistent defense strategy.
Why it matters: In 2026, most US enterprises run on Microsoft. Being an "Architect Expert" means you are the person who designs the blueprint for their safety, making you one of the most valuable people in the IT department.
11. eLearnSecurity Junior Penetration Tester (eJPTv2)
The eJPTv2 has quickly become a favorite for those who find the OSCP+ too daunting but want something more hands-on than the CEH. It is a 100% practical exam that simulates a real penetration test of a corporate network. By the time you finish the course, you will have a solid understanding of how to conduct a professional security audit, from scanning for open ports to exploiting web application vulnerabilities and writing a final report.
- Information Gathering and Reconnaissance: You will learn both passive and active reconnaissance techniques to gather information about a target network, including subdomain enumeration, technology profiling, and identifying open services and hidden files.
- Vulnerability Assessment and Verification: This domain teaches you how to use professional scanners to find security flaws and, more importantly, how to manually verify those findings to eliminate false positives and understand the true risk to the business.
- Host and Network Penetration Testing: You get hands-on experience exploiting vulnerabilities in both Windows and Linux systems, learning how to use the Metasploit Framework and custom scripts to gain access and move laterally through a network.
- Web Application Hacking Basics: The course covers the most common web-based attacks, including SQL injection, cross-site scripting (XSS), and broken authentication, ensuring you can audit a company's web presence for security weaknesses.
- Post-Exploitation and Reporting Skills: You will learn what to do after you've gained access, including privilege escalation and credential harvesting, and how to document all your findings in a professional report that a client can actually use.
Why it matters: The eJPTv2 is the best "bridge" certification in 2026. it moves you past the "beginner" stage and proves to employers that you can actually use the tools of the trade in a real-world scenario.
12. AWS Certified Security – Specialty (SCS-C03)
As Amazon Web Services (AWS) continues to dominate the cloud market in the USA, the AWS Security Specialty remains a high-ROI certification for 2026. This course is laser-focused on the deep technical aspects of securing an AWS environment, including the proper use of IAM policies, key management services (KMS), and automated incident response using Lambda and EventBridge. It is designed for engineers who are actually building and maintaining cloud infrastructure every day.
- Advanced Identity and Access Management (IAM): You will master the creation of complex IAM policies, including the use of Service Control Policies (SCPs) and permissions boundaries to implement the principle of least privilege across thousands of cloud resources.
- Infrastructure Security and Network Protection: This course teaches you how to design secure VPC architectures, use AWS WAF to protect web applications, and implement automated DDoS protection using AWS Shield to keep your cloud services available.
- Data Protection and Encryption Modeling: You will learn how to use AWS Key Management Service (KMS) and CloudHSM to manage encryption keys and protect data at rest and in transit across all AWS storage and database services effectively.
- Logging, Monitoring, and Threat Detection: The curriculum covers the use of AWS CloudTrail, CloudWatch, and Amazon GuardDuty to monitor your environment for suspicious activity and generate actionable alerts for your security team to investigate.
- Automated Incident Response in the Cloud: You will gain the skills to use AWS Lambda and EventBridge to create "self-healing" security architectures that can automatically isolate compromised instances and remediate security misconfigurations in real-time.
Why it matters: If you work in an AWS environment in 2026, this certification is non-negotiable. It proves you have the specialized technical depth required to protect an organization's most valuable cloud-native assets.
13. Palo Alto Networks Certified Network Security Engineer (PCNSE)
Palo Alto Networks is the leader in the Next-Generation Firewall (NGFW) market, and the PCNSE is the gold standard for anyone managing their devices. In 2026, where the "network perimeter" has evolved into a complex mesh of cloud and on-premises sites, this certification ensures you can design and troubleshoot a unified security platform. It covers everything from firewall configuration to advanced threat prevention and secure remote access.
- NGFW Design and Deployment Strategies: You will learn how to design and install Palo Alto Networks firewalls in a variety of complex environments, including high-availability clusters and integrated cloud deployments for enterprise-wide protection.
- Advanced Threat Prevention and Sandboxing: This course teaches you how to configure WildFire and other advanced security services to detect and block zero-day exploits, sophisticated malware, and command-and-control traffic in real-time.
- GlobalProtect and Secure Remote Access: You get deep-dive training on how to implement GlobalProtect to provide secure, encrypted access for remote workers, ensuring that the same security policies are applied regardless of where a user is located.
- Network Security Management with Panorama: The curriculum covers the use of Panorama for centralized management of hundreds of firewalls, allowing you to deploy consistent security policies, manage updates, and analyze logs from a single pane of glass.
- Troubleshooting and Performance Optimization: You will gain the technical skills to identify and resolve complex network and security issues, ensuring that your firewalls are performing at peak efficiency without introducing latency into the business network.
Why it matters: Palo Alto firewalls are the backbone of many US corporate networks in 2026. Being PCNSE certified makes you an indispensable expert for any organization that relies on their technology for its primary defense.
14. Fortinet NSE 8 (Fortinet Certified Expert)
The NSE 8 is the highest level of certification in the Fortinet ecosystem and is widely considered one of the most difficult technical exams in the world. It consists of a written exam followed by a grueling practical lab where you must design, configure, and troubleshoot a massive "Security Fabric" environment. In 2026, this certification is the hallmark of a true master of network security architecture and enterprise-grade defense systems.
- Fortinet Security Fabric Architecture: You will learn how to integrate a wide range of Fortinet products into a single, cohesive security fabric that shares threat intelligence and automates the response to attacks across the entire network.
- Expert-Level Troubleshooting and Analysis: The course and exam require you to solve complex, real-world technical problems across firewalls, switches, wireless controllers, and advanced security appliances under strict time constraints to prove your mastery.
- High-Performance Infrastructure Design: You get advanced training on designing resilient and scalable network architectures for the largest enterprises, ensuring that security never becomes a bottleneck for business operations or data flow.
- Advanced Routing and Switching Integration: This domain focuses on the deep integration of security services with advanced networking protocols, ensuring that your security posture is robust even in the most complex and dynamic network environments.
- Security Automation and Orchestration Mastery: You will learn how to use FortiManager and FortiAnalyzer to automate repetitive tasks and gain deep insights into network security events, allowing you to manage large-scale deployments with minimal manual effort.
Why it matters: Holding an NSE 8 in 2026 puts you in an elite group of professionals globally. It is a powerful signal to the largest corporations in the USA that you are a world-class expert capable of managing their most complex security challenges.
15. CISA: Certified Information Systems Auditor (ISACA)
While most of the courses on this list focus on building and defending, the CISA focuses on auditing and controlling. In 2026, with the increasing weight of government audits and compliance requirements (like SOC 2 and ISO 27001), CISA-certified professionals are in higher demand than ever. This course teaches you how to systematically evaluate an organization’s IT systems to ensure they are secure, efficient, and legally compliant.
- Information System Auditing Process: You will learn the professional standards and methodologies for conducting a comprehensive IT audit, from initial planning and risk assessment to the final reporting of findings to senior management.
- Governance and Management of Information Technology: This domain focuses on evaluating the leadership and organizational structures of an IT department, ensuring that they align with business goals and effectively manage IT-related risks.
- Information Systems Acquisition and Development: You will gain the skills to audit the process of how a company buys or builds new software and hardware, ensuring that security and efficiency are considered at every stage of the project.
- Information Systems Operations and Business Resilience: The course teaches you how to evaluate the day-to-day operations of an IT environment, including the effectiveness of backup procedures, disaster recovery plans, and incident response capabilities.
- Protection of Information Assets Auditing: You will learn how to audit the technical and administrative controls used to protect sensitive data, ensuring that encryption, access management, and physical security are all functioning as intended.
Why it matters: In 2026, security is not just about the "how" but also the "proof." CISA-certified professionals provide the independent verification that a company’s security claims are true, making them vital for trust and legal compliance.
One of the biggest challenges in the 2026 job market is that everyone has certifications, but very few people have actual proof that they can do the work. This is exactly where Fueler comes in. Instead of just listing a course on your LinkedIn, Fueler allows you to showcase the actual projects, lab reports, and security audits you completed during these courses. By building a skills-first portfolio on Fueler, you can show hiring managers the tangible evidence of your cybersecurity expertise, helping you stand out from a sea of applicants who only have a certificate to show.
Final Thoughts
The path to a successful cybersecurity career in 2026 is no longer about collecting as many random certificates as possible. It is about choosing the right specialized path, whether that is cloud security, management, or penetration testing, and backing that education up with a strong portfolio of real-world work. The 15 courses listed above represent the best of the best in the USA today, offering both the theoretical knowledge and the industry respect you need to climb the professional ladder. Start with one, master it, and never stop learning, because the threats we face are always evolving.
FAQs
What is the best cybersecurity course for beginners in 2026?
For absolute beginners, the Google Cybersecurity Professional Certificate or CompTIA Security+ are widely considered the best option. They provide a broad foundation without requiring years of prior experience, making them ideal for those starting from scratch.
Which cybersecurity certification offers the highest salary in the USA?
While salaries vary by experience and location, advanced certifications like the CISSP, CCSP, and OSCP+ consistently lead to the highest-paying roles, with many professionals in 2026 earning well over $150,000 annually.
Do I need a degree to get hired in cybersecurity in 2026?
No, a degree is becoming less mandatory as the industry shifts toward a "skills-first" hiring model. Most top tech firms now value professional certifications and a strong portfolio of projects (like a Fueler profile) over a traditional four-year college degree.
How long does it take to get a cybersecurity certification?
The timeline varies significantly; a foundational cert like Security+ can take 1 to 3 months of study, while an advanced credential like the CISSP or the practical NSE 8 can take 6 months to a year of dedicated preparation and experience.
Are free cybersecurity courses worth it for my career?
Yes, free courses from platforms like Coursera (audit mode) or Cybrary are excellent for gaining knowledge, but for professional hiring, you usually need the paid certificate to pass through automated resume filters and prove your commitment to the field.
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.