7 Top AI Cybersecurity Tools for Canadian Companies

Riten Debnath
24 Apr, 2026

Last updated: April 2026
If you think your small business in Canada is too small to be a target, you are essentially leaving your front door wide open in a digital blizzard. Cyber threats today don't care if you are a massive corporation in Toronto or a growing startup in Kelowna; they just want a way in. Relying on "common sense" alone is no longer a security plan; it is a liability. You need hard, organic tools that build a wall around your data without relying on the hype of trendy buzzwords.
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
At a glance: Comparing the Top AI Cybersecurity Tools for Canadian Companies
1. Bitdefender GravityZone
Best for growing Canadian businesses that need high-performance endpoint protection with a very low system impact.
Bitdefender is widely respected for its "quiet efficiency." It provides a unified security platform that covers laptops, desktops, and servers without slowing them down to a crawl. For a business owner who wants protection that doesn't get in the way of daily operations, GravityZone offers a "set and forget" experience that consistently ranks at the top of independent security tests for its raw detection power.
- Layered Next-Gen Protection Architecture: This system uses multiple layers of security, including advanced behavioral monitoring and process inspection, to catch threats that traditional antivirus software might miss by looking for suspicious activity rather than just known bad files.
- Unified Security Management Console: You can manage all your devices from a single, cloud-based dashboard, which gives you a clear view of your company's security health and allows you to push updates or run scans across your entire team with just a few clicks.
- Advanced Ransomware Mitigation Engine: This specialized feature creates instant backups of your most important files the moment it detects a potential ransomware attack, allowing you to restore your data immediately if a malicious process tries to encrypt your hard drive.
- Network Attack Defense Layer: This acts as a protective shield for your network, identifying and blocking specialized attacks like brute-force attempts and password stealers before they can even gain a foothold in your internal office environment.
- Phishing and Web Security Filters: The tool automatically scans web traffic and emails to block fraudulent websites that try to steal your login credentials, ensuring your team doesn't accidentally hand over the keys to your company's financial accounts.
Pricing: Business Security starts at $184.99 per year for 5 devices, while Premium tiers for larger deployments start at $409.99 per year.
Why it matters
It protects your productivity. In the Canadian market, time is money, and Bitdefender ensures your team stays safe without the constant "system update" lag that plagues cheaper, less organic security solutions.
2. NordLayer
Best for Companies with remote or hybrid teams that need secure, encrypted access to internal company resources.
NordLayer is the business-grade evolution of the VPN technology you likely already know. It is designed specifically for teams that need to work from coffee shops, home offices, or client sites across Canada without exposing company data to public Wi-Fi risks. It creates a private tunnel for your data, making it essentially invisible to hackers lurking on open networks.
- Zero Trust Network Access (ZTNA): This security model ensures that every user and device must be verified before they can access specific parts of your network, meaning a breach on one employee's laptop won't automatically lead to a total company-wide data leak.
- Military-Grade AES 256-bit Encryption: All data moving between your employees' devices and your company servers is scrambled using the world's most secure encryption standard, making it impossible for third parties to read your sensitive business communications or documents.
- Smart Remote Access Gateways: You can set up dedicated servers in specific geographic locations, allowing your team to access region-locked Canadian government or financial portals securely even if they are traveling for business outside of the province.
- Centralized Member Management: The admin panel allows you to instantly add or remove team members, reset passwords, and monitor connection logs, giving you total control over who is accessing your business data at any given second of the day.
- Auto-Connect and Threat Block: This feature ensures that your employees are always protected by automatically connecting the VPN the moment they turn on their device, while simultaneously blocking known malicious websites and intrusive advertisements.
Pricing: Lite plan starts at $8.00 per user/month, while the Core plan is $11.00 per user/month and the Premium tier is $14.00 per user/month (billed annually).
Why it matters
It secures "Remote Reality." With more Canadians working away from the office, NordLayer ensures that your "office perimeter" exists wherever your employees happen to be sitting with their laptops.
3. Malwarebytes for Business
Best for Quick remediation and a lightweight secondary layer of defense against aggressive malware and ransomware.
Malwarebytes has long been the "secret weapon" for IT professionals because of its ability to find and kill infections that other software leaves behind. For a Canadian business, it serves as a powerful, lightweight guard that focuses specifically on the most dangerous threats like zero-day exploits and ransomware that can cripple a company's operations in minutes.
- Signature-less Behavioral Analysis: Instead of just looking for a list of known viruses, this tool monitors how programs behave on your computer, allowing it to stop brand-new, never-before-seen "zero-day" attacks before they can execute their malicious code.
- Ransomware Rollback Technology: If an infection manages to encrypt your files, Malwarebytes can actually roll back the changes to a healthy state within a 72-hour window, effectively acting as a time machine for your most critical business data and documents.
- Brute Force Protection for RDP: This feature specifically guards against hackers trying to guess your passwords to gain remote control of your computers, which is one of the most common ways small businesses in Canada get compromised.
- Vulnerability Assessment and Patching: The software automatically scans your installed apps for security holes and warns you if you are running outdated software that needs to be updated to prevent hackers from exploiting known weaknesses in your system.
- Cloud-Native Nebula Platform: All security events and device statuses are reported to a single, easy-to-navigate cloud dashboard, allowing you to manage your entire fleet of computers without needing to maintain an expensive on-premise server.
Pricing: Standard Business plans start at $69.99 per endpoint/year (5-device minimum), with Advanced EDR plans starting around $79.99 per endpoint/year.
Why it matters
It provides a safety net. Even if a threat gets past your first line of defense, Malwarebytes is the specialized tool that ensures it doesn't stay there long enough to cause permanent financial or reputational damage.
4. Sophos Intercept X
Best for Organizations that want high-end exploit prevention and detailed forensic reporting on security incidents.
Sophos is a powerhouse in the world of professional security, known for its "Intercept X" technology that focuses on stopping the techniques hackers use, rather than just the files they send. It’s a sophisticated tool for Canadian companies that want to understand not just that they were attacked, but how it happened and how to stop it from ever happening again.
- Deep Learning Malware Detection: This organic detection engine uses a massive neural network to analyze the "DNA" of files before they run, allowing it to identify malicious code with incredible accuracy without the need for constant, bulky database updates.
- Anti-Exploit Technology Layer: This feature identifies the common "tricks" used by hackers to hijack legitimate software (like your web browser or PDF reader), effectively breaking the attack chain before the malicious actor can gain control of the operating system.
- CryptoGuard Ransomware Shield: Sophos monitors your file system for the unauthorized encryption of data and, upon detection, it instantly shuts down the malicious process and reverts the affected files to their original, unencrypted state automatically.
- Root Cause Analysis (Forensics): When an attack is blocked, Sophos provides a detailed visual map showing exactly where the threat came from, what it tried to touch, and how it was stopped, giving your team the insights needed to harden your defenses.
- Synchronized Security Heartbeat: If you use other Sophos products, they "talk" to each other in real-time, meaning if a laptop gets infected, your firewall can automatically isolate that specific device from the rest of the network to prevent the spread.
Pricing: Estimated pricing starts at $28.00 per user/year for Intercept X Advanced, while Advanced with XDR starts around $48.00 per user/year.
Why it matters
It offers professional-grade visibility. For a growing company, knowing the "why" behind a security event is just as important as stopping it, and Sophos provides the data you need to make informed long-term security decisions.
5. Check Point Harmony
Best for Total protection across the board, including mobile devices, email, and endpoint security in one package.
Check Point is one of the oldest and most respected names in cybersecurity. Their Harmony suite is designed to be a "complete" solution that covers every possible way a hacker could get into your business. From the smartphone in your pocket to the email in your inbox, Check Point provides a unified wall of protection that is trusted by some of the largest organizations in the world.
- Complete Mobile Threat Defense: This extends your company's security to employee smartphones, protecting against malicious apps, unsecure Wi-Fi networks, and OS-level vulnerabilities that are often overlooked in traditional business security plans.
- Advanced Email and Office Security: Harmony scans all incoming email attachments and links in real-time, removing "active content" like malicious macros from documents before they ever reach your employees' inboxes to prevent phishing and malware delivery.
- Endpoint Detection and Response (EDR): The tool provides continuous monitoring of all activities on your computers, allowing your security team to hunt for "hidden" threats and respond to complex attacks with automated cleanup and quarantine protocols.
- Zero-Phishing Protection Layer: This feature uses real-time scanning to identify and block new phishing sites as they are created, preventing your team from entering their credentials into fake login pages designed to look like Microsoft 365 or your bank.
- Secure Web Browsing and Access: It ensures that your employees can only access safe parts of the internet by filtering out malicious categories and preventing the download of dangerous file types, keeping your company's web traffic clean and compliant.
Pricing: Harmony Endpoint typically ranges from $40.00 to $150.00 per seat/year depending on the complexity of the bundle and the number of users.
Why it matters
It provides total coverage. Instead of buying five different tools for five different problems, Check Point Harmony gives you one organic system that covers your entire digital footprint from top to bottom.
6. Kali Linux (for Auditing)
Best for Technical business owners or IT staff who want to perform their own "stress tests" on their company network.
Kali Linux is not a "protection" tool in the traditional sense; it is a professional penetration testing suite. It is a free, open-source operating system loaded with over 600 tools used by security professionals to find the holes in their own armor. For a Canadian company with a dedicated IT person, using Kali is the best way to "think like a hacker" and fix problems before the bad guys find them.
- Massive Library of Security Tools: Kali comes pre-installed with legendary tools like NMAP for network scanning, Wireshark for packet analysis, and Metasploit for testing how vulnerable your systems are to specific, real-world exploits.
- Full Network Vulnerability Scanning: You can use the built-in tools to scan your office network and find devices that have weak passwords, open ports, or outdated software that could serve as an easy entry point for a cybercriminal.
- Wireless Security Auditing: Kali includes specialized tools for testing the strength of your office Wi-Fi, allowing you to see if your encryption is easy to crack or if your guest network is properly isolated from your sensitive business data.
- Password Strength Assessment: You can run "brute-force" simulations against your own internal systems to identify which employees are using weak or easily guessable passwords, helping you enforce better security habits across the entire company.
- Forensic and Recovery Tools: Beyond just attacking, Kali includes powerful tools for investigating a breach after it happens, allowing you to recover deleted files and see exactly what a hacker did while they were inside your system.
Pricing: Completely Free and open-source.
Why it matters
It puts you on the offensive. By regularly auditing your own systems with the same tools hackers use, you can identify and patch your biggest weaknesses before they are ever exploited in the real world.
7. Wireshark
Best for Deep network troubleshooting and identifying "leaky" devices that are sending data where they shouldn't.
Wireshark is the world’s most widely used network protocol analyzer. It allows you to see exactly what is happening on your network at a microscopic level. If you suspect a device in your office is infected and "calling home" to a hacker's server, Wireshark is the tool that will show you the exact data packets leaving your building.
- Live Data Capture and Offline Analysis: You can record all the traffic moving through your network in real-time and then go back and analyze it later to find patterns of suspicious activity or unauthorized data transfers.
- Microscopic Packet Inspection: Wireshark breaks down every single piece of data into a readable format, showing you the source, the destination, and the actual content of the communication, leaving no room for "hidden" malicious traffic.
- Advanced Color-Coding Rules: You can set up custom rules that highlight specific types of traffic (like encrypted data or unusual protocols) in different colors, making it much easier to spot a needle in the haystack of your daily network activity.
- Multi-Platform Support: Whether your office runs on Windows, macOS, or Linux, Wireshark can be installed and used to monitor any type of network connection, from standard Ethernet to complex wireless setups.
- Powerful Filtering System: With thousands of possible filters, you can narrow down your view to just a single device or a specific type of application, allowing you to ignore the "noise" and focus purely on the traffic that looks suspicious.
Pricing: Completely Free and open-source.
Why it matters
It provides the ultimate truth. While other tools might guess if something is wrong, Wireshark shows you the actual data packets, giving you undeniable proof of what is happening inside your company's network.
Which one should you choose?
If you are a small business looking for a solid all-rounder that won't slow down your computers, Bitdefender GravityZone is your best starting point. If you have a fully remote team, you absolutely need NordLayer to keep your connections private. For those who want the most aggressive protection against ransomware, Malwarebytes or Sophos are the top choices. However, if you have an in-house IT person who wants to take a hands-on approach to security, having them learn Kali Linux and Wireshark will give you a level of insight that no paid tool can match.
How does this connect to building a strong career or portfolio?
In the modern world, "security awareness" is a high-value skill that belongs in every professional’s portfolio. When you can show a future employer or client that you don't just "do the work," but you do it securely using professional-grade tools, your value skyrockets. This is the core of what we do at Fueler. By documenting your ability to manage these security systems or even just showing that you've implemented a "Security-First" workflow for your projects, you are providing "proof of work" that proves you are a responsible, high-level professional that companies can trust with their most sensitive data.
Final Thoughts
Cybersecurity is not an "IT problem," it is a business survival problem. For Canadian companies, the cost of being unprepared is far higher than the cost of any of these tools. By choosing organic, proven software and taking a proactive approach to your security, you aren't just protecting your data you are protecting your reputation, your customers, and your future. Pick your first tool today and start building your digital fortress.
FAQs
1. Is free antivirus software enough for a Canadian business in 2026?
No. While free tools are great for personal use, they lack the centralized management, ransomware rollback, and network-wide visibility that a business needs to protect multiple employees and sensitive customer data.
2. Do I need a VPN if my team only works from the office?
Even in an office, a VPN like NordLayer can add a layer of encryption and allow you to segment your network, ensuring that guest Wi-Fi users can't see your internal company servers or sensitive files.
3. What is the most common cyber threat for small businesses in Canada?
Currently, phishing (fake emails) and ransomware are the two biggest threats. Hackers use these to steal login credentials or lock your files until you pay a massive fee in cryptocurrency.
4. How often should I run security audits on my company network?
At a minimum, you should perform a basic scan once a month. However, tools like Bitdefender and Sophos provide "always-on" monitoring that identifies threats the second they appear, reducing the need for manual scans.
5. Are open-source tools like Kali Linux safe to use?
Yes, they are safe as long as they are downloaded from official sources. However, they are "power tools" that require significant technical knowledge to use effectively without accidentally disrupting your own network.
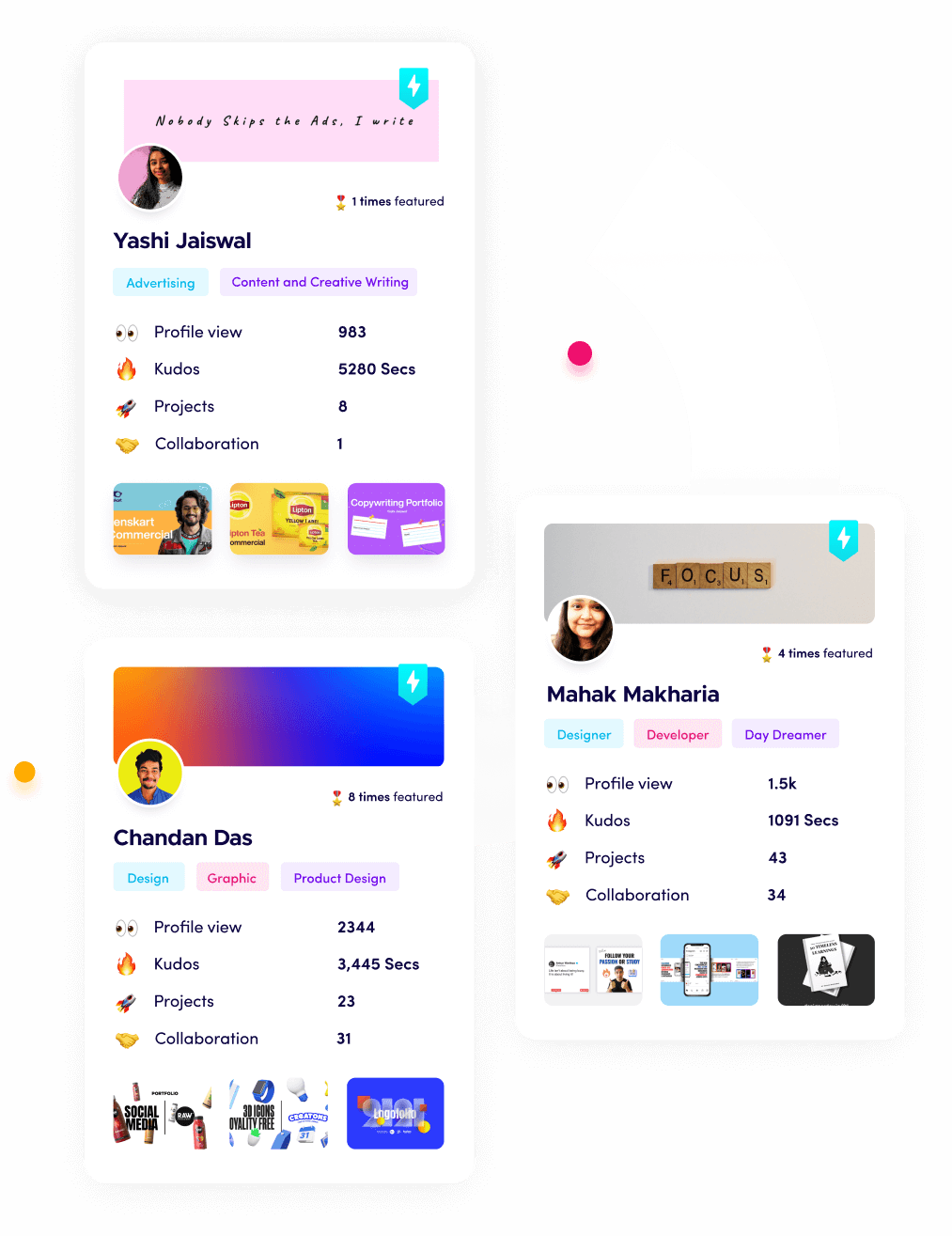
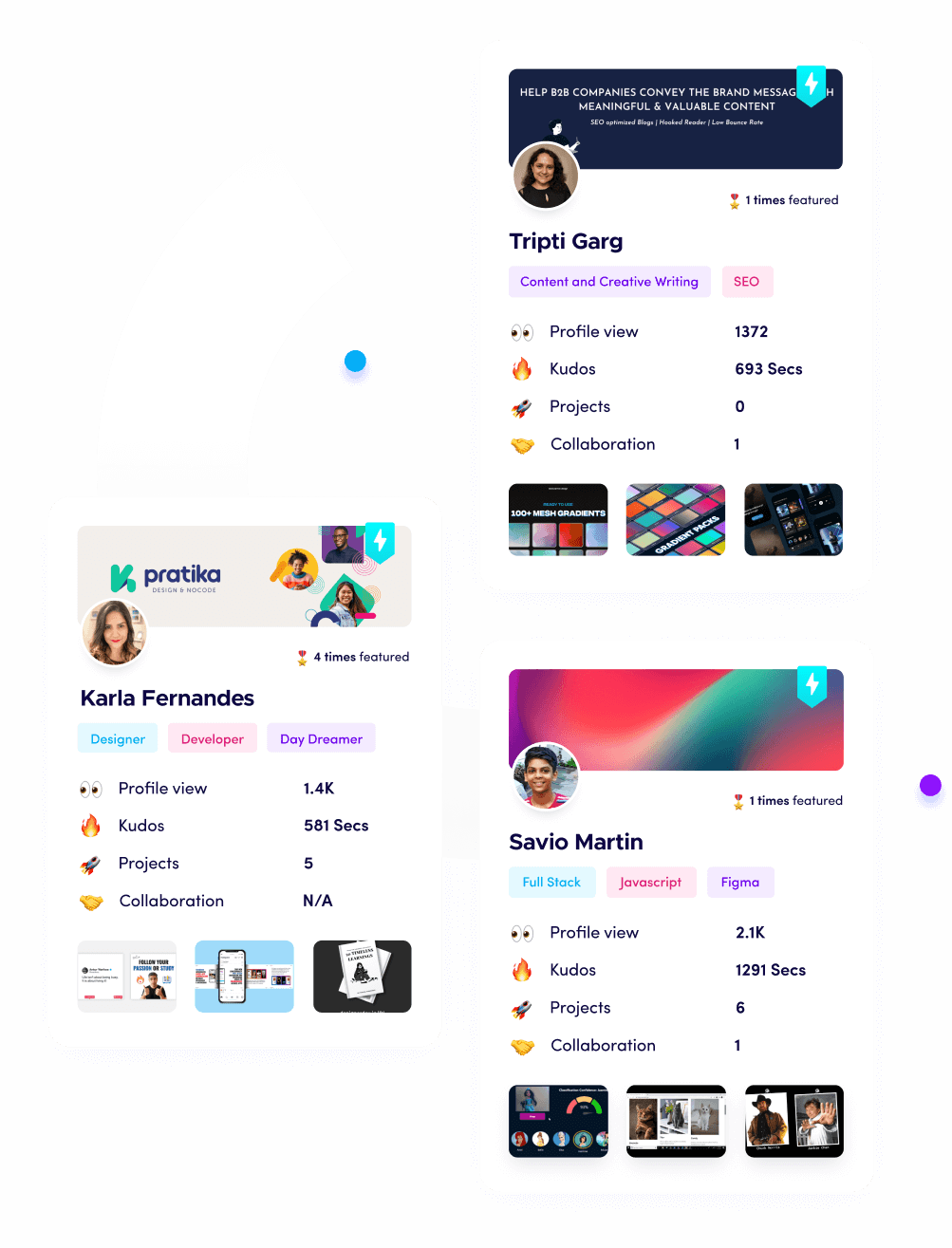
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.