7 Top AI Cybersecurity Tools Every Company Should Know

Riten Debnath
20 Apr, 2026

Last updated: April 2026
Hackers are officially using AI, and if you are still relying on a basic firewall, you are essentially bringing a butter knife to a railgun fight.
If you have been reading the news lately, you know that the "bad guys" are getting smarter by the second. They are using advanced algorithms to craft perfect phishing emails and launch automated attacks that never sleep. For a business owner or a security manager, this is terrifying. But here is the good news: the "good guys" have the same tech. In 2026, the only way to beat a machine is with a better machine. You need defensive tools that can spot a threat before it even happens, acting as a digital bodyguard that works 24/7 without a coffee break.
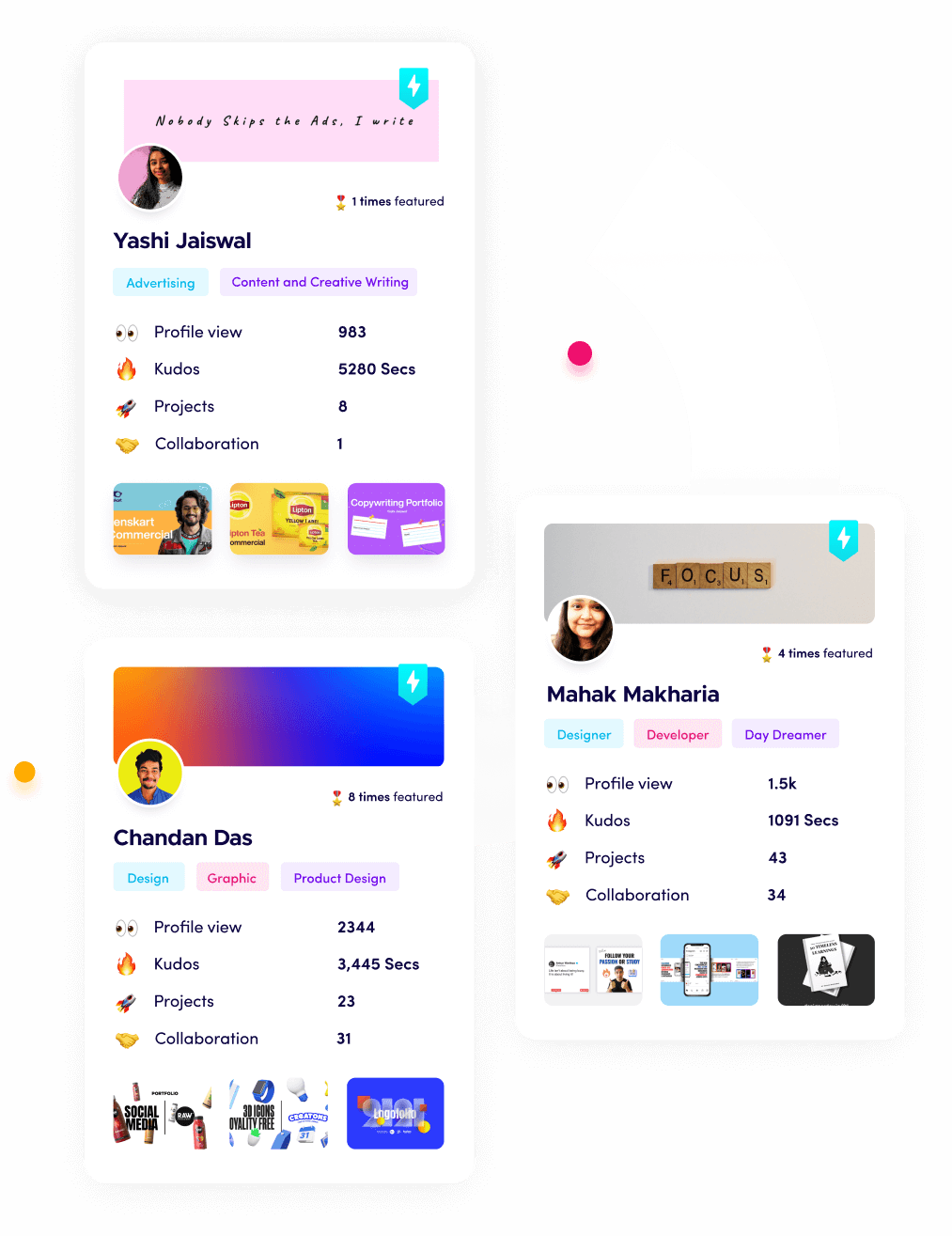
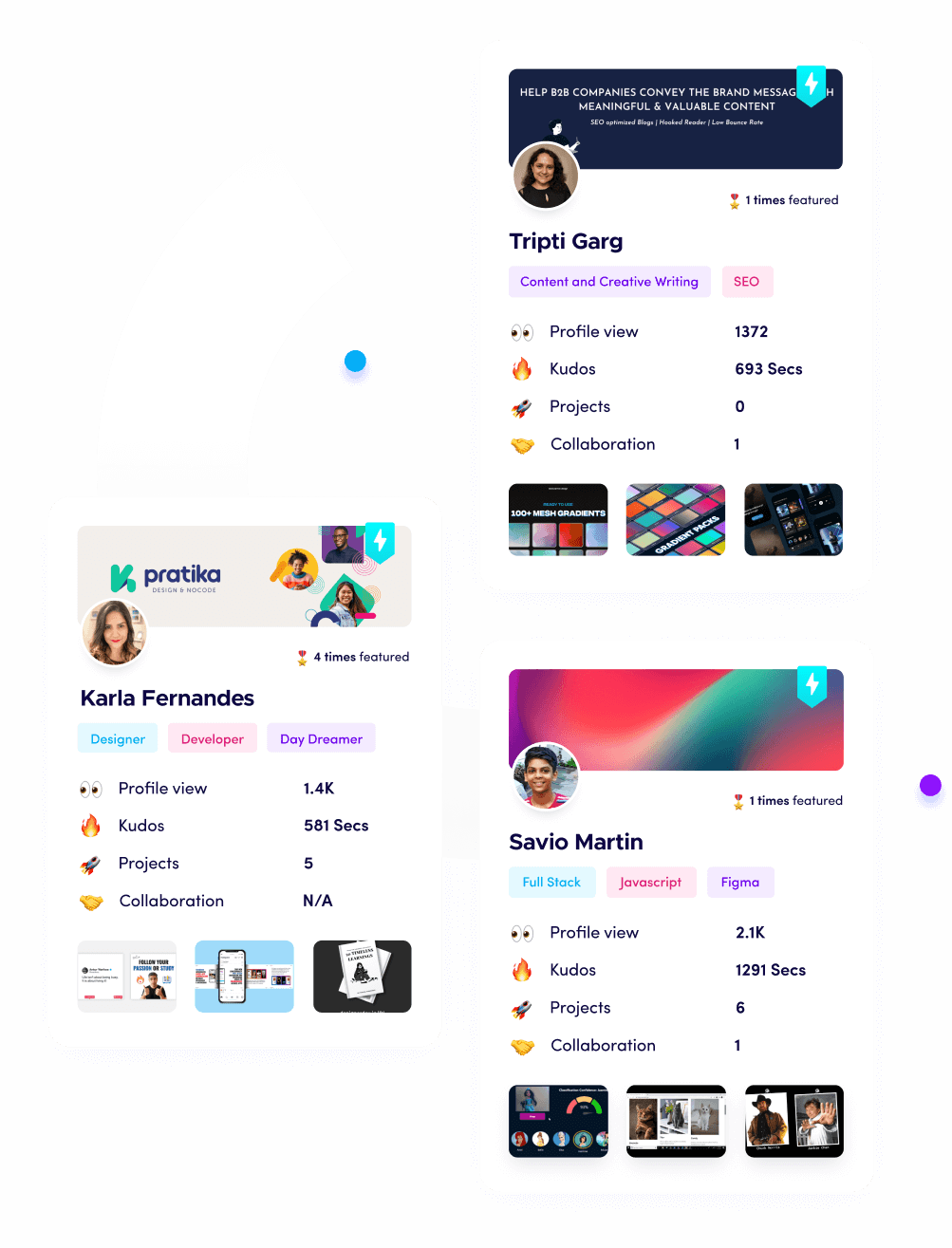
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
At a glance: Comparing the Top AI Cybersecurity Tools Every Company Should Know
1. CrowdStrike Falcon
Best for: Comprehensive endpoint protection and high-speed threat hunting.
CrowdStrike is the heavy hitter of the industry. It uses a single, lightweight agent to protect every laptop, server, and phone in your company. Its AI "brain" analyzes trillions of events every week to spot patterns that look like a breach. Instead of waiting for a virus to be "known," it looks for suspicious behavior. If an app starts acting like a hacker, Falcon shuts it down instantly. It is widely considered the gold standard for companies that cannot afford even a single minute of downtime.
Key Features:
- Behavioral Protection: It does not just look for bad files; it watches for "bad behavior," meaning it can stop brand-new attacks that have never been seen before in the wild.
- Overwatch Threat Hunting: A 24/7 team of human experts works alongside the AI to investigate any weird activity that the machine flags, giving you a human-plus-machine safety net.
- Unified Console: You can manage everything from your cloud servers to your employees' laptops from one single screen, which saves you from jumping between five different apps.
- Zero Trust Assessments: It constantly checks if a user is who they say they are before giving them access to sensitive data, which is crucial for remote teams working from home.
- Incident Response Tools: If something does go wrong, Falcon provides a detailed "flight recorder" view of exactly how the intruder got in and what they tried to touch.
Pricing:
- Falcon Go: $59.99 per device annually (Basic protection for small businesses).
- Falcon Pro: $99.99 per device annually (Includes more advanced endpoint security).
- Falcon Enterprise: $184.99 per device annually (Full threat hunting and intelligence capabilities).
Why it matters:
This tool matters because it provides "peace of mind as a service." For a company, knowing that every single device is being watched by one of the most advanced AI systems on earth allows the team to focus on growth instead of constantly checking for leaks.
2. Darktrace DETECT
Best for: Identifying "hidden" threats inside your network that others miss.
Darktrace is famous for its "Immune System" approach to security. Instead of looking at a list of bad guys, it learns what "normal" looks like for your specific company. It watches how your employees work, how data moves, and how your servers talk. If something slightly weird happens like an accountant suddenly downloading 5GB of data at 2:00 AMit flags it. It is an organic, self-learning system that evolves as your business grows, making it perfect for companies with complex, messy networks.
Key Features:
- Self-Learning AI: It starts working immediately without you having to set up thousands of rules; it simply watches and learns the "vibe" of your office's digital life.
- Autonomous Response: When it finds a threat, it doesn't just send an email; it can automatically step in to "surgically" stop the bad activity while letting normal work continue.
- Cloud and SaaS Coverage: It doesn't just watch your office Wi-Fi; it monitors your Microsoft 365, Slack, and Zoom accounts to make sure nobody is attacking you through the cloud.
- Cyber AI Analyst: This feature automatically stitches together different alerts into a single story, so you don't have to spend hours playing detective to find out what happened.
- Email Protection: It scans incoming mail for "social engineering" tricks, catching those hyper-realistic phishing emails that standard filters usually let through.
Pricing:
- Small Deployments: Roughly $50,000–$150,000 annually for a single module.
- Mid-Market: $150,000–$500,000 annually for multi-module bundles (Detect + Respond).
- Custom Enterprise: Quote-based for larger organizations (Typically starts at $50,000+ per year).
Why it matters:
Darktrace matters because hackers are becoming experts at "blending in." This tool is the only thing that can spot a wolf in sheep's clothing by noticing that the "sheep" is walking just a little bit differently than yesterday.
3. SentinelOne Singularity
Best for: High-speed automation and "one-click" threat reversal.
SentinelOne is built for speed. Its main claim to fame is the "Rollback" feature. If a piece of ransomware manages to encrypt your files, SentinelOne can literally "undo" the damage with one click, restoring your files to exactly how they were before the attack. It uses a very aggressive AI that lives directly on the device, meaning it can stop an attack even if the computer is not connected to the internet. It is highly popular with tech-savvy companies that want a very fast, automated response system.
Key Features:
- One-Click Rollback: This is a literal "time machine" for your files; if you get hit by ransomware, you can revert the changes and go back to work in minutes.
- Offline Protection: Because the AI lives on the laptop itself, it doesn't need a cloud connection to stay smart, which is perfect for travelers or people in areas with bad Wi-Fi.
- Storyline Technology: It automatically connects every tiny event into a clear visual map, showing you the "who, what, and where" of an attack without you needing to read lines of code.
- Automated Remediation: It can automatically disconnect an infected computer from the network to prevent the "virus" from spreading to other employees.
- Ranger IoT: It scans your office network to find every device, including smart fridges or printers that might be a "backdoor" for hackers.
Pricing:
- Singularity Core: $45 per endpoint annually (Basic AI detection).
- Singularity Control: $75 per endpoint annually (Adds device control and security suite).
- Singularity Complete: $150+ per endpoint annually (Full EDR/XDR and rollback features).
Why it matters:
Speed is the only thing that saves you from ransomware. SentinelOne matters because it reduces the time it takes to fix a breach from days to seconds. For a business, that is the difference between a minor annoyance and a total catastrophe.
4. Palo Alto Networks Cortex XDR
Best for: Companies that want their network, cloud, and devices to "talk" to each other.
Palo Alto Networks is a legend in the firewall space, and Cortex XDR is their AI-powered evolution. Most security tools only look at one thing (like just emails or just laptops). Cortex looks at everything. It pulls data from your firewall, your cloud, and your endpoints to see the big picture. If a hacker tries to sneak in through a cloud account and then jump to a laptop, Cortex sees the whole path. It is a massive, enterprise-grade system for companies that want a "unified front" against cybercrime.
Key Features:
- Cross-Data Integration: It combines data from the network, the cloud, and the devices to find stealthy attacks that would look "normal" to a single-view tool.
- AI-Driven Analytics: It uses machine learning to automatically filter out 98% of the "noise," so your security team only sees the 2% of alerts that actually matter.
- Managed Threat Hunting: You can opt-in for a service where Palo Alto's own experts monitor your system 24/7, effectively acting as an extension of your own team.
- Automated Root Cause Analysis: When a threat is found, the AI automatically tells you exactly where it started, so you can fix the hole and make sure it never happens again.
- External Attack Surface Management: It looks at your company from the outside to find old websites or forgotten servers that hackers might be using to get in.
Pricing:
- Cortex XDR Prevent: $40–$60 per endpoint annually.
- Cortex XDR Pro: $80–$120 per endpoint annually (Full detection and response).
- Large Scale: Typical 3-year contracts for 2,000 endpoints range from $300,000–$550,000.
Why it matters:
Fragmentation is a hacker's best friend. Cortex XDR matters because it breaks down the walls between your different security systems. By having everything in one place, you eliminate the "blind spots" where the most dangerous attacks usually hide.
5. Check Point Harmony
Best for: Protecting remote workers and securing the "Mobile Office."
As more people work from cafes, airports, and home offices, the "office" is now everywhere. Check Point Harmony was designed specifically for this new world. It focuses heavily on securing the browser and the mobile device. It prevents users from downloading malicious files, stops them from entering passwords on fake sites, and protects their mobile apps. It is a "user-centric" tool that follows your employees wherever they go, making sure their connection is safe no matter what Wi-Fi they are using.
Key Features:
- Zero-Phishing Technology: It inspects every website your employees visit in real-time, blocking fake "login" pages before the user can even type their password.
- Secure Internet Access: It acts as a shield for your browser, preventing malicious pop-ups or "drive-by" downloads from infecting the computer while someone is browsing.
- Mobile Security: It protects smartphones from malicious apps and unsecured Wi-Fi networks, which is a huge gap in most companies' security plans.
- Email and Collaboration Security: It plugs directly into apps like Slack, Teams, and Gmail to scan attachments and links for hidden threats.
- VPN-less Remote Access: It allows employees to access internal company files securely without the hassle of a traditional, slow VPN.
Pricing:
- Harmony SASE Essentials: $10 per user per month.
- Harmony SASE Premium: $15 per user per month.
- Harmony Endpoint: $40–$150 per seat annually (Depending on the level of protection).
Why it matters:
The "human" is the weakest link in security. Check Point Harmony matters because it protects people from their own mistakes. It is like having a professional security guard standing behind every employee, gently tapping them on the shoulder before they click a "bad" link.
6. Vectra AI
Best for: Spotting hackers who are already "inside" and moving through your data.
Vectra AI focuses on "Network Detection and Response" (NDR). Most tools try to keep people out, but Vectra assumes the hacker might already be inside. It uses AI to watch the traffic inside your company. It looks for "lateral movement,"which is when a hacker jumps from a low-level computer to a high-level server. It is like a motion-sensor system for your data. It doesn't care about "files," it only cares about "intent." If it sees data being moved in a way that looks like a theft in progress, it sounds the alarm.
Key Features:
- Attack Signal Intelligence: It prioritizes threats based on how dangerous they actually are, so you aren't waking up at 3:00 AM for a minor glitch.
- Privileged Access Monitoring: It keeps a very close eye on "Admin" accounts, which are the primary targets for hackers who want to take over an entire company.
- Cloud Detection: It monitors your AWS, Azure, and Google Cloud environments to ensure that nobody is spinning up "ghost" servers to mine crypto or steal data.
- AI Governance: A new feature for 2026 that helps companies track which "Shadow AI" tools (like unapproved chatbots) their employees are using, preventing data leaks.
- Automated Lockdown: It can work with your other tools (like your firewall) to automatically lock down a specific user account if it shows signs of being compromised.
Pricing:
- Annual Subscription: Typically ranges from $120,000–$250,000 for mid-sized deployments.
- Platform Fee: Usually quote-based, often starting around $50,000 for smaller environments.
Why it matters:
This tool matters because "prevention" is never 100% successful. You need a system that can catch a thief who is already in the building. Vectra is the ultimate "safety net" that prevents a small breach from turning into a company-ending disaster.
7. Nudge Security
Best for: Governing "Shadow AI" and keeping track of all the apps your team uses.
In 2026, the biggest threat isn't just "viruses," it is employees signing up for random AI tools and pasting company secrets into them. Nudge Security is a unique tool that focuses on "SaaS and AI Governance." It automatically finds every single app your employees have signed up for using their work email. Instead of just "blocking" them, it "nudges" the employee with a message: "Hey, we noticed you're using this new AI tool. Here is how to use it safely." It is a modern, human-centric way to manage security in a world full of new apps.
Key Features:
- SaaS Discovery: It finds every single "hidden" app your team is using, from ChatGPT to random design tools, giving you a full inventory in minutes.
- Interactive Nudges: It automatically emails employees when they sign up for a risky app, asking them what they are using it for and providing security guidelines.
- OAuth Risk Analysis: It shows you exactly what permissions your apps have (like "Can read your emails"), helping you cut off apps that are asking for too much data.
- Offboarding Automation: When an employee leaves, Nudge helps you close all their accounts instantly, ensuring they don't keep access to company data on their personal phone.
- AI Supply Chain Mapping: It tells you which of your existing tools have added new AI features, so you can review their privacy policies before your data gets sucked into a new model.
Pricing:
- Small Business: $750 per month (For under 150 accounts).
- Enterprise: $5 per active user per month (For 150–2,500 accounts).
- Custom: Quote-based for larger organizations.
Why it matters:
You cannot protect what you cannot see. Nudge matters because it shines a light on the "Shadow IT" that exists in every company. It turns security into a conversation with your employees rather than a battle against them.
Which one should you choose?
The right choice depends on your biggest "fear." If you are terrified of Ransomware, you should go with SentinelOne because of its rollback feature. If you have a huge, remote team that is always on their phones, Check Point Harmony is the best way to keep them safe. If you are an enterprise-level corporation with a massive budget and need the "best of the best" full-spectrum coverage, CrowdStrike or Palo Alto Cortex is the way to go. For those who just want to stop employees from leaking data into random AI apps, Nudge Security is the most modern and effective solution.
How does this connect to building a strong career or portfolio?
Knowing these tools is the difference between being a "General IT guy" and a "High-Value Security Expert." When you are looking for a job in 2026, companies aren't looking for people who just "know security." They are looking for people who can manage CrowdStrike or deploy Vectra AI.
This is where Fueler comes in. Instead of just saying "I'm good at cybersecurity" on a resume, you can use Fueler to show a project where you set up a Zero Trust environment using Check Point, or a case study of how you used Nudge Security to find 50 "hidden" apps in a company. By showing these real-world assignments and work samples, you give hiring managers the "proof" they need to trust you with their multi-million dollar data. Your portfolio should be a collection of these skills in action, not just a list of certifications.
Final Thoughts
Cybersecurity in 2026 is no longer a "luxury," it is a survival skill. The hackers are using AI to find the cracks in your business, so you must use AI to seal them. Whether you choose a heavyweight like CrowdStrike or a modern "nudge" tool, the goal is the same: stay one step ahead of the threat. The best part? These tools actually make your life easier by automating the boring parts of security, giving you more time to focus on actually growing your company.
FAQs
What is the most affordable AI security tool for small businesses?
Nudge Security and CrowdStrike's "Falcon Go" plan are excellent starting points, offering high-level protection at a price point that won't cripple a small company's budget.
Can AI cybersecurity tools replace a human security team?
No. While the AI does 98% of the heavy lifting, you still need humans to make high-level decisions and handle complex investigations. Think of AI as the "power suit" that makes your human team ten times stronger.
How does "Rollback" work in SentinelOne?
It uses a technology similar to a "system restore point." The AI keeps a record of all changes made to files, and if it detects ransomware, it can undo those specific changes to bring the files back to their original state.
Do I need a VPN if I have an AI security tool like Check Point Harmony?
In many cases, tools like Harmony provide "ZTNA" (Zero Trust Network Access), which is a faster and more secure alternative to a traditional VPN, though some companies still use both for extra layers of safety.
How do I show my cybersecurity skills to an employer in 2026?
The best way is to build a project-based portfolio on a platform like Fueler. Instead of just listing tools, show screenshots of dashboards you've managed or write short "reports" on how you solved a specific security problem.
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.