8 AI Tools That Improve Threat Detection Accuracy

Riten Debnath
30 Apr, 2026

Last updated: April 2026
If you think your "123456" password and a prayer are enough to stop a modern hacker, you are essentially leaving your vault wide open with a "Welcome" mat out front. In an era where a single security breach can wipe out years of hard work in a few hours, the tools you use to watch your back are the only things standing between your data and a very expensive disaster. We are moving past the days of simple antivirus scans into a world of deep network visibility and instant response.
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
Before we dive into the specific gear, understand that threat detection is about visibility. You cannot fix what you cannot see. The following tools are the industry standards for 2026, relied upon by everyone from small startups to global banks to ensure that if someone tries to pick the digital lock, an alarm goes off immediately.
At a glance: Comparing the AI Tools That Improve Threat Detection Accuracy
1. CrowdStrike Falcon
Best for: Comprehensive endpoint protection and stopping breaches in large, distributed teams.
CrowdStrike is widely considered the gold standard for endpoint security because it operates entirely in the cloud. It doesn't bog down your computer with heavy scans; instead, it watches every process and script running on your system. If a file starts acting weird or trying to access data it shouldn't, Falcon kills the process instantly. It is built for speed and massive scale.
- Behavioral Analysis and Indicators of Attack: It ignores what a file is named and focuses strictly on what the file is doing in real-time, which catches sophisticated hackers who rename their malicious tools to look like harmless system updates or legitimate administrative software.
- Global Threat Graph Tracking: This feature maps out the relationship between billions of events across the globe, allowing the software to spot a new attack pattern in seconds based on data collected from other companies, ensuring you are protected from threats before they even reach you.
- Single Lightweight Agent Architecture: Unlike old antivirus software that makes your laptop fan spin like a jet engine and slows down your work, this runs as a single, tiny program in the background that has zero impact on your daily computer performance or battery life.
- Real-Time Remote Response: It provides a direct command-line interface to any infected device on your network, allowing your security experts to jump in and fix the issue remotely from anywhere in the world without needing the physical laptop in their hands.
- Automated Remediation and Quarantine: If a threat is detected, the system can automatically isolate the file and repair any damage to the system registry or files, ensuring the computer is clean and safe to use again without needing a full manual wipe.
Pricing: Falcon Go starts at $59.99 per device per year, Falcon Pro is $99.99 per device per year, and the Falcon Enterprise tier is $184.99 per device per year.
Why it matters: This tool is the difference between finding out you were hacked six months ago and stopping the hacker the second they touch your network. For a professional, knowing how to navigate a Falcon dashboard is a high-value skill that proves you can manage enterprise-level safety.
2. Splunk Enterprise Security
Best for: Large-scale data analysis and turning millions of system logs into a clear security story.
Splunk is often described as "Google for your data." It takes every single log, click, and login from your entire company and puts it into a searchable database. When something goes wrong, Splunk allows you to trace the attacker's footsteps backward to see exactly where they entered. It is the ultimate tool for digital forensics and long-term security monitoring.
- Centralized Data Hub for Everything: It pulls in data from your website, your office routers, your employee laptops, and your cloud storage, giving you one single place to watch everything so that no suspicious activity can hide in a dark corner of your network.
- Custom Alerting and Logic: You can write specific rules, such as "alert me if anyone logs in from two different countries within one hour," which is a classic sign of a stolen password, allowing you to catch identity theft before any data is actually stolen.
- Risk-Based Analytics Score: It assigns a "risk score" to every user and device in your company, so your security team can focus on the most dangerous problems first rather than getting overwhelmed by thousands of minor, harmless notifications.
- Incident Review Dashboards: It creates beautiful, easy-to-read charts and maps that show you exactly where your security stands, making it easy to explain risks to managers who aren't tech-savvy so they can understand why security budgets are necessary.
- Massive App Ecosystem: There are thousands of pre-built "apps" within Splunk that allow it to connect instantly to other tools like Zoom, Microsoft 365, or Amazon Web Services, ensuring your entire digital world is monitored under one roof.
Pricing: Platform and Security products require a sales quote, but cloud ingestion typically ranges from $1,620 to $1,860 per GB per day annually, with Observability tiers starting at $15 per host per month.
Why it matters: Accuracy in threat detection comes from having all the facts. Splunk ensures that no piece of evidence is lost, allowing you to prove exactly what happened during an incident, which is essential for legal compliance and maintaining customer trust.
3. SentinelOne Singularity
Best for: Businesses looking for an "all-in-one" platform that can undo the damage of a virus with one click.
SentinelOne is the main rival to CrowdStrike, but it focuses heavily on "healing" a computer after an attack. Their AI is built directly into the agent on your laptop, so even if you aren't connected to the internet, the software can still stop a virus. Its most famous feature is the "Rollback," which acts like a time machine for your files.
- AI-Powered Threat Prevention: It uses advanced machine learning to identify and block malware without needing to be connected to a central server, ensuring that your laptop stays protected even when you are working from a remote coffee shop or on a plane.
- One-Click Ransomware Rollback: If a virus manages to encrypt your files, this feature allows you to revert the entire computer back to a healthy state from a few minutes prior, completely neutralizing the attack without you having to pay any ransom.
- Storyline Threat Visualization: It automatically connects every tiny event in an attack into a single visual timeline, so you don't have to guess how a hacker got in; the software literally draws you a map of the entire breach from start to finish.
- IoT and Rogue Device Discovery: It automatically finds every device connected to your office network, from smart printers to lightbulbs, and alerts you if an unmanaged or "rogue" device appears that shouldn't be there, preventing hackers from using "smart" tech as a backdoor.
- Automated Investigation with Purple AI: This tool allows you to ask security questions in plain English, like "Show me all logins from last night," and it will automatically find the data for you, saving hours of manual searching for your security team.
Pricing: Singularity Core is $69.99 per endpoint per year, Singularity Control is $79.99, and the most popular tier, Singularity Complete, is $179.99 per endpoint per year.
Why it matters: This tool is perfect for teams that don't have a 24/7 security room. The automation and rollback features mean that even a small team can survive a major attack that would normally put a business out of commission for weeks.
4. Palo Alto Networks Cortex XDR
Best for: Unified security that connects network, cloud, and endpoint data into one view.
Cortex XDR is designed to stop "siloed" security, where your network and your laptops are watched by different tools that don't talk to each other. It gathers data from everywhere and uses it to find patterns that a human would miss. It is particularly strong for companies that already use Palo Alto firewalls.
- Holistic Data Stitching: It combines alerts from your firewalls, your cloud servers, and your employees' laptops into one single incident, ensuring that a hacker who tries to sneak through multiple different layers of your business is caught by the cross-referencing.
- Managed Threat Hunting Experts: When you use this tool, you get access to professional human hunters who work alongside the software to look for tiny, hidden traces of hackers that automated systems might accidentally ignore or label as "normal."
- Automated Root Cause Analysis: It tells you exactly how the hacker got in, what they touched, and where they went next, saving your team from having to spend days manually piecing together the puzzle of a digital break-in.
- Behavioral Policy Labelling: You can set specific "behavioral rules" for different departments, so the system knows that a developer using a terminal is normal, but a HR manager using a terminal is a major red flag that needs instant attention.
- Large-Scale Data Retention: It allows you to store massive amounts of security data for months at a time, which is critical for finding "slow and low" attacks where a hacker stays inside your system for a long time before doing anything.
Pricing: Enterprise plans for Palo Alto services average around $1,023,576 per year, while SMB-focused setups typically average $182,825 per year, though specific XDR licensing is quoted per endpoint or data volume.
Why it matters: By integrating data from multiple sources, Cortex XDR reduces "alert fatigue." It ensures that security officers only spend time on high-accuracy alerts that represent real danger, rather than chasing ghosts in the system.
5. Darktrace HEAL
Best for: Self-learning security that understands your unique business "immune system."
Darktrace takes a totally different approach by not looking for "bad" things at all. Instead, it spends its first few weeks learning what "normal" looks like for your specific company. Once it knows your habits, it can spot any deviation immediately. It’s like having a digital immune system that knows when your business has caught a "cold."
- Self-Learning Digital Immune System: It does not require any manual updates or a database of known viruses; instead, it builds a unique mathematical model of your business and detects threats purely because they look "different" from your usual behavior.
- Real-Time Attack Visualization: It provides a 3D map of your entire network, showing you exactly where an attack is moving in real-time, allowing you to watch the "infection" spread and stop it before it reaches your most sensitive data servers.
- Autonomous Cyber AI Response: When it sees a threat, the AI can take surgical action to stop just the malicious activity like cutting off one specific connection without shutting down the entire computer or interrupting the employee's legitimate work.
- Visual Incident Reporting: It automatically creates easy-to-read reports that explain exactly what happened during a security event, which is perfect for showing your clients or board of directors that you have full control over your digital safety.
- Proactive Recovery Planning: The "HEAL" feature helps you build a step-by-step plan to recover your data and systems after an attack, ensuring that you don't miss any hidden backdoors the hacker might have left behind for later.
Pricing: Pricing is custom-based on network size and number of users, but enterprise deployments typically start in the tens of thousands of dollars per year.
Why it matters: Accuracy is highest here because the tool is tuned specifically to you. It won't flag a late-night data transfer if that’s a normal part of your job, but it will catch an unusual login from a country your team has never visited.
6. Vectra AI
Best for: Finding hackers who have already managed to bypass your front-door security.
Vectra AI is like an internal motion sensor. While other tools focus on the "walls" of your business, Vectra watches the "hallways." It assumes that a hacker will get in eventually and focuses entirely on finding them before they can steal anything. It is the best tool for stopping "lateral movement" inside a network.
- Attack Signal Intelligence: It uses machine learning to prioritize the most dangerous threats so your team knows exactly what to fix first, preventing them from wasting time on low-level issues while a major heist is happening.
- Deep Identity Monitoring: It keeps a constant eye on every user account to see if it is being used by an unauthorized person, catching "account takeovers" that usually go unnoticed by traditional antivirus software.
- Hybrid Cloud and Data Center Support: It works seamlessly across your physical office network and your cloud services like AWS or Azure, ensuring there are no blind spots in your security as you move data between different locations.
- Automated Alert Triage: It reduces the manual work for your security staff by grouping related alerts together into one "story," so they only have to review one incident instead of five hundred separate notifications.
- Privileged Access Tracking: It monitors your most powerful accounts like your IT admins to ensure they aren't being misused, which is critical since these accounts are the number one target for professional cyber-criminals.
Pricing: Subscription-based pricing is available upon sales request, typically tailored to the number of IP addresses or users being monitored.
Why it matters: This tool provides a vital second layer of defense. By focusing on the "post-compromise" phase, it ensures that even if a hacker gets past your firewall, they cannot move around or steal data without being caught.
7. Fortinet FortiGuard
Best for: High-speed network security and blocking malicious websites before they load.
Fortinet is a giant in the hardware world, and its FortiGuard services bring AI intelligence to their firewalls. It processes over 100 billion events every day to keep its "blacklist" updated. This is the tool you use to ensure that your employees don't accidentally click on a phishing link or download a malicious file from the web.
- Real-Time Web Filtering: It uses a massive global database to categorize and block dangerous websites the moment they are created, ensuring your team can't accidentally land on a fake login page or a site full of malware.
- Automated Cloud Sandboxing: It takes any suspicious file and runs it in a safe, isolated "sandbox" in the cloud to see what it does before it ever reaches your computer, effectively stopping brand-new viruses that haven't been seen before.
- Intrusion Prevention System (IPS): It constantly scans your internet traffic for "exploits"which are known bugs in software like Windows or Chrome and blocks them, protecting you even if you haven't installed the latest security updates yet.
- Global Threat Intelligence Updates: Every Fortinet device in the world talks to each other; if a new virus is found in London, your office in New York is protected from it within minutes thanks to the constant stream of AI-driven updates.
- IoT Device Security Profiles: It automatically identifies "dumb" devices like smart fridges or cameras and places them in a restricted part of your network, so if they get hacked, the attacker can't use them to reach your main computers.
Pricing: Small business hardware ranges from $700 to $1,000, while larger systems for 15-100 users cost between $1,500 and $4,000, plus yearly FortiGuard subscription fees.
Why it matters: Fortinet provides the "shield" at the front door. By stopping 99% of threats at the network level, you keep your employees' computers clean and reduce the pressure on the rest of your security team.
8. Wiz Security
Best for: Modern companies that run entirely in the cloud and need to see everything at once.
Wiz has taken the security world by storm because it doesn't require you to install anything. It connects to your cloud accounts (like AWS, Google Cloud, or Azure) in minutes and scans everything for vulnerabilities. It is the fastest way to get a bird's-eye view of your entire cloud security posture.
- Agentless Cloud Scanning: You don't have to install any software on your servers; instead, Wiz connects directly to your cloud provider and "looks" at your data, which means it can be set up in minutes without breaking any of your existing systems.
- Cloud Security Graph: It creates a visual map showing how different parts of your cloud are connected, highlighting "attack paths" where a hacker could potentially hop from a public website into your private database.
- Vulnerability Prioritization: It tells you exactly which bugs you need to fix first based on how much risk they actually pose to your data, preventing your developers from wasting time on thousands of minor, harmless issues.
- Compliance Tracking and Auditing: It automatically checks your cloud against global standards like SOC2 or GDPR and gives you a simple "Pass/Fail" score, making it incredibly easy to get ready for official security audits.
- Secret and Password Detection: It scans your cloud code for "leaked" passwords or API keys that your developers might have accidentally left behind, which is one of the most common ways that modern companies get hacked.
Pricing: Custom enterprise pricing usually starts around $10,000 to $15,000 per year for smaller cloud environments, scaling up based on the number of resources and workloads protected.
Why it matters: In 2026, the cloud is where most hacks happen. Wiz gives you total visibility without the headache of managing software on every single server, making it the most accurate tool for modern, cloud-first companies.
Which one should you choose?
Choosing the right tool depends entirely on your business structure and what you are most afraid of losing. If you have a large team of remote employees using laptops everywhere, CrowdStrike Falcon or SentinelOne are your best bets because they protect the device no matter where it is. If you are a high-tech company running everything on the cloud, Wiz is the clear winner for its speed and visibility. For those who need a "set it and forget it" system that learns your unique habits, Darktrace is the most intuitive choice. Small businesses looking for a physical "front door" shield should stick with Fortinet.
How does this connect to building a strong career or portfolio?
In the current job market, simply saying "I know about security" isn't enough to get you hired. Companies want to see that you have actually used these industry-standard tools to solve real problems. By documenting your experience with software like Splunk or CrowdStrike, whether through certifications, home-lab projects, or work assignments, you prove you are ready to handle high-stakes environments. This is exactly why we built Fueler. You can take screenshots of your security dashboards, write up your threat-hunting processes, and host them in a professional portfolio. Showing a hiring manager a real sample of how you identified a threat using these tools is 10x more powerful than a bullet point on a resume.
Final Thoughts
The digital world is getting faster and more dangerous, but you don't have to face it alone. These eight tools represent the absolute best in modern threat detection, offering everything from "one-click healing" to global threat intelligence. While no tool is a magic bullet, using them accurately will significantly lower your risk of a business-ending breach. Remember, the best security is proactive; don't wait for a hack to happen before you start looking for a lock.
FAQs
1. What are the best threat detection tools for small businesses in 2026?
For small businesses, CrowdStrike Falcon Go and Fortinet are excellent starting points because they offer high-level protection at a per-device price that fits a smaller budget.
2. Is AI actually necessary for threat detection?
While not "mandatory," AI is highly recommended because it can process data millions of times faster than a human, catching subtle attack patterns that traditional software would miss.
3. How do I start a career in threat detection?
Start by learning the basics of network security, getting familiar with tools like Splunk (which has free training), and building a portfolio on Fueler to showcase your technical projects.
4. What is the difference between EDR and XDR?
EDR (Endpoint Detection and Response) focuses only on your laptops and servers, while XDR (Extended Detection and Response) connects data from your network, cloud, and email for a bigger picture.
5. How much does enterprise security software usually cost?
Costs vary wildly, but you can expect to pay anywhere from $60 to $200 per user per year for high-end protection, with large-scale data tools costing significantly more.
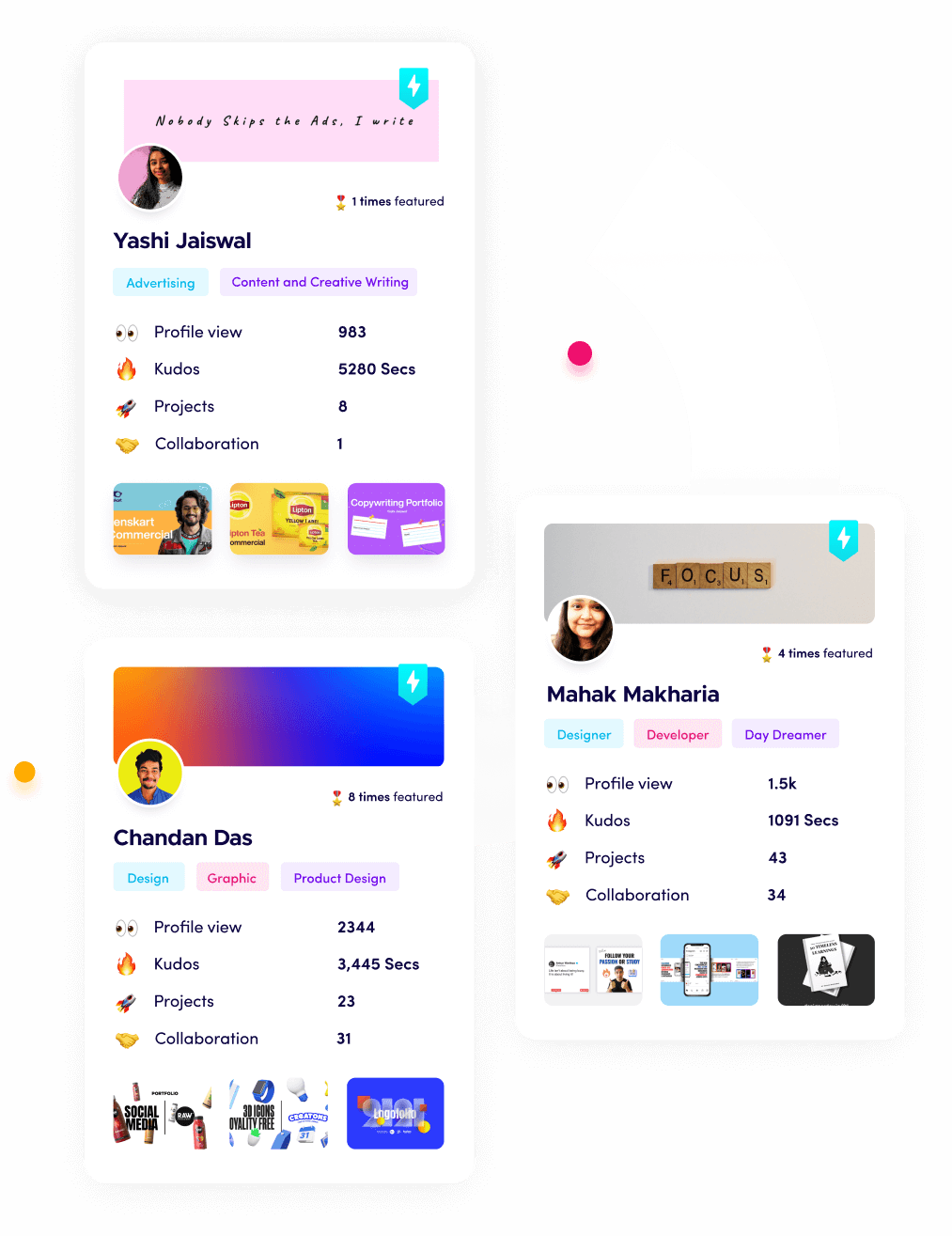
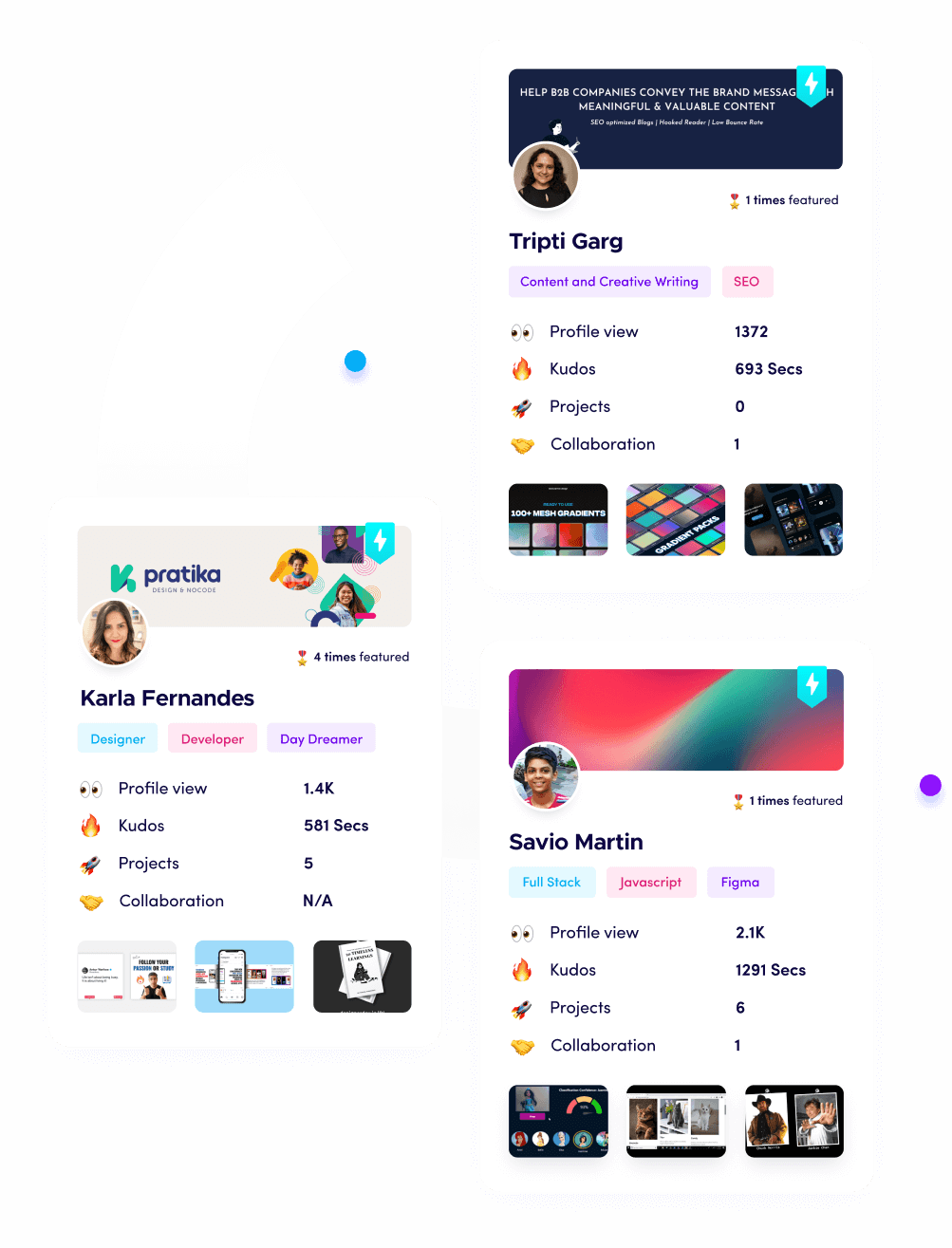
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.