10 AI Tools That Improve Security Workflows

Riten Debnath
30 Apr, 2026

Last updated: April 2026
A single unpatched vulnerability is all it takes to turn a thriving business into a cautionary tale overnight.
In the world of cybersecurity, the "flashy" tech often gets the headlines, but the real work is done by robust, reliable tools that give humans total control over their data. To truly improve security workflows, you need systems that offer deep visibility, precise control, and clear evidence of what is happening on your network. Relying on solid, foundational software ensures that your defense is built on a rock-solid base rather than unpredictable trends.
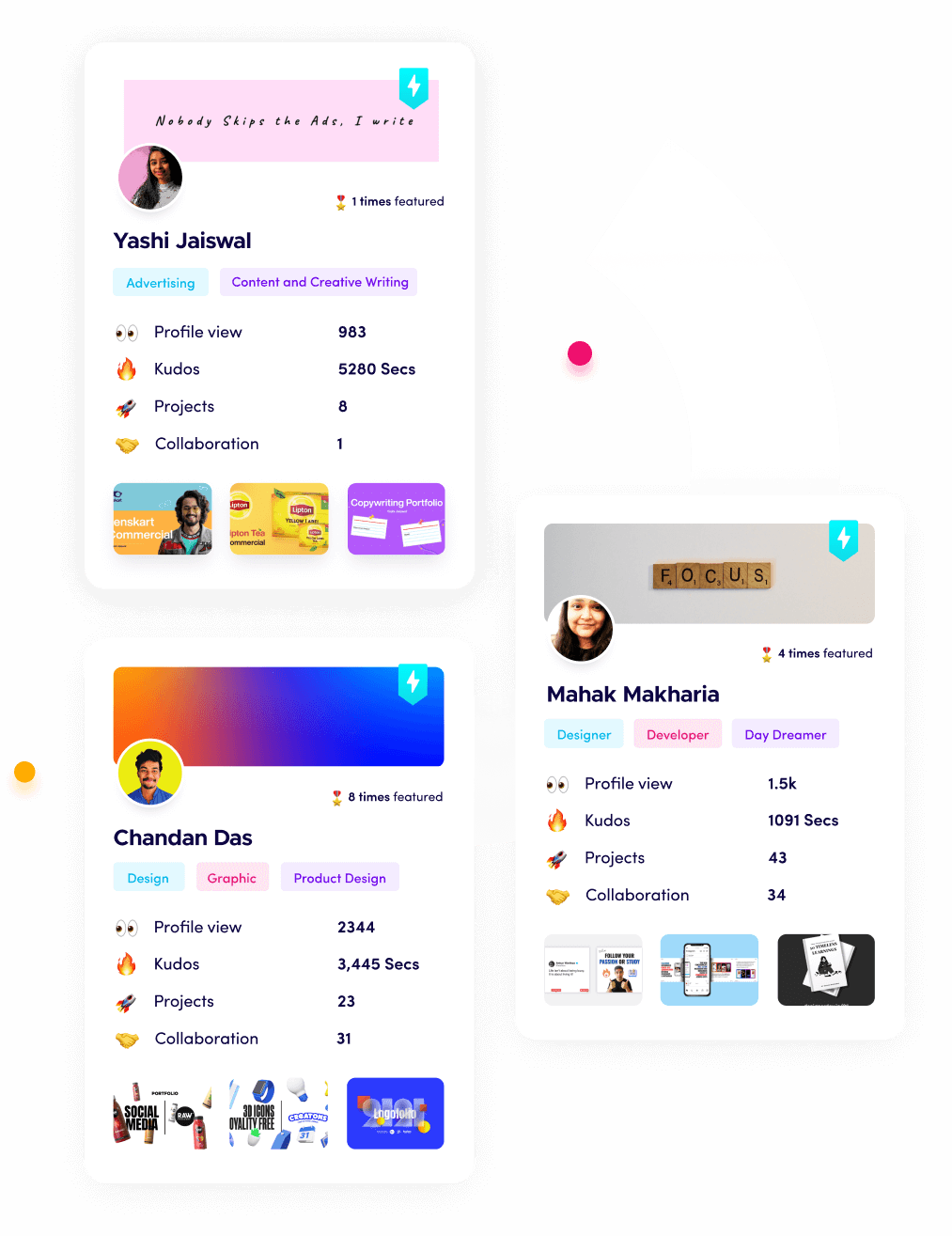
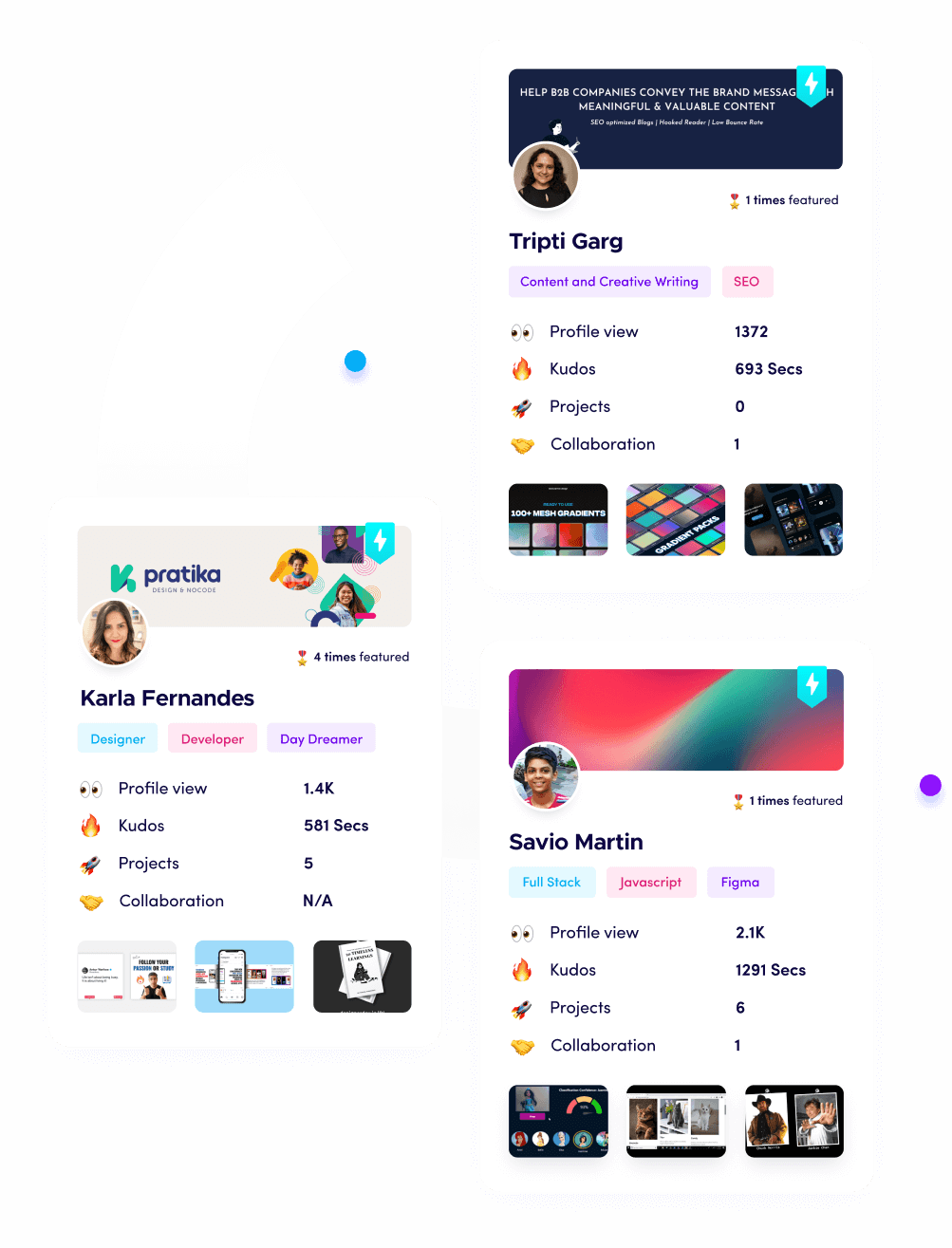
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
At a glance: Comparing the AI Tools That Improve Security Workflows
1. Splunk Enterprise
Best for: Large-scale data analysis and security information management.
Splunk is the industry standard for making sense of massive amounts of machine data generated by your business every second. It gathers logs from every corner of your infrastructure, from your website servers to your employee laptops, and puts them in a searchable index. It helps security teams find the "needle in the haystack" when investigating a potential hack or system failure.
- Centralized Data Logging: It acts as a universal vacuum for data, collecting and indexing logs from almost any source or format so that your team has a single, unified place to search for security events.
- Real-Time Alerting Systems: You can configure highly specific triggers that send instant notifications to your security team the very moment a suspicious error or unauthorized login attempt occurs on the network.
- Highly Customizable Dashboards: The platform allows you to build visual charts and live graphs that display the real-time health of your security posture, making it easy for stakeholders to understand the current risk level.
- Deep Incident Investigation: It provides a granular, second-by-second timeline of digital events, which is absolutely essential for forensic teams to reconstruct exactly how a breach started and what data was touched.
- Automated Compliance Reporting: It streamlines the tedious process of auditing by automatically generating the complex reports required to prove your company is meeting strict legal and industry security standards.
Pricing: Standard pricing starts at approximately $150 USD per month for the "Splunk Cloud" entry tier, while large enterprise licenses typically scale based on the volume of data indexed, often exceeding $2,000 USD per gigabyte of daily data.
Why it matters: Improving security workflows is impossible if you are blind to your own data. Splunk gives you the "eyes" to see across your entire digital empire, ensuring that no suspicious activity can hide in the dark corners of your servers.
2. Wireshark
Best for: Microscopic network traffic analysis and protocol debugging.
Wireshark is the world’s most famous network protocol analyzer, acting like a digital microscope for your internet connection. It allows you to intercept and see exactly what is happening on your network in real-time by capturing "packets" of data as they move. It is an essential tool for identifying hidden malware communication or unauthorized data leaks.
- Live Packet Capture: It allows you to watch data travel across the wire in real-time, providing a live feed of every single communication happening between devices on your internal or external network.
- Deep Protocol Inspection: The tool can break down and "read" hundreds of different internet languages, or protocols, allowing you to see the actual content of the messages being sent between computers and servers.
- Powerful Search Filters: You can write specific rules to filter out the "noise" of normal internet traffic and focus exclusively on the specific type of data or the suspicious IP address that is causing concern.
- Multi-Platform Compatibility: Because it runs on Windows, macOS, and Linux, security professionals can use it in almost any environment, whether they are working on a high-end workstation or a server in a data center.
- Offline Analysis Capabilities: Beyond live monitoring, you can save massive files of captured data and open them later to perform a deep forensic deep-dive into a past security event or network crash.
Pricing: Wireshark is a completely free, open-source tool maintained by a global community, so there is no cost to download or use it for commercial purposes.
Why it matters: When you need to know exactly what a piece of malware is doing, you cannot guess. Wireshark provides the cold, hard facts of network communication, making it a mandatory tool for any serious security workflow.
3. Burp Suite Professional
Best for: Web application security testing and finding website vulnerabilities.
Burp Suite is the "Swiss Army Knife" for people who test website security. It acts as a middleman between your web browser and the server, allowing you to intercept, inspect, and modify the data you send to a website. This helps security researchers find bugs like weak passwords or broken checkout pages before hackers do.
- Interception Proxy Power: It lets you pause a request sent from your browser to a website, allowing you to change the data inside the request to see how the website handles unexpected or "bad" information.
- Automated Vulnerability Scanning: The professional version includes a powerful scanner that automatically hunts for common website flaws like SQL injection or Cross-Site Scripting, saving hours of manual work for the tester.
- Advanced Manual Testing Tools: It provides a suite of tools like "Repeater" and "Intruder" that allow you to send the same web request over and over with slight variations to find hidden entry points.
- Extensibility via BApp Store: You can customize the software by downloading hundreds of community-made plugins that add new features, such as specific tests for cloud platforms like AWS or Azure.
- Detailed Technical Documentation: For every bug it finds, Burp Suite provides a clear explanation of the risk and a step-by-step guide on how the developers can fix the code to prevent a real hack.
Pricing: Burp Suite Professional costs $449 USD per user per year for a standard license.
Why it matters: Most modern businesses live on the web. Burp Suite improves your workflow by giving you the exact tools needed to ensure your website is a fortress, protecting your customer's data from common web-based attacks.
4. Nessus (by Tenable)
Best for: Identifying missing patches and weak configurations across a company.
Nessus is a vulnerability scanner that checks your computers, routers, and servers to see if they are missing important security updates. It is like a digital building inspector that walks through your network and points out which "doors" are unlocked or which "windows" are broken. It is widely used to maintain a high level of security hygiene.
- Comprehensive Vulnerability Library: It maintains one of the largest databases of known security flaws in the world, ensuring that even the most obscure or brand-new bugs can be detected on your systems.
- High-Speed Network Scanning: The engine is built for efficiency, allowing it to scan thousands of devices across a large corporate network in a very short amount of time without crashing the systems it is testing.
- Accurate Configuration Auditing: It doesn't just look for bugs; it also checks if your systems are set up correctly according to "Best Practices," such as ensuring that default, easy-to-guess passwords have been changed.
- Prioritized Risk Reporting: Instead of just giving you a long list of problems, it ranks them by "Criticality," so your team knows exactly which fires to put out first to have the biggest impact on safety.
- Cloud and Asset Discovery: It can automatically find new devices that have joined your network or cloud environment, ensuring that a "shadow" computer doesn't stay hidden and unpatched for months.
Pricing: Nessus Professional is priced at approximately $3,590 USD for a one-year license, with discounts usually available for multi-year commitments.
Why it matters: You cannot fix what you do not know is broken. Nessus automates the discovery of weaknesses, allowing your security team to focus on fixing problems rather than spending weeks trying to find them.
5. Metasploit Framework
Best for: Penetration testing and verifying if a vulnerability can actually be exploited.
Metasploit is a tool that helps security professionals "think like a hacker." While tools like Nessus find the holes, Metasploit allows you to safely test if those holes can actually be used to get into a system. It is used to prove to management that a vulnerability is a real threat that needs immediate attention.
- Huge Exploit Database: It contains thousands of "exploits," which are pieces of code designed to take advantage of specific bugs, allowing security pros to test their defenses against real-world attack methods.
- Safe Testing Environment: It provides a controlled way to test vulnerabilities without actually damaging the company's systems, ensuring that you can prove a point without causing a real-world outage.
- Post-Exploitation Modules: Once a "breach" is simulated, Metasploit allows you to see what a hacker could do next, such as stealing passwords or moving from one computer to another inside the network.
- Payload Customization: It allows users to create custom "payloads," which are instructions for what the computer should do after the security hole is opened, such as opening a secure communication channel for the tester.
- Team Collaboration Features: The framework allows multiple security researchers to work together on a single "attack" simulation, sharing notes and data in real-time to improve the overall quality of the test.
Pricing: The basic "Framework" version is free and open-source. The "Metasploit Pro" version, which includes more automation and reporting, costs roughly $15,000 USD per user per year.
Why it matters: Sometimes people don't believe a "hole" is dangerous until they see someone walk through it. Metasploit provides the proof needed to justify security spending and ensures your workflows are focused on the most dangerous threats.
6. Snort
Best for: Detecting and preventing intruders on a network in real-time.
Snort is an open-source Network Intrusion Detection System (IDS). It sits on your network and "sniffs" the traffic, comparing it against a set of rules that describe what a hack looks like. If it sees something that matches a rule, it can sound an alarm or even block the traffic entirely to protect the network.
- Rule-Based Detection: It uses a massive library of community-written rules that tell the system exactly what specific types of malicious traffic look like, from virus signatures to "brute force" login attacks.
- Real-Time Traffic Logging: Every time an alert is triggered, Snort records the details of the event, providing a clear trail of evidence that tells you who tried to get in and what they were trying to do.
- Three Functional Modes: It can act as a simple packet "sniffer," a detailed packet logger for forensics, or a full-blown intrusion prevention system that actively blocks "bad" data from entering the network.
- Massive Community Support: Because it is open-source, thousands of security experts around the world contribute new rules every day, ensuring the software stays updated against the very latest internet threats.
- Low Hardware Requirements: It is designed to be very lightweight, meaning you can run it on older hardware or small devices to protect small offices without needing to buy expensive new servers.
Pricing: Snort is free to download and use. However, for the most up-to-date "Official" rule sets from Cisco, subscriptions start at around $399 USD per year for individuals or more for businesses.
Why it matters: You need a digital guard at the gate. Snort provides that constant, automated surveillance, ensuring that your security workflow includes a system that can react to a threat in milliseconds.
7. KeePassXC
Best for: Secure, offline password management for sensitive credentials.
While many people use cloud-based password managers, top security pros often prefer KeePassXC. It is an offline tool that stores all your passwords in an encrypted "vault" file that stays on your own computer. This means your passwords are never stored on someone else's server, giving you total control over your most sensitive keys.
- Military-Grade Encryption: It uses industry-standard encryption algorithms to lock your password database, ensuring that even if someone steals the file, they cannot read your passwords without your master key.
- No Cloud Dependency: Since it is entirely offline, you don't have to worry about the password manager company getting hacked; your data is only as accessible as you allow your physical computer to be.
- Auto-Type Functionality: It can automatically type your usernames and passwords into websites and apps for you, which helps protect you against "keyloggers" that try to record what you type on your keyboard.
- Secure Password Generator: The tool includes a feature that creates incredibly complex, long, and random passwords that are impossible for humans to guess or for computers to "crack" easily.
- Database Health Checks: It can scan your existing passwords to tell you if you are using the same password in too many places or if your passwords are too weak to be considered safe.
Pricing: KeePassXC is completely free and open-source software with no subscription fees or hidden costs.
Why it matters: Passwords are the keys to your kingdom. By using a tool that keeps those keys offline and encrypted, you eliminate the risk of a massive cloud-provider breach affecting your company's most important accounts.
8. Nmap (Network Mapper)
Best for: Discovering what devices are on a network and what they are doing.
Nmap is the world's most popular tool for network discovery. It sends out small signals to every IP address on a network to see if anyone "answers." It tells you which computers are online, what operating systems they are running, and which "ports" (digital doors) are open and waiting for a connection.
- Fast Port Scanning: It can scan thousands of digital ports in seconds to find out which services, like a website or an email server, are currently running and accessible to the outside world.
- OS Fingerprinting: By looking at how a computer responds to a signal, Nmap can accurately guess if the machine is running Windows, macOS, Linux, or even a specialized device like a smart printer.
- Nmap Scripting Engine (NSE): This allows users to write simple scripts to automate tasks, such as checking if a specific server is vulnerable to a very famous hack without needing a larger, heavier scanner.
- Network Inventory Mapping: It helps administrators keep an updated list of every single device connected to the corporate WiFi or wired network, ensuring no "rogue" devices are hiding in the background.
- Service Version Detection: It doesn't just see that a "door" is open; it tells you exactly what software is guarding that door and what version it is, helping you spot outdated software that needs an update.
Pricing: Nmap is free and open-source software, available for anyone to use for any purpose without payment.
Why it matters: You cannot protect what you don't know exists. Nmap is the ultimate tool for "mapping" your territory, ensuring that every single device under your care is accounted for and properly secured.
9. GnuPG (GPG)
Best for: Encrypting emails and verifying the identity of file senders.
GnuPG, often called GPG, is a tool that allows you to lock your messages and files so that only the intended recipient can read them. It also allows you to "sign" a file with a digital stamp, proving that the file really came from you and hasn't been tampered with by a middleman.
- Public Key Cryptography: It uses a clever system of two "keys"one you give to everyone and one you keep secret to ensure that anyone can send you a secure message, but only you can open it.
- Digital Signatures: It allows you to place an unforgeable digital seal on your software or documents, ensuring that your customers or colleagues know the file hasn't been modified by a hacker.
- File Encryption: Beyond just emails, you can use GPG to lock individual files on your hard drive or in your cloud storage, adding an extra layer of protection to your most sensitive business plans.
- Trust Network Management: It includes a system for "verifying" your friends' and colleagues' keys, ensuring that you are actually talking to who you think you are talking to on the internet.
- Cross-Platform Support: Because it is a global standard, GPG works across all major computer systems, allowing a Windows user to send a perfectly secure message to a Linux user without any compatibility issues.
Pricing: GnuPG is free software under the GNU General Public License, meaning it is free for everyone to use and modify.
Why it matters: In a world of "phishing" and fake identities, GPG provides the "ID card" and the "vault" needed to ensure your business communication remains private and authentic.
10. OpenVAS (GVM)
Best for: A full-featured, open-source alternative for vulnerability management.
OpenVAS is a comprehensive vulnerability scanner that is often seen as the free alternative to Nessus. It provides a massive set of tests to check your computers for security holes. It is perfect for smaller companies or individual professionals who want high-quality security checks without the high-end corporate price tag.
- Regularly Updated Tests: It draws from a feed of over 50,000 "Network Vulnerability Tests," ensuring that your scans are always looking for the latest threats found by security researchers globally.
- Scheduled Scanning: You can set the software to automatically scan your network every week or every month, ensuring that new security holes are found shortly after they appear without you having to remember to check.
- Web-Based Interface: It provides a clean dashboard that you can access through your web browser, making it easy to manage your scans and view your reports from any computer in your office.
- Detailed Remediation Advice: When it finds a bug, it doesn't just name the problem; it provides links to the official fixes and explains the exact steps your IT team should take to secure the device.
- In-Depth Reporting Formats: You can export your scan results into PDF or XML files, making it easy to share the "proof" of your security work with managers, clients, or auditors.
Pricing: OpenVAS is open-source and free. For companies that want professional support and a "Greenbone" hardware appliance, commercial versions are available starting around $3,000 USD per year.
Why it matters: Security should be accessible to everyone. OpenVAS allows professionals to implement a world-class vulnerability management workflow without needing a massive budget, proving that smart work beats high spending every time.
Which one should you choose?
If you are just starting to build a professional security workflow, the "must-haves" are Nmap for seeing what you own and KeePassXC for protecting your access. If you are working in a corporate environment where you need to manage thousands of alerts, Splunk is the undisputed king of visibility. For those focused on web security, Burp Suite is the only tool that truly gives you the control needed to protect modern apps. The best choice depends on your specific role, but a well-rounded expert should eventually have experience with at least three or four of these.
How does this connect to building a strong career or portfolio?
In the security industry, "knowing" a tool isn't enough; you have to prove you can use it to solve real problems. When you use Wireshark to find a leak or Nessus to secure a network, you are creating "proof of work." By documenting these projects and showing your methodology, you move from being just another person with a resume to a professional with a track record. This is exactly what we focus on at Fueler: helping you take these technical wins and turn them into a visual portfolio that shows companies you are ready to be hired based on your actual skills.
Final Thoughts
Mastering these tools is about more than just clicking buttons; it is about developing a mindset for safety and efficiency. A great security workflow is one where the tools handle the repetitive data gathering, allowing the human to make the critical decisions. Whether you are using free tools like Nmap or enterprise giants like Splunk, the goal is always the same: visibility and control. Start small, pick one tool to master this week, and slowly build the technical "muscles" that will define your career.
FAQs
1. Are these free security tools safe for professional business use?
Yes, tools like Nmap, Wireshark, and Snort are industry standards used by the world's largest companies. Being "open-source" often means they are more secure because thousands of experts check the code for errors.
2. How much does a professional Splunk certification cost in 2026?
While software prices change, most professional Splunk certification exams typically cost around $130 USD per attempt, though the required training courses can cost significantly more.
3. Can I use Burp Suite for free for my portfolio projects?
Yes, there is a "Community Edition" of Burp Suite that is completely free. It lacks the automated scanner, but it is perfect for learning the manual skills needed to build a web security portfolio.
4. Do I need a powerful computer to run a vulnerability scanner like OpenVAS?
Vulnerability scanners can be resource-intensive. It is recommended to have at least 8GB of RAM and a modern multi-core processor to run scans smoothly without slowing down your other work.
5. Which security tool is the best for a total beginner to learn first?
Nmap is widely considered the best tool for beginners. It has a simple command-line interface, is completely free, and teaches you the fundamental basics of how the internet and networking actually work.
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.