7 AI Tools That Improve Security for Remote Teams

Riten Debnath
14 May, 2026

Last updated: May 2026
If your remote security strategy is still just "don't click on weird links," you are basically trying to stop a flood with a paper towel. In 2026, the bad guys are using automated scripts that scan your home Wi-Fi for weaknesses before you have even finished your morning coffee. Your team is working from couches, cafes, and airports, which means the old office firewall is officially retired. You need a digital bouncer that follows your employees wherever they go.
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
Cybersecurity in the remote era is no longer about building a wall around a building; it is about protecting the person, the device, and the data in real-time. This guide dives into the top AI-powered tools that are actually moving the needle in 2026, ensuring your remote team stays productive without becoming a headline in a data breach report.
At a glance: Comparing the AI Tools That Improve Security for Remote Teams
1. CrowdStrike Falcon
Best for: Comprehensive endpoint protection and stopping "silent" breaches on remote laptops.
CrowdStrike is the heavy hitter in the world of cloud-native security. It does not wait for a virus to start deleting files; instead, it uses behavioral AI to notice if a laptop is acting "weird"like trying to send encrypted data to a random server in the middle of the night. It is lightweight, so it won't slow down your team’s computers while they are trying to work.
- NGAV (Next-Gen Antivirus): This feature goes beyond simple file scanning and uses machine learning to identify and block malicious patterns of behavior even if the specific "virus" has never been seen before in the wild.
- Falcon Insight (EDR): Think of this as a "black box" flight recorder for your computer that tracks everything happening on the device, allowing security teams to see exactly how a hacker tried to get in and stop them instantly.
- Threat Intelligence Integration: The platform automatically consumes data from millions of other devices worldwide, so if a new threat is discovered in London, your remote team in Bangalore is protected within seconds without needing a manual update.
- Device Control: This allows you to manage and secure the USB ports on your remote team's laptops, ensuring that no one accidentally (or intentionally) plugs in a malicious thumb drive that could infect the entire company network.
- Falcon OverWatch: This is a 24/7 human-led threat hunting service that works alongside the AI to catch the most sophisticated "hands-on" attackers who try to mimic legitimate user behavior to hide their tracks.
Pricing: Falcon Go starts at $59.99 per device/year for small teams. Falcon Pro is $99.99 per device/year, and the Enterprise tier goes up to $184.99 per device/year for full visibility and response capabilities.
Why it matters: When your team is remote, their laptop is the only thing standing between a hacker and your company's data. CrowdStrike matters because it provides enterprise-grade protection that travels with the employee, ensuring that a "home office" is just as secure as a corporate headquarters.
2. Zscaler Private Access (ZPA)
Best for: Replacing clunky VPNs with a "Zero Trust" approach to remote app access.
VPNs are so 2010. They are slow, they drop connections, and once a hacker gets into a VPN, they have the keys to the whole kingdom. Zscaler ZPA uses AI to connect your remote employees directly to the specific apps they need and nothing else. It creates a "dark" network that hackers can't even see, making it impossible for them to attack what they can't find.
- Identity-Centric Access: The system verifies the user's identity and the health of their device before granting access to any application, ensuring that only the right people get in on secure machines.
- Automated Micro-Segmentation: Instead of giving someone access to the whole network, ZPA uses AI to create a tiny "segment" just for the app they are using, which prevents hackers from moving sideways through your systems.
- Global Cloud Footprint: Because Zscaler runs on a massive global network, your remote team gets fast, low-latency connections no matter where they are in the world, eliminating the "speed penalty" usually associated with security tools.
- App Discovery: The AI automatically finds and catalogs all the internal apps being used by your team, helping you identify "Shadow IT" or forgotten servers that might be sitting unprotected and vulnerable to exploits.
- Continuous Risk Assessment: ZPA constantly monitors the connection and will automatically revoke access if it notices the user's risk profile has changed, such as a sudden login from an impossible geographic location.
Pricing: Basic access plans typically start around $140 per user/year. Advanced configurations with full segmentation controls average about $225 per user/year, while full enterprise suites can exceed $375 per user/year.
Why it matters: Zscaler matters because it solves the biggest remote work headache: secure access that doesn't annoy the employees. By removing the need for a traditional VPN, you improve the user experience while simultaneously making your network much harder for criminals to infiltrate.
3. Darktrace / EMAIL
Best for: Stopping sophisticated, AI-generated phishing attacks that look perfectly normal.
Hackers are now using AI to write emails that sound exactly like your coworkers. Darktrace / EMAIL doesn't look for "bad words" or "known scams." Instead, it uses "Self-Learning AI" to understand the unique "pattern of life" for your company. If your accountant suddenly sends a "bill" that doesn't look like their usual invoices, Darktrace flags it before anyone has a chance to click.
- Behavioral Anomaly Detection: The AI learns the relationship between every person in your company, noticing subtle shifts in communication styles or unusual attachments that might signal an account has been taken over by a hacker.
- Autonomous Response: When a suspicious email arrives, the AI can take a variety of actions from simply "tagging" it as a warning to completely moving it to a quarantine folder so the employee never even sees it.
- Outbound Data Leak Prevention (DLP): This feature stops employees from accidentally sending sensitive data like credit card numbers or internal passwords to the wrong person, acting as a final safety check for tired remote workers.
- Account Takeover Protection: Darktrace monitors for unusual login patterns and administrative changes, catching hackers who have stolen an employee's credentials and are trying to use their email to spread malware internally.
- Cross-Domain Correlation: The AI connects signals from email with data from your cloud and network, allowing it to see the full "story" of an attack that might start with a simple message and end with a data breach.
Pricing: Darktrace pricing is generally quote-based depending on the number of mailboxes, but mid-sized teams can expect costs to range from $25 to $40 per user/year depending on the specific modules included.
Why it matters: Email is still the #1 way companies get hacked. Darktrace matters because it is the only tool fast enough to catch "AI vs. AI" phishing attempts, protecting your remote team from the human error of clicking on a very convincing fake message.
4. Okta Identity Cloud
Best for: Managing passwords and "Adaptive" Multi-Factor Authentication (MFA) for remote teams.
If your team is using "Password123" for everything, you are asking for trouble. Okta is the gold standard for Identity and Access Management (IAM). It uses AI to determine the "risk" of every login attempt. If someone tries to log in from a new device in a different country, Okta won't just ask for a password; it will trigger an extra layer of security to prove they are who they say they are.
- Single Sign-On (SSO): This allows your team to log into all their work apps with one secure account, reducing "password fatigue" and making it much easier for IT to revoke access if an employee leaves the company.
- Adaptive MFA: The AI analyzes the context of a login like the time of day, the location, and the device being used and only asks for extra verification when things look suspicious or high-risk.
- Lifecycle Management: This feature automatically creates (and deletes) user accounts across all your company’s apps as people join or leave the team, ensuring that no "ghost accounts" are left open for hackers to find.
- ThreatInsight: Okta uses data from its entire customer base to identify and block the IP addresses of known hackers before they even try to guess one of your employees' passwords.
- Identity Governance: This provides a clear audit trail of who has access to what, helping your company meet legal compliance standards and ensuring that "least privilege" is always maintained across the remote workforce.
Pricing: The "Essentials" tier, which most companies need for proper compliance and Adaptive MFA, is $17 per user/month (billed annually). Adding specialized modules like Governance can increase this to $25+ per user/month.
Why it matters: Identity is the new perimeter. Okta matters because it ensures that only the right person can get into your company's systems, regardless of where they are working from. It turns a messy collection of passwords into a single, highly secure gateway.
5. SentinelOne Singularity
Best for: High-speed, automated response to ransomware on remote devices.
SentinelOne is the speed demon of cybersecurity. It is designed to stop ransomware in its tracks before it can encrypt a single file. Using a "Behavioral AI" engine that runs directly on the laptop, it can detect an attack and "roll back" the computer to a healthy state automatically. For a remote team without local IT support, this "self-healing" capability is a lifesaver.
- Static and Behavioral AI: The tool uses two different AI engines, one that looks for known bad files and another that watches for suspicious activity to provide multiple layers of protection against both old and new threats.
- Automated Remediation: If a piece of malware does manage to run, SentinelOne can automatically kill the process, quarantine the file, and even disconnect the laptop from the network to prevent the infection from spreading.
- Ransomware Rollback: This is the "magic" feature that can restore files encrypted by ransomware back to their original state using a local backup, effectively making the attack useless without needing to pay a ransom.
- Full EDR Visibility: Despite being highly automated, the platform provides deep-dive data for security pros, showing exactly how an attack started and which files were touched, which is vital for legal reporting after an incident.
- Singularity Cloud: This extends the same level of protection to your company’s cloud servers and containers, ensuring that your remote team’s work is safe both on their laptops and in the data center.
Pricing: Singularity Core (the basic plan) starts at $69.99 per endpoint/year. The more popular Singularity Control is $79.99 per endpoint/year, while the full "Complete" tier with EDR and rollback is $179.99 per endpoint/year.
Why it matters: Ransomware moves too fast for humans. SentinelOne matters because it provides an autonomous "safety net" for remote employees who don't have an IT expert sitting next to them to fix things when something goes wrong.
6. Tessian (by Proofpoint)
Best for: Preventing "misdirected" emails and accidental data loss caused by human error.
We have all done it: started typing a name in the "To" field and accidentally sent a sensitive document to the wrong "John." Tessian uses AI to understand the "relationship graph" of your employees. If you try to send a financial report to someone you have never emailed before, Tessian will pop up a friendly warning asking, "Are you sure this is the right John?"
- Misdirected Email Prevention: The AI analyzes historical email patterns to catch those "oops" moments before they become a massive privacy breach, saving your remote team from embarrassing and costly mistakes.
- Architectural DLP: This goes beyond simple rules and uses machine learning to identify sensitive data within the body or attachments of an email, preventing it from being sent to personal accounts or unauthorized external parties.
- Spear Phishing Protection: Tessian identifies when an external email is "spoofing" a colleague’s name or using a look-alike domain, providing a clear warning to the remote worker that the sender is not who they claim to be.
- Executive Impersonation Detection: The AI specifically monitors for attacks targeting your leadership team, noticing when a hacker tries to "impersonate" a CEO to trick an employee into buying gift cards or sharing passwords.
- Human Layer Risk Dashboard: This provides leadership with a clear view of which employees are most at risk or making the most mistakes, allowing for targeted training instead of boring, company-wide lectures.
Pricing: Tessian is now part of Proofpoint and is generally sold as an add-on. Pricing typically lands between $30 and $55 per user/year depending on the specific "Defender" or "Enforcer" modules you choose to implement.
Why it matters: Remote workers are often more distracted than office workers. Tessian matters because it provides a "digital shoulder tap" that prevents simple human errors from turning into significant security liabilities for your remote-first business.
7. Vectra AI
Best for: Detecting hackers hiding in your cloud apps like Microsoft 365 or AWS.
Hackers love to steal a remote worker's login and then sit quietly inside their Microsoft 365 or Slack account to watch and wait. Vectra AI uses "Attack Signal Intelligence" to find these hidden intruders by watching their behavior. It doesn't care about passwords; it cares about what is happening inside your cloud apps, catching "authorized" users who are doing very "unauthorized" things.
- Microsoft 365 Detection: The AI specifically monitors your Outlook, Teams, and SharePoint accounts for signs of a takeover, such as a user suddenly setting up new "forwarding rules" to steal incoming emails.
- Privileged Access Monitoring: Vectra tracks your IT admins and power users, sounding the alarm if their accounts start performing unusual tasks that look like a hacker trying to escalate their control over the network.
- Cloud Detection and Response (CDR): This extends your security into AWS, Azure, and Google Cloud, identifying when someone is trying to steal data from your databases or change your cloud security settings.
- Automated Triage: The AI scores every threat from 1 to 100, allowing your security team to ignore the "junk" and focus only on the high-risk incidents that could actually cause a data breach.
- Network Detection and Response (NDR): For teams that still have some on-premise servers, Vectra monitors the "east-west" traffic to catch hackers trying to move between different computers in your digital estate.
Pricing: Vectra is an enterprise tool that is usually priced based on the volume of data or number of users. Expect a starting point of roughly $15,000 to $20,000 per year for mid-sized teams, scaling up significantly for larger cloud footprints.
Why it matters: When your team is remote, the "network" is just a collection of cloud apps. Vectra matters because it provides the "eye in the sky" needed to see if a hacker has bypassed your login screens and is currently living inside your company’s digital workspace.
Which one should you choose?
If you are a small startup on a budget, start with CrowdStrike Falcon Go for your laptops and Okta for simple SSO. These are the "must-haves" for basic survival. If you are a mid-sized team dealing with sensitive data, you absolutely need Darktrace / EMAIL and SentinelOne to handle the heavy lifting of automated defense. For large enterprises with complex cloud setups, Vectra AI and Zscaler are the professional choices that will keep your global workforce secure and compliant without slowing them down.
How does this connect to building a strong career or portfolio?
Understanding these tools is not just about keeping a company safe; it is about proving you are a modern, high-value professional. In 2026, every hiring manager wants to see "Proof of Work" that shows you can manage a remote-first security stack. If you can document how you rolled out Okta or managed a SentinelOne deployment, you aren't just an "IT person," you are a "Security Architect." Sharing these real-world projects in your portfolio is what moves you from the "maybe" pile to the "hired" pile, as it shows you have the practical, in-demand skills that actually solve business problems.
Final Thoughts
The remote work revolution is here to stay, but it has brought a whole new set of digital dangers with it. You cannot rely on 10-year-old security methods in a 2026 world. By integrating these AI-powered tools into your workflow, you aren't just checking a box for compliance; you are building a resilient, high-performance culture that respects the freedom of remote work while taking the risks seriously. Stay sharp, stay curious, and keep your "Proof of Work" updated as you master these new technologies.
FAQs
Are these AI security tools hard for remote employees to use?
Actually, most of them are "set it and forget it." Tools like CrowdStrike and SentinelOne run quietly in the background without bothering the user. The whole point of these 2026 AI tools is to provide security that is invisible, so your team can focus on their actual work rather than fighting with security pop-ups.
Can I use these tools on personal laptops (BYOD)?
Yes, most of these platforms are designed for "Bring Your Own Device" environments. They can protect the company's work apps and data on a personal laptop without spying on the employee's private photos or messages, which is a big win for both security and privacy.
Do these tools work if my remote team has bad internet?
Most of them do! Tools like SentinelOne and CrowdStrike have "local" AI engines that run on the laptop itself, meaning they can still block a virus even if the employee is offline. They will simply "report back" to the cloud once the connection is restored.
Is the "SSO Tax" something I should worry about?
Yes, it is a real thing. Many SaaS apps charge extras, sometimes double or triple, to allow you to connect them to tools like Okta. When budgeting for your security stack, always check the "Enterprise" or "Pro" pricing of your favorite apps to see if they charge a premium for SSO.
How often should I update these AI security tools?
The beauty of "cloud-native" AI tools is that they update themselves. You don't have to worry about manual patches or "version 2.0" downloads. The AI is constantly learning from the global network, so your remote team always has the most up-to-date protection available.
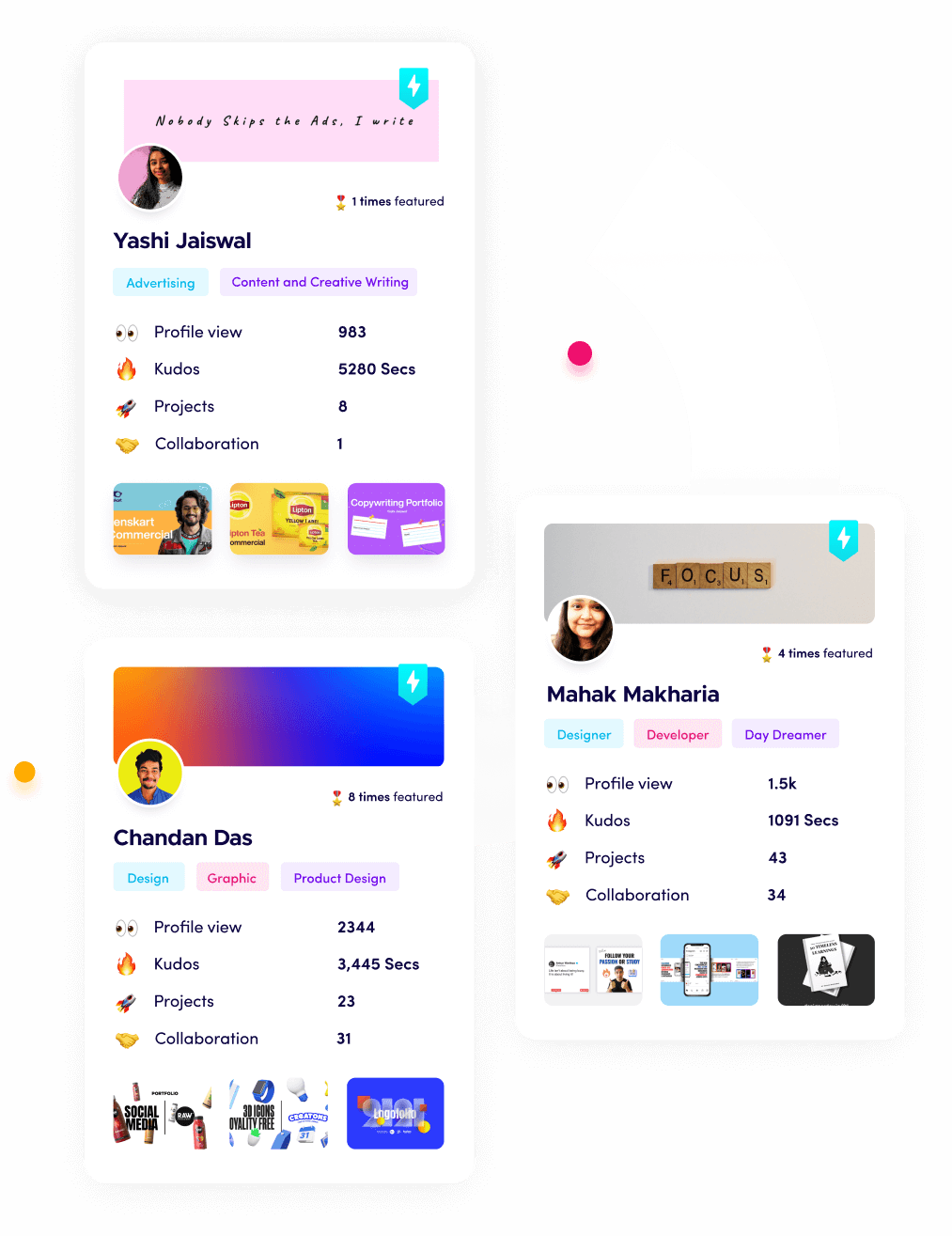
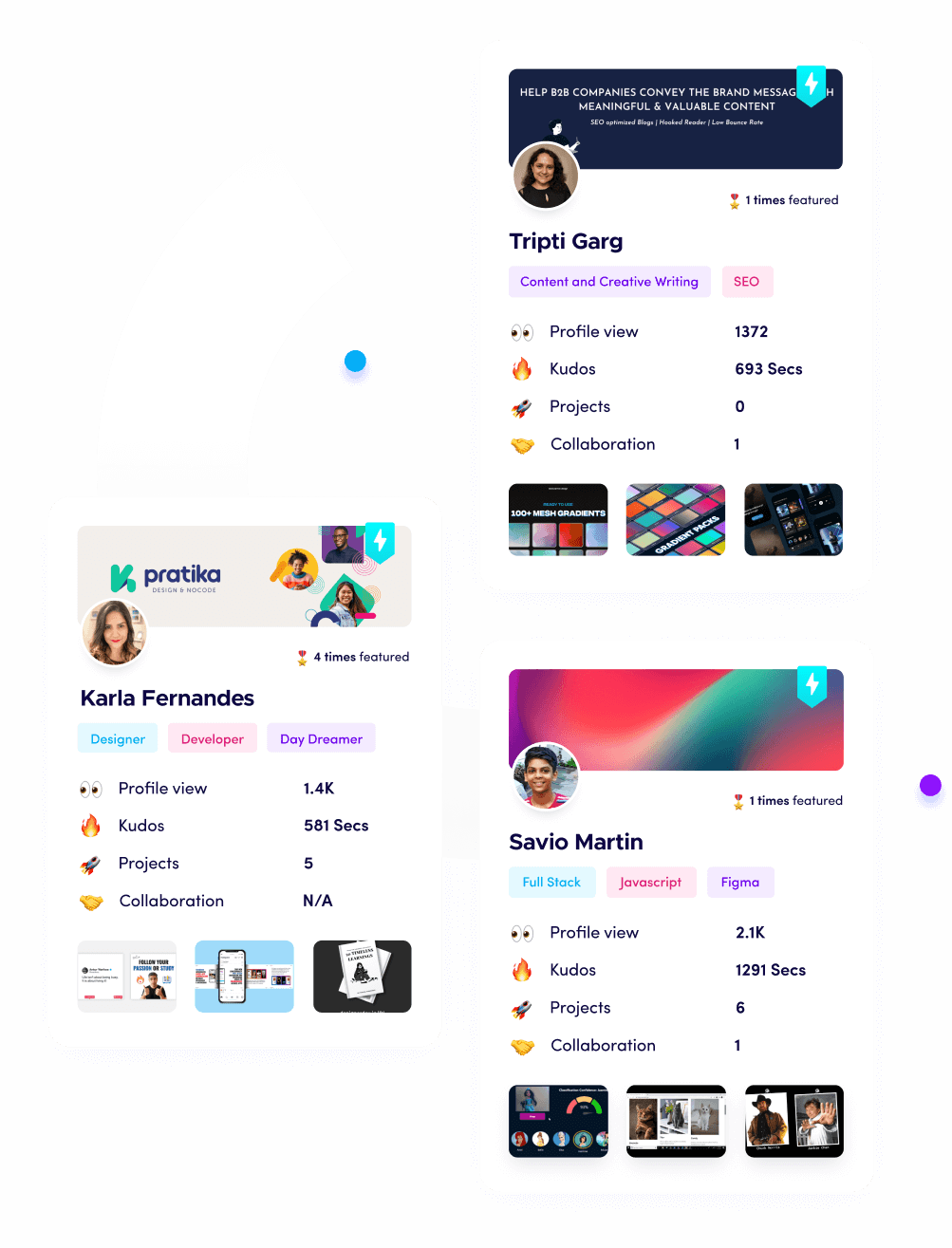
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.