10 AI Tools That Improve Digital Security in 2026

Riten Debnath
30 Apr, 2026

Last updated: April 2026
If you think your digital life is safe just because you don't click on "You've won an iPhone" ads, you are living in a beautiful, dangerous dream. In 2026, cyber-attacks aren't just emails from fake princes; they are invisible, AI-powered ghosts that can mimic your boss's voice on a Zoom call or slowly drain your company's data while you're sleeping. If you’re still relying on basic passwords and "gut feelings," you’re essentially trying to stop a bullet with a paper shield.
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
The New Reality of Digital Defense
The game has changed. Cybersecurity is no longer about building a "wall" around your data; it’s about having an "intelligence agency" inside your network. Hackers are now using generative AI to create thousands of unique attack variants every hour. Traditional antivirus software, which waits to see a "known" virus before acting, is officially obsolete.
Today’s best tools use behavioral AI. They don't care what a file looks like; they care about what a file does. If a document starts trying to change your system settings or an "employee" logs in from three different countries in ten minutes, the AI acts instantly. To stay safe in 2026, you need tools that think faster than the criminals. Here are the 10 best AI-driven defenders currently leading the market.
At a glance: Comparing the AI Tools That Improve Digital Security
1. Cynet 360 AutoXDR
Best for: Small to mid-market organizations needing a "fully automated" security team in a single box.
Cynet is a game-changer for companies that don't have a 50-person security department. It combines endpoint protection, network monitoring, and user behavior analysis into one platform. Its "AutoXDR" technology doesn't just find threats; it automatically "hunts" for them across your entire digital environment, fixing holes before you even know they exist.
Key Features:
- Automated Remediation Playbooks: The system doesn't just alert you to a virus; it automatically follows a pre-set "playbook" to kill the process, delete the file, and clean the registry without human intervention.
- 24/7 Managed Detection (CyOps): Every subscription includes access to a professional human security team that monitors your alerts around the clock, providing an extra layer of "expert" eyes on your data.
- Identity Protection (ITDR): The AI monitors user login patterns and can instantly flag or block "account takeovers" where a hacker has stolen an employee's credentials to sneak inside.
- Deception Technology: It scatters "honeypots" (fake files and passwords) across your network to lure hackers into a trap, allowing the AI to identify and block them the second they touch the bait.
- Vulnerability Management: It automatically scans all your connected devices for outdated software or weak configurations, giving you a prioritized "to-do" list to harden your defenses.
Pricing: $10 per endpoint per month for the "All-In-One" tier, with a 20-endpoint minimum ($200/month floor).
Why it matters: It provides a "complete security team" experience for a fraction of the cost of hiring a single specialist, making it the ultimate value choice for growing businesses.
2. Arctic Wolf MDR
Best for: Businesses that want a "Concierge" security service that manages everything for them.
Arctic Wolf isn't just software; it is a Managed Detection and Response (MDR) service. They install their AI sensors across your network, cloud, and devices, and then their experts manage it for you. It’s perfect for the "I just want to be safe" business owner who doesn't want to look at a single technical dashboard.
Key Features:
- Concierge Security Team: You are assigned dedicated security researchers who learn your business inside and out, providing personalized advice and monthly "security posture" reviews.
- 24/7 Continuous Monitoring: Their AI-powered "Security Operations Center" (SOC) never sleeps, ensuring that a middle-of-the-night ransomware attack is caught and stopped in minutes, not hours.
- Managed Risk Scanning: The system continuously hunts for "internal" risks, like employees using unauthorized apps or sensitive files being shared publicly on Google Drive or Dropbox.
- Cloud Detection and Response: It extends its AI "eyes" into your AWS, Azure, and Microsoft 365 environments, ensuring your cloud data is just as safe as your office servers.
- Security Awareness Training: Included in the service is automated training for your employees, using AI to send "fake" phishing emails to see who clicks and needs more education.
Pricing: Typically ranges from $12 to $18 per endpoint per month for mid-sized deployments, with annual minimums often starting around $25,000.
Why it matters: It shifts the responsibility of security from your shoulders to theirs, giving you an enterprise-level safety net without the enterprise-level headache.
3. Mimecast Email Security (AI-Powered)
Best for: Stopping "Deepfake" business emails and sophisticated social engineering attacks.
Email is still the #1 way hackers get into companies. Mimecast uses advanced AI to analyze the "sentiment" and "intent" of every email. It can spot if an email is a "Deepfake" designed to sound like your boss or if a link is a "delayed-action" trap that only becomes malicious after it passes through your initial filters.
Key Features:
- AI Impersonation Protect: The AI scans for subtle signs that an email is fake, such as a slightly different "tone" of voice or a hidden sender address that mimics your company’s domain perfectly.
- CyberGraph Visual Graphs: It creates a "social map" of your email interactions, highlighting any "stranger" who is trying to force their way into a sensitive conversation or thread.
- Attachment Sandboxing: Every file sent to you is opened by the AI in a "virtual bubble" first to see if it tries to do anything malicious before it ever touches your actual computer.
- Browser Isolation: If an employee clicks a suspicious link, Mimecast opens the site in a remote, isolated browser so that any malware on the page can't actually reach the user’s device.
- DMARC Analyzer: It prevents hackers from "spoofing" your own company's email address to attack your customers, protecting your brand's reputation and your email deliverability.
Pricing: The "Advanced" tier for mid-market teams (500+ users) costs roughly $4.00 to $7.20 per user per month.
Why it matters: It stops the "human" side of hacking, where your employees are tricked into giving away data by acting as a high-tech "truth filter" for your inbox.
4. Akamai Guardicore Segmentation
Best for: Stopping "Lateral Movement" (when a hacker gets in and tries to move from computer to computer).
Guardicore is like building a series of air-locked rooms inside your office. If a hacker manages to infect one laptop, the AI "Segmentation" prevents them from seeing or touching any other device on the network. It uses AI to automatically "label" every piece of software in your company so it knows exactly who should be talking to whom.
Key Features:
- AI-Driven Policy Recommendations: You don't have to be a networking genius; the AI studies your traffic and suggests "security rules" that will protect your data without breaking your workflow.
- Real-Time Visual Map: It provides a "living" map of every single connection in your company, showing you exactly how data is moving between your office, the cloud, and your remote workers.
- Identity-Based Security: Rules are tied to the person, not the IP address, meaning your security settings follow you whether you are in the office or working from a beach in Bali.
- Incident Response Isolation: With one click, you can "freeze" an infected server or laptop, completely cutting it off from the rest of the company while you clean it up.
- Agentless Visibility: It can see and protect "dumb" devices like office printers, smart cameras, and IoT sensors that can't run traditional security software but are often used as back doors by hackers.
Pricing: Custom quotes, but typically ranges from $30 to $50 per workload/server per month for large enterprise environments.
Why it matters: It turns a "total network failure" into a "minor local issue" by ensuring that an infection can never spread beyond the first device it touches.
5. Rapid7 InsightIDR
Best for: Rapid "Incident Response" and finding the "needle in the haystack" in your security logs.
InsightIDR is a Cloud-Native SIEM (Security Information and Event Management) tool. It sucks in all the "boring" data from your entire company's firewalls, laptops, cloud apps, and uses AI to find the one small anomaly that points to a hack. It’s designed to tell you exactly what happened in plain English so you can fix it fast.
Key Features:
- User and Entity Behavior Analytics (UEBA): The AI builds a profile for every employee; if "Dave from Accounting" suddenly starts looking at "HR Salary Folders" at midnight, the system alerts you instantly.
- Centralized Log Management: It gathers every digital "footprint" left in your company and stores them in one searchable place, making it easy to track a hacker's movements after a breach.
- Visual Investigation Timelines: Instead of looking at thousands of lines of code, you get a clean, visual "storyboard" showing exactly how an attack started and where it went.
- Deception Tools: Like Cynet, it includes "Honey Credentials" and "Honey Files" that trigger an immediate, high-priority alert the moment a hacker tries to use or open them.
- Cloud-Native Architecture: There is no hardware to install; the entire system lives in the cloud and can be set up to monitor your company in just a few hours.
Pricing: Starts at roughly $5.89 per user per month for the Advanced tier.
Why it matters: It cuts through the "noise" of modern tech, ensuring that your team isn't distracted by 1,000 fake alerts and only sees the threats that actually matter.
6. Exabeam New-Scale Fusion
Best for: Large enterprises that need to automate their "Threat Detection, Investigation, and Response" (TDIR).
Exabeam is the "detective" of the security world. It is built on the idea that "normal" behavior is the best baseline for security. Its AI creates a "Timeline" for every single user and device in your company. If a hacker tries to "low and slow" their way into your data over several weeks, Exabeam's AI will spot the pattern that humans would miss.
Key Features:
- Automated Smart Timelines: The AI automatically builds a chronological history of every event related to a specific user, so you can see a "movie" of what a suspect did across your entire network.
- Advanced Anomaly Detection: It doesn't look for "bad files"; it looks for things that are "unusual for this user," which is the most effective way to catch insider threats or stolen accounts.
- Outcome-Based Security: It comes with pre-built "packages" for specific threats like Ransomware or Phishing, so the AI knows exactly what to look for based on the current global threat landscape.
- Massive Scale Ingest: It can handle trillions of data points per day, making it the perfect choice for giant corporations that generate massive amounts of digital "noise."
- Playbook Automation: It integrates with hundreds of other tools to automatically "lock" accounts or "block" IPs the moment a high-risk timeline is detected.
Pricing: Enterprise-grade pricing starting at $75,000 per year for the full Fusion suite.
Why it matters: It is designed for the most complex digital environments, ensuring that "big data" doesn't become a "big blind spot" for your security team.
7. LogRhythm Axon
Best for: Security teams who want a "simplified" cloud-native view of their entire organization.
LogRhythm Axon was built by security analysts, for security analysts. It’s a SaaS platform that focuses on making the "investigation" part of security as easy as possible. Its AI is tuned to help you "see" the truth in your data without having to learn complex "query languages" or coding.
Key Features:
- Interactive Single-Screen Investigation: You can see your alerts, your data logs, and your "case management" notes all on one screen, meaning you never have to "tab-hop" during a high-pressure security event.
- MITRE ATT&CK Mapping: The AI automatically labels every threat with the specific "hacker technique" being used (based on the global MITRE framework), so you know exactly what kind of criminal you are fighting.
- Custom Policy Builder: You can create your own "security rules" using a simple "drag and drop" interface, allowing the AI to look for the specific risks that are unique to your industry.
- Bi-Weekly Feature Updates: Because it is a 100% cloud-based tool, LogRhythm pushes out new AI models and detection rules every two weeks to keep up with the latest hackers.
- Predictable Pricing: Unlike many "SIEM" tools that charge you based on how much data you upload, Axon uses a more predictable model so your bill doesn't explode during a busy month.
Pricing: Custom quotes only, but generally positioned to compete with Rapid7 in the $10,000 - $30,000+ per year range for mid-sized organizations.
Why it matters: It removes the "technical barrier" to high-end security, allowing a regular IT person to perform like a world-class cybersecurity expert.
8. Cybereason Defense Platform
Best for: Seeing the "Full Story" of a malicious operation across every device in your company.
Cybereason is famous for its "Malop" (Malicious Operation) engine. While other tools show you "Alerts," Cybereason shows you "Operations." It uses AI to connect 10 different "small" alerts into one "big" story, showing you exactly where the hacker started, what they are doing right now, and what their next move will be.
Key Features:
- Malop Visualization: Instead of a list of text, you get a visual "web" that shows how a hacker moved from an email to a laptop to your server, making the entire attack easy to understand at a glance.
- Cross-Machine Correlation: The AI "talks" to every device on your network simultaneously, ensuring that a hacker can't "hide" by moving from one machine to another.
- Predictive Ransomware Protection: It uses "behavioral baiting" to trick ransomware into revealing itself before it can encrypt your first file, allowing the AI to kill the attack in its infancy.
- Binary Analysis: The AI looks at the "intent" of every piece of software on your machine, blocking apps that try to do things they weren't designed to do (like a "Calculator" app trying to access the internet).
- Automated Investigation: It automatically answers the "Who, What, When, Where, and Why" for every attack, saving your team hours of manual research time.
Pricing: Custom quotes, typically structured as a per-endpoint subscription ranging from $40 to $100 per device per year.
Why it matters: It stops you from playing "Whack-a-Mole" with alerts and helps you see and stop the entire attack strategy in one go.
9. Broadcom Symantec Endpoint Security (SES)
Best for: Established businesses that want a "tried and true" name with modern AI upgrades.
Symantec has been around forever, but don't let that fool you. Their modern "SES Complete" platform uses some of the most advanced AI in the world. It’s particularly good at "Attack Surface Reduction," essentially using AI to "harden" your computer so that 90% of a hacker's favorite tools simply don't work on your machine.
Key Features:
- Intelligent Threat Defense: The system uses "Deceptive" techniques and machine learning to block malware, memory exploits, and "living-off-the-land" attacks that use your computer's own tools against you.
- Breach Assessment: The AI continuously "simulates" attacks against your own computers to find your weak spots before a real hacker does.
- Adaptive Protection: The system automatically changes its "strictness" based on the threat level; if a new global virus is spreading, the AI makes your defenses tougher until the danger passes.
- Network Integrity: It monitors your Wi-Fi connections for "Man-in-the-Middle" attacks, ensuring that no one is spying on your data when you’re working from a public cafe or airport.
- Mobile Threat Defense: It provides a dedicated app for your work phones that uses the same AI-brain to protect against malicious apps and "SMS-Phishing" (Smishing).
Pricing: Starts at roughly $34.99 per device per year for basic cloud protection (1-99 devices).
Why it matters: It combines a massive global database of threats with modern, "thinking" software, giving you a very stable and reliable shield for your business.
10. Trellix Helix
Best for: Large-scale "Security Orchestration" and connecting hundreds of different tools into one AI-brain.
Trellix Helix is the "Command Center" for your security world. If you already use 20 different security tools, Trellix Helix uses AI to "orchestrate" them, making them work together as one giant, unified system. It’s perfect for the "Security Professional" who needs to manage a massive and complex tech stack.
Key Features:
- Open XDR Architecture: It can talk to over 600 different third-party security tools, meaning you don't have to throw away your existing software to get the benefits of Trellix’s AI.
- Collective Analytics Layer: The system shares "anonymous" threat data with other Trellix users around the globe, ensuring that everyone is protected from a new attack the second it is first seen.
- Automated Phishing Handling: The AI can automatically "read" and "remediate" thousands of reported phishing emails a day, saving your IT team from the most boring part of their job.
- Flexible Playbook Builder: You can create complex "if-this-then-that" rules for your security, allowing the AI to handle everything from minor glitches to massive breaches automatically.
- Dynamic Threat Intelligence: It constantly updates its "knowledge base" from the world's most elite security researchers, ensuring your AI is always up to date on the latest hacker trends.
Pricing: Custom enterprise quotes; however, entry-level Trellix endpoint suites can start around $795 per user per year for full protection bundles.
Why it matters: It is the "glue" that holds your security together, ensuring that your different tools aren't working in silos and missing the big picture.
Which One Should You Choose?
The "best" tool is the one that fits your team's size and technical skills:
- If you are a small business with NO IT team: Go with Cynet 360 AutoXDR or Arctic Wolf MDR. They do the work for you.
- If you are a Microsoft 365 user on a budget: Stick with Microsoft Defender for Business (from Title 1), but add Mimecast for better email safety.
- If you are a large company with complex needs, Exabeam Fusion or Trellix Helix will give you the "Command Center" you need to stay in control.
- If you are terrified of a data breach spreading, Akamai Guardicore is the best "insurance" you can buy for your internal network.
How This Connects to Your Career and Portfolio
You might be asking, "Riten, I’m a freelancer/professional, do I really need to know about 'Enterprise XDR'?"
The answer is YES. In 2026, clients aren't just buying your "work"; they are buying your "reliability." When you build your profile on Fueler, you are building a record of trust. If you can show a potential client that you understand the "Security-First" approach, and that you use tools like these to protect the projects you build, you instantly become a high-value hire.
Think about it: who would you hire? The developer who just builds the app, or the developer who builds the app and can explain how they protected the client's source code from being leaked? On Fueler, we help you showcase these "hidden" professional skills through your work samples, making it clear that you are a top-tier professional who understands the modern digital landscape.
Final Thoughts
Digital security in 2026 isn't a "luxury" for big banks anymore; it is a basic requirement for anyone who works online. The tools listed above represent the absolute cutting edge of how we protect our hard work from an increasingly aggressive digital world. Whether you choose a "set it and forget it" service like Arctic Wolf or a "do it yourself" powerhouse like SentinelOne, the goal is the same: stay one step ahead of the threat. Invest in your safety today so you can focus on building your career and your legacy tomorrow.
FAQs
1. Is AI security expensive for a 10-person company?
Not at all. Tools like Cynet or CrowdStrike offer small business plans that cost less than a few cups of coffee per employee per month. It is much cheaper than the cost of a single data breach.
2. Can these tools stop a "Deepfake" voice or video?
Email security tools like Mimecast are getting very good at spotting the "markers" of AI-generated content. While no tool is 100% perfect, they provide a much stronger filter than a human eye ever could.
3. What is "XDR" anyway?
XDR stands for "Extended Detection and Response." It basically means the security tool looks at everything (email, cloud, network, and laptops) at the same time, rather than just looking at one thing in isolation.
4. Do I need these if I only use a Chromebook or a Tablet?
Yes. While these devices are generally "safer," hackers now target your identity (your passwords and accounts) rather than your device. AI tools like Mimecast and Cynet protect your accounts no matter what device you use to log in.
5. How do I add my "Security Skills" to my Fueler portfolio?
You can mention your "Security-First Workflow" in your project descriptions. For example, "Built this web app using Zero-Trust principles and verified all code against modern AI-threat databases." This shows clients you are a professional who thinks beyond just the "pretty" parts of a project.
What is Fueler Portfolio?
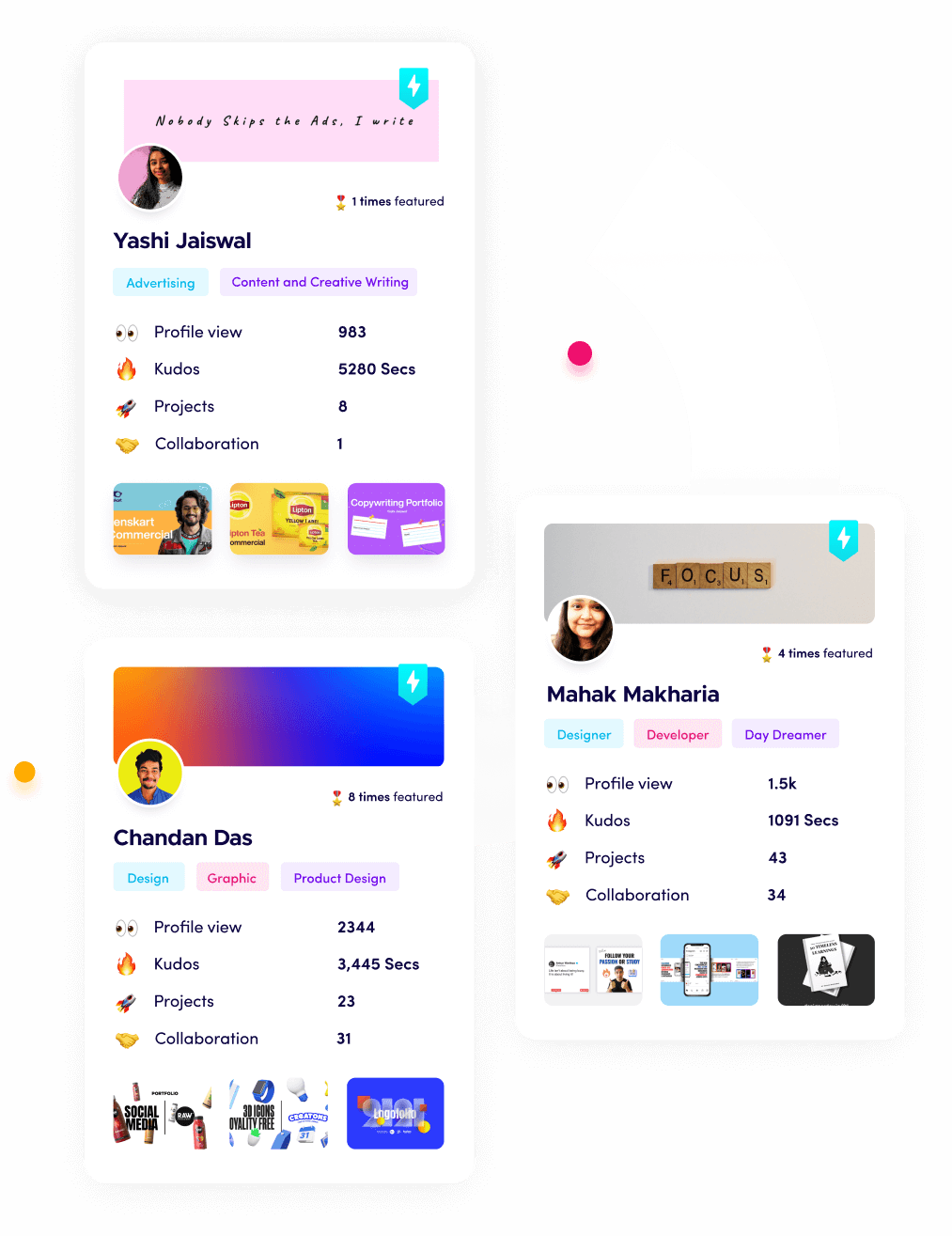
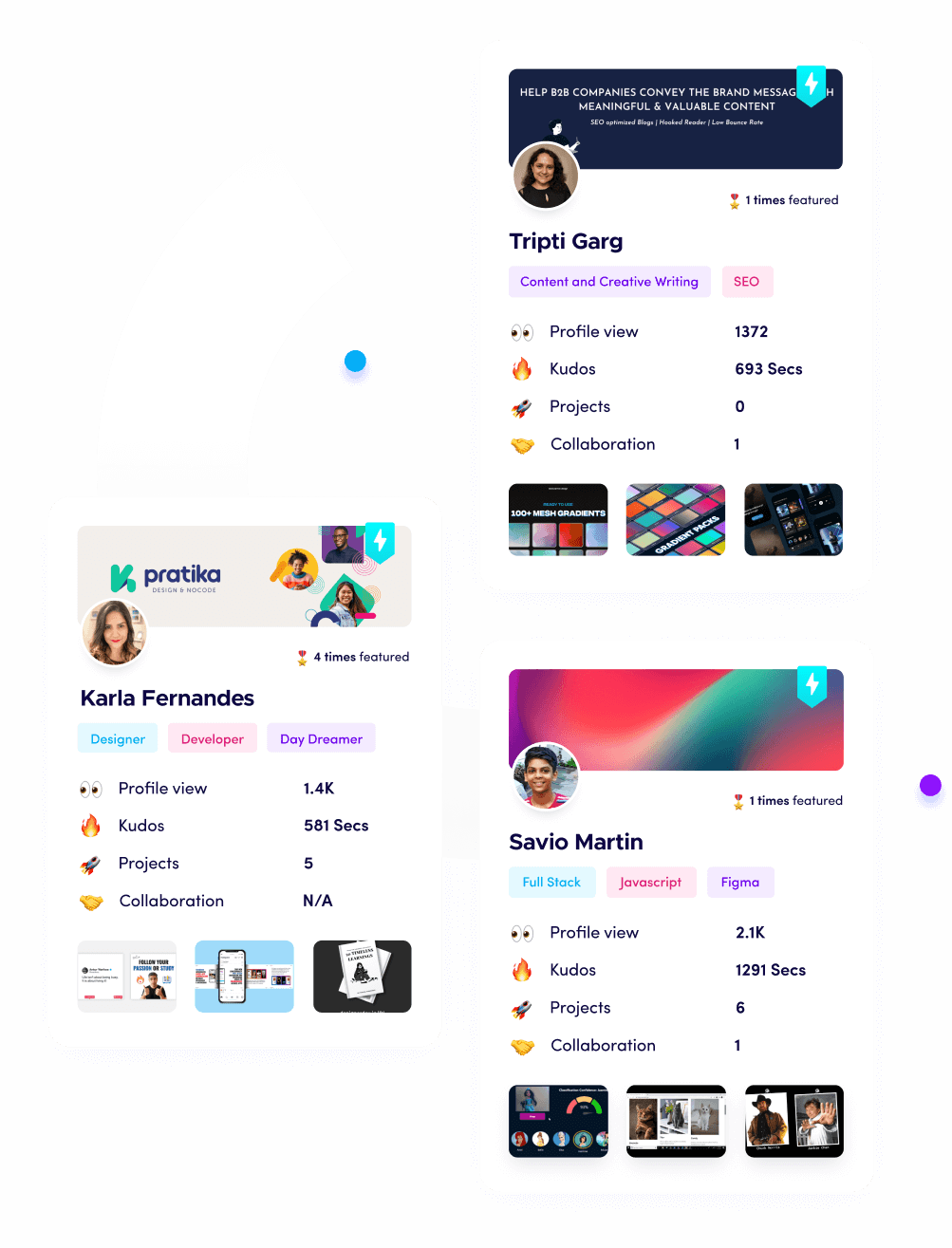
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.