8 AI Tools That Help Reduce Security Risks

Riten Debnath
30 Apr, 2026

Last updated: April 2026
In the world of high-stakes security, the "latest trend" is rarely as effective as a battle-tested shield that has survived a decade of real-world combat.
Security isn't about having the most buttons to press; it’s about having the right ones. If you've ever felt the panic of a server going down or a suspicious login at 2:00 AM, you know that a "smart" tool that guesses isn't nearly as valuable as a rock-solid system that acts. Reducing security risks requires a return to the fundamentals of identity, infrastructure, and ironclad encryption. When you strip away the marketing fluff, you're left with tools that don't just "detect" problems, but actually build a digital environment where those problems can't exist in the first place.
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
At a glance: Comparing the AI Tools That Help Reduce Security Risks
1. Okta Workforce Identity Cloud
Best for: Unified identity management and preventing unauthorized account access.
Okta is the gold standard for Identity and Access Management (IAM). Instead of every employee having twenty different passwords for twenty different tools, Okta provides one secure "front door." It ensures that only the right people have access to the right data at the right time. By centralizing login control, you eliminate the risk of a "ghost" employee still having access to your company files months after they’ve left the team.
- Single Sign-On (SSO) Centralization: It allows your team to access all their work applications with one secure login, drastically reducing the "password fatigue" that often leads employees to use weak, easily guessable passwords across multiple sensitive accounts.
- Adaptive Multi-Factor Authentication (MFA): This feature goes beyond simple text codes by analyzing the user's location, device, and network, automatically challenging suspicious login attempts with extra security steps if the behavior looks out of the ordinary.
- Automated Lifecycle Management: When a new person joins or leaves your company, Okta can automatically create or delete their accounts across hundreds of different apps like Slack, Jira, and Zoom, ensuring no "backdoor" access remains for former staff.
- Deep Security Insights and Reporting: It provides a granular audit trail of exactly who logged in, when they did it, and what applications they accessed, which is critical for identifying potential account takeovers before they turn into full data breaches.
- Seamless API Access Management: Beyond just humans, Okta secures the way different software programs talk to each other, ensuring that only authorized internal systems can exchange sensitive data without exposing it to the open web.
Pricing: $6.00 USD per user/month for the "Starter" plan, $17.00 USD for "Essentials," and up to $70.00 USD per user/month for the "Essential Suite" including governance.
Why it matters: Most data breaches start with a stolen password. Okta reduces this risk by making passwords nearly irrelevant through strong authentication and centralized control, making it a mandatory piece of any modern security workflow.
2. Palo Alto Networks Next-Generation Firewall (NGFW)
Best for: Comprehensive network perimeter defense and deep packet inspection.
While a basic firewall just looks at where data is coming from, a Palo Alto Next-Generation Firewall actually looks at what the data is. It acts as a highly intelligent border guard that can tell the difference between a legitimate file transfer and a hidden piece of malware disguised as an image. It provides the deep visibility needed to block sophisticated attacks that try to sneak past traditional defenses.
- Layer 7 Application Visibility: Unlike older firewalls that only see port numbers, this tool identifies exactly which apps are running on your network, allowing you to block risky personal apps while keeping critical business tools open and safe.
- Integrated Threat Prevention: It combines antivirus, anti-spyware, and vulnerability protection into a single engine, meaning it can stop a wide variety of network attacks in one go without slowing down your internet speed.
- WildFire Sandbox Analysis: When the firewall sees a file it doesn't recognize, it sends it to a secure "sandbox" to run it and see if it behaves like a virus before ever letting it reach your employees' computers.
- URL Filtering with Categories: It gives you the power to block entire categories of dangerous websites, such as known phishing sites or unrated domains, significantly reducing the chance of an employee accidentally clicking a malicious link.
- GlobalProtect Remote Access: It extends the same high level of corporate security to your remote workers, ensuring that even when someone is working from a coffee shop, their traffic is still protected by the company's main firewall.
Pricing: Physical hardware units range from $5,000 USD to over $200,000 USD, while virtual subscriptions typically cost between $8,000 USD and $20,000 USD per year depending on the model and features.
Why it matters: Reducing security risks is impossible if you don't control the flow of data into your company. This tool provides the "muscle" needed to physically block threats at the entrance, ensuring they never touch your internal servers.
3. Zscaler Internet Access (ZIA)
Best for: Securing remote workforces and providing a "Cloud-First" security perimeter.
Zscaler is a leader in "Security as a Service." Instead of forcing all your remote employees to connect to a slow office VPN, Zscaler puts a secure "security cloud" between your employees and the internet. No matter where in the world your team is, their internet traffic goes through Zscaler first to be cleaned of viruses and checked for data leaks.
- Cloud-Native Web Gateway: It replaces traditional on-premise security hardware with a global cloud network, ensuring that security policies are applied consistently to every employee, whether they are in the office or on a beach.
- In-Line Data Loss Prevention (DLP): The tool monitors all outgoing data in real-time, preventing employees from accidentally (or intentionally) uploading sensitive files like credit card lists or private code to public websites or cloud storage.
- Sandboxing for Unknown Threats: Just like a physical firewall, Zscaler captures unknown files and tests them in a secure environment to ensure they aren't "zero-day" threats that your antivirus software hasn't learned about yet.
- Advanced Cloud Browser Isolation: For particularly risky websites, Zscaler can run the site in a "disposable" browser in the cloud, only sending a visual image to the user, which makes it impossible for the website to infect the user's actual computer.
- Comprehensive Bandwidth Control: It allows you to prioritize business-critical traffic like Microsoft Teams or Zoom over recreational traffic like YouTube, ensuring your security tools don't interfere with the productivity of your team.
Pricing: ZIA entry-level plans start at approximately $72.00 USD per user/year, while full enterprise editions with advanced security can reach over $325.00 USD per user/year.
Why it matters: In the age of remote work, the "office" no longer has walls. Zscaler reduces security risks by moving the protection to the cloud, following your employees wherever they go and ensuring they are always behind a professional-grade shield.
4. HashiCorp Vault
Best for: Securely managing "secrets" like passwords, API keys, and certificates for developers.
In the world of coding, developers often accidentally leave "secrets" (like database passwords) inside their code. If a hacker sees that code, they have the keys to everything. HashiCorp Vault solves this by acting as a high-security safe for these secrets. Instead of writing the password in the code, the code asks Vault for the password only when it is needed, and Vault can even change the password every few minutes.
- Dynamic Secret Generation: This is a game-changer; Vault can create a temporary password for a database that only works for thirty minutes and then automatically deletes it, making stolen credentials almost useless to a hacker.
- Centralized Secret Management: It provides one single location for all your company’s API keys, encryption keys, and passwords, replacing the dangerous habit of storing them in spreadsheets, sticky notes, or Slack messages.
- Data Encryption as a Service: Instead of developers having to learn complex math to encrypt data, they can simply send the data to Vault, which will encrypt it using professional standards and send it back, ensuring data is always safe.
- Detailed Lease and Revocation: Every time a secret is used, Vault tracks it. If you suspect a breach, you can click one button to "revoke" every active password in the company, instantly locking out any potential intruders.
- Strict Role-Based Access Control: You can set very specific rules so that only the "Billing App" can see the credit card keys, while the "Marketing App" has no way of even knowing those keys exist in the system.
Pricing: A "HCP Vault Dedicated" cluster for about 50 clients starts at approximately $51,000 USD list price annually, though negotiated deals can bring this down significantly to around $13,500 USD for smaller teams.
Why it matters: Reducing security risk in software development is all about "Secret Management." Vault ensures that even if your code is stolen, your actual data remains locked behind a door that only opens for a few seconds at a time.
5. Rapid7 InsightVM
Best for: Automated vulnerability management and prioritizing which bugs to fix first.
InsightVM is like a 24/7 building inspector for your digital infrastructure. It constantly scans your computers and servers to find "vulnerabilities" (weak spots like outdated software). What makes it special is that it doesn't just give you a long list of problems; it tells you which ones are actually being used by hackers right now, so you know exactly what to fix first.
- Live Monitoring via Insight Agent: This small piece of software stays on your computers and provides real-time updates on their security status, meaning you don't have to wait for a "weekly scan" to find a new problem.
- Real-Risk Prioritization: It uses a sophisticated scoring system that looks at how easy a bug is to exploit and whether hackers are currently talking about it on the dark web, helping your team focus on the most dangerous threats.
- IT-Integrated Remediation Projects: It allows you to create "to-do lists" for your IT team directly within the tool, making it much easier to track the progress of fixing security holes across thousands of different computers.
- Cloud and Container Assessment: As your business moves to the cloud, InsightVM moves with you, scanning your Amazon AWS or Google Cloud environments to ensure your virtual servers are just as safe as your physical ones.
- Policy Compliance Auditing: It checks your systems against global security standards like CIS or NIST, providing you with the exact proof you need to show auditors that your company is following the best possible security rules.
Pricing: Pricing is based on the number of "assets" (computers) being scanned. For 250 assets, the list price is roughly $2.20 USD per asset/month, totaling about $6,600 USD per year.
Why it matters: You can't fix a hole you don't know exists. InsightVM improves your workflow by turning a mountain of scary technical data into a clear, prioritized checklist that keeps your risk levels as low as possible.
6. Cisco Umbrella
Best for: DNS-layer security and blocking malicious websites before they even load.
Cisco Umbrella is often the first line of defense for a company. It works at the "DNS" level, the system that translates website names (like google.com) into IP addresses. When an employee tries to visit a site that Cisco knows is dangerous, Umbrella simply refuses to connect them. It’s like having a GPS that refuses to drive you into a high-crime neighborhood.
- DNS-Layer Threat Blocking: By stopping threats at the very first step of an internet connection, it prevents malware from ever reaching your network or endpoints, stopping the attack before it even officially begins.
- Selective Web Proxy: For websites that aren't "known bad" but look suspicious, Umbrella can route the traffic through a deeper inspection engine to check for hidden files or dangerous code without slowing down your entire internet.
- Shadow IT Discovery: It provides a detailed list of every cloud app your employees are using, allowing you to see if people are storing company data in unapproved personal Dropbox or Evernote accounts.
- Off-Network Protection: When employees take their laptops home, Umbrella stays active, ensuring that a virus they catch on their home WiFi doesn't follow them back into the corporate office the next day.
- Incredibly Fast Deployment: Because it works at the DNS level, you can protect an entire company of thousands of people in less than thirty minutes just by changing one setting in your network router.
Pricing: "DNS Security Essentials" typically costs between $2.25 USD and $3.75 USD per user/month, while the "Secure Internet Gateway" tier ranges from $5.50 USD to $8.00 USD per user/month.
Why it matters: Most hacks require a "call home" to a hacker's server. Cisco Umbrella cuts that phone line. It is a simple, highly effective way to reduce security risk by making sure your computers never even talk to the bad guys.
7. Varonis Data Security Platform
Best for: Protecting sensitive files and monitoring who is touching your most private data.
Varonis focuses on the "Data" itself. Most companies have millions of files, and they have no idea who is reading them. Varonis watches your file servers and cloud storage (like OneDrive or Google Drive) and alerts you if someone starts downloading files they've never looked at before. It is essentially a security camera for your digital filing cabinets.
- Data Classification Engine: It automatically crawls through your millions of files to find exactly where your "sensitive" data is like spreadsheets containing credit card numbers or secret project plans so you know what needs the most protection.
- Least Privilege Automation: The tool identifies employees who have access to files they don't actually need for their jobs and can automatically "lock" those folders, ensuring that a single hacked account can't see the whole company.
- User Behavior Analytics (UBA): It builds a "profile" for every employee. If a quiet accountant suddenly starts deleting thousands of files or accessing the CEO's private folder, Varonis will trigger an instant high-priority alarm.
- Permission Visibility Maps: It provides a visual "map" of who can see what, making it easy for managers to see at a glance if a folder is "over-exposed" to the entire company or even the public internet.
- Automated Data Protection: It can be set to automatically "quarantine" sensitive files that are found in the wrong place, moving them to a secure location until a security professional can review why they were there.
Pricing: Varonis uses a quote-based model, but for mid-sized organizations, typical starting costs for the SaaS platform are in the range of $15,000 USD to $50,000 USD per year depending on the data volume.
Why it matters: Hackers don't want your computers; they want your data. Varonis reduces risk by putting a "smart lock" on every single file, ensuring that your most private information stays that way, even if someone gets inside your network.
8. Check Point Harmony Endpoint
Best for: Preventing ransomware and securing individual employee laptops.
Harmony Endpoint is a "complete" security package for the actual computers your employees use. While traditional antivirus only looks for old viruses, Harmony includes specific tools to stop "Ransomware" (where a hacker locks your files and demands money). If it detects a ransomware attack, it can actually "roll back" the files to their original state, making the hack useless.
- Anti-Ransomware with Auto-Recovery: If a hacker starts encrypting your files, Harmony detects the behavior, kills the virus, and automatically restores the encrypted files from a hidden, protected backup.
- Zero-Phishing Protection: It inspects every website an employee visits in real-time, blocking "copycat" sites that try to steal passwords, even if the site is only a few minutes old and has never been seen before.
- Threat Extraction (Safe Content): When an employee downloads a PDF, Harmony can strip out any hidden "active" code and deliver a 100% safe, cleaned version of the file to the user in less than a second.
- Full Disk Encryption Management: It ensures that every laptop in your company is fully encrypted, so if an employee leaves their computer in a taxi, the data is completely unreadable to whoever finds it.
- Forensic Analysis Reports: For every attack it stops, it generates a "forensic" report that shows exactly how the threat tried to get in, what it tried to do, and which other computers might be at risk.
Pricing: A "Harmony Endpoint Elite" subscription license costs approximately $152.00 USD per user/year when purchased through major resellers like CDW.
Why it matters: Your employees' laptops are the most vulnerable part of your business. Harmony Endpoint reduces risk by providing a "last line of defense" that is smart enough to fix itself even after a hack has started.
Which one should you choose?
If you are a small team looking for the biggest "win" with the least effort, starting with Cisco Umbrellait takes minutes to set up and blocks a massive percentage of web threats. If you are a developer or a tech-heavy startup, your first priority should be HashiCorp Vault to ensure you aren't leaving the keys to your database in your code. For established companies that need to manage a growing team, Okta is the most important tool for keeping control over who has access to your business.
How does this connect to building a strong career or portfolio?
In cybersecurity, employers don't care about what you "know", they care about what you have "done." If you can show a portfolio project where you set up a HashiCorp Vault instance to secure a web app, or an audit report you generated using Rapid7, you are providing "Proof of Work." At Fueler, we help you document these technical wins. By showcasing the actual workflows you've built with these tools, you prove to hiring managers that you have the hands-on skills to reduce their company's risk from day one.
Final Thoughts
Reducing security risks isn't about buying every tool on this list; it's about picking the ones that solve your biggest weaknesses. Whether it’s managing identities with Okta or protecting your network with Palo Alto, each of these tools is a building block for a safer business. The goal is to create a workflow where security is "built-in," not just added on at the end. Start with one tool, master its features, and you'll find that your risk goes down while your professional value goes up.
FAQs
1. Is Okta's pricing affordable for a very small startup with only 5 people?
While Okta has a "Starter" plan for $6/user, many small startups find the total cost increases due to the "SSO Tax," where other software companies charge more to let you use Okta. For a 5-person team, using Google Workspace's built-in security is often a more budget-friendly starting point.
2. Can I learn how to use Palo Alto firewalls without buying the expensive hardware?
Yes! Palo Alto offers "Virtual Lab" environments and student versions of their software that you can run on your own computer to learn. This is a fantastic way to build your portfolio without spending thousands of dollars on physical gear.
3. Does Zscaler replace the need for a traditional office firewall?
For many modern companies, the answer is yes. Since most work happens in the cloud (like Gmail or Slack), a cloud-based gateway like Zscaler is often more effective than a physical box sitting in a mostly empty office.
4. How long does it take to get a "HashiCorp Vault" certification?
Most professionals spend 2 to 4 months of hands-on practice before taking the Vault Associate exam. Having this certification on your Fueler portfolio is a huge signal to high-paying tech companies.
5. What is the difference between Nessus (from the previous blog) and Rapid7 InsightVM?
Nessus is great for "point-in-time" scans, like a one-time checkup. Rapid7 InsightVM is built for "continuous" monitoring, meaning it stays active all the time to find new problems the second they appear.
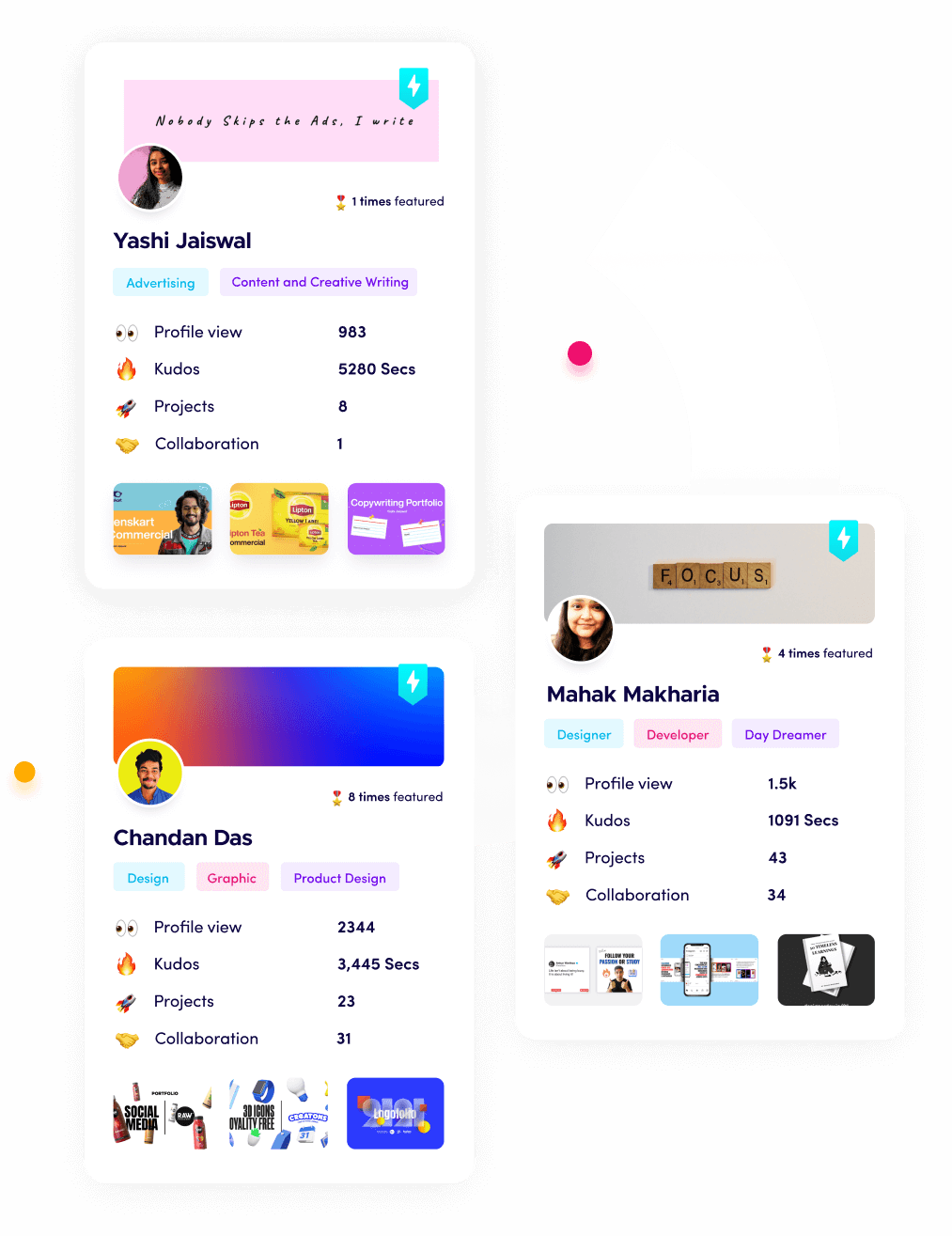
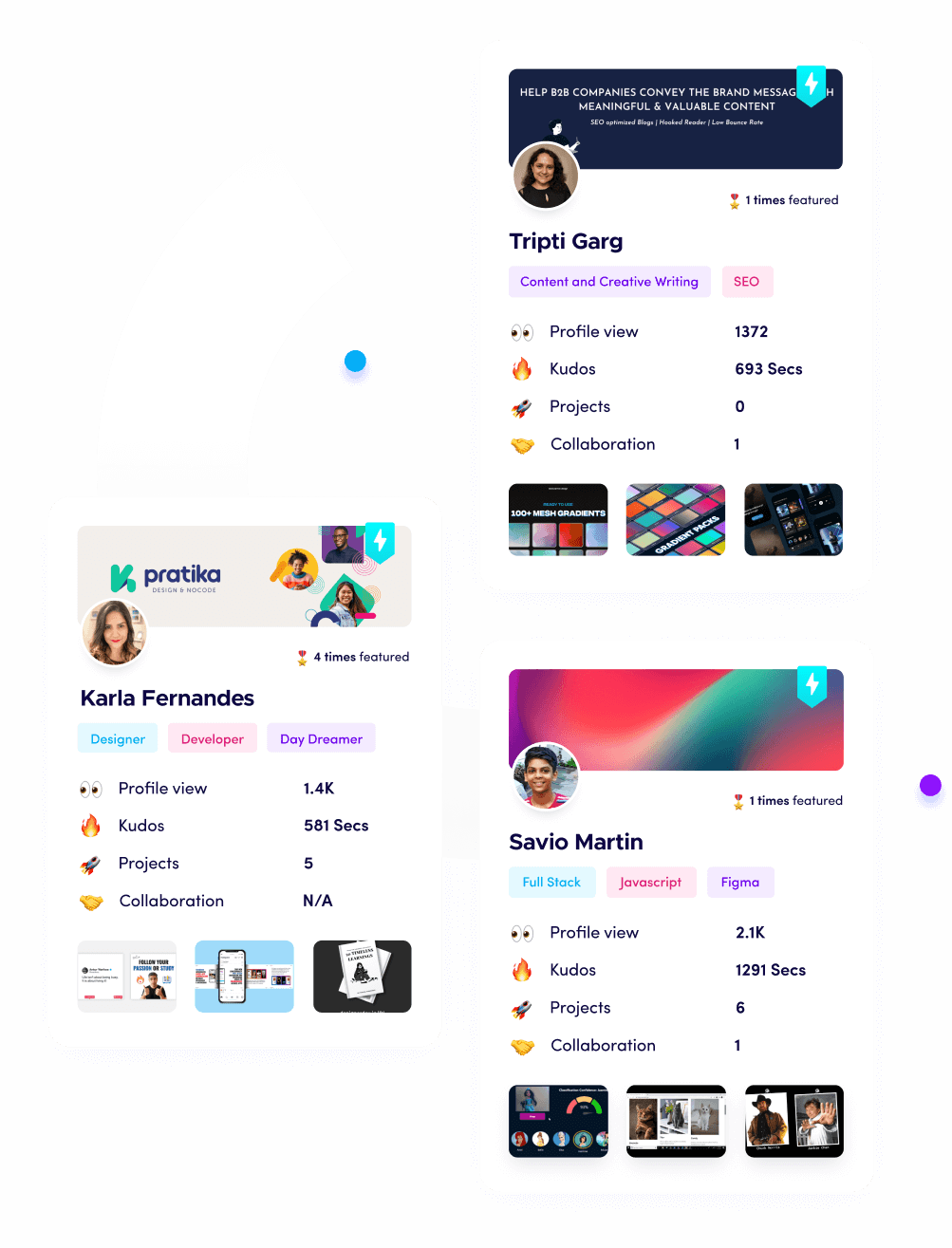
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.