7 AI Tools That Help Monitor Security Risks in Real Time

Riten Debnath
30 Apr, 2026

Last updated: April 2026
Hackers don't sleep, they don't take coffee breaks, and they certainly don't wait for your IT team to clock in at 9 AM to start an attack.
In the time it took you to read that sentence, thousands of automated bots just tried to brute-force their way into company databases across the globe. For a modern business, checking the logs once a week is like locking your front door but leaving all the windows open while you go on vacation. You need eyes on your data every single second. While everyone is shouting about AI right now, the truth is that many of the world’s most secure systems rely on rock-solid, high-performance monitoring tools that focus on visibility, human expertise, and immediate response.
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
Before we dive into the list, let’s be clear: real-time monitoring isn't just about catching "bad guys." It’s about operational health. It’s knowing when a server is overheating, when an employee accidentally shares a private folder, or when a weird surge in traffic suggests a DDoS attack is brewing. Here are the 7 best tools actually being used by professionals in 2026.
At a glance: Comparing the AI Tools That Help Monitor Security Risks in Real Time
1. CrowdStrike Falcon
Best for: Unified endpoint protection and enterprise-scale cloud security.
CrowdStrike Falcon is the undisputed heavyweight champion for protecting endpoints, which is just a technical way of saying any device connected to your network, like laptops, mobile phones, or servers. It operates as a single, tiny piece of software that stays in the background and watches for suspicious activity across your entire company. It is famous for being incredibly fast to deploy, meaning a company with 10,000 employees can get fully protected in hours rather than weeks.
- Unified Threat Graph: This feature creates a massive visual map of every relationship between files, users, and devices, allowing security teams to see exactly how a potential threat is trying to move through the company network in real time.
- Lightweight Single Agent: Unlike old-school antivirus software that makes your computer loud and slow, Falcon uses less than 1% of your CPU power, ensuring that your team stays productive and doesn't try to disable the security software out of frustration.
- Overwatch Managed Hunting: This is a 24/7 "human-in-the-loop" service where actual cybersecurity experts from CrowdStrike watch your data alongside the software to catch the tiny, subtle signs of an attack that a program might miss.
- Device Control Visibility: It gives administrators a clear view of every USB drive or external device being plugged into company hardware, preventing data theft from "insider threats" or accidental malware infections from lost thumb drives.
- Mobile Threat Defense: It extends the same level of enterprise security to Android and iOS devices, which is critical in 2026 because so much work happens on personal phones that are often the weakest link in a company's armor.
Pricing: Falcon Go (Small Business) starts at $59.99 per device annually. Falcon Pro is $99.99 per device annually, and Falcon Enterprise is $184.99 per device annually.
Why it matters: It provides a "silent" security layer. Most employees will never even know it is running, yet it acts as a digital bodyguard that is constantly updated with the latest threat data from millions of other protected devices worldwide.
2. SentinelOne Singularity
Best for: Automated threat mitigation and ransomware recovery.
SentinelOne is the primary rival to CrowdStrike and is best known for its "Singularity" platform. What makes this tool special is its focus on autonomy. While other tools might send an alert to a human and wait for instructions, SentinelOne is designed to identify a threat and kill it instantly. It is particularly popular with mid-sized businesses that don't have a 50-person security team sitting in a dark room watching screens all day.
- 1-Click Remediation and Rollback: This is the "magic" feature that allows an admin to click one button to undo any changes a hacker made, such as restoring files that were encrypted by ransomware back to their original healthy state.
- Ranger IoT Discovery: It automatically scans your network to find every "Internet of Things" device, from smart lightbulbs to printers, ensuring that a hacker can't use a smart fridge as a back door into your private server.
- Storyline Technology: Instead of giving you a list of 500 confusing alerts, it groups related events into a single "story" that shows exactly where the attack started, what it touched, and where it tried to go.
- Full Remote Shell: This allows security professionals to securely log into an infected device from anywhere in the world to perform deep forensic investigations without needing to physically touch the laptop.
- Binary Vault: It keeps a record of every piece of code that has run on a device, which is essential for understanding "Zero Day" attacks, where the hacker uses a brand new method that nobody has seen before.
Pricing: Singularity Core starts at $69.99 per endpoint per year. Singularity Control is $79.99 per endpoint per year, and the full Singularity Complete package is $179.99 per endpoint per year.
Why it matters: It gives you a "time machine" for your data. The ability to "Rollback" a ransomware attack can be the difference between a 10-minute annoyance and a multi-million dollar business failure.
3. Splunk Enterprise Security
Best for: Massive data analysis and high-level security operations.
If your business generates a mountain of data every day, Splunk is the tool you use to make sense of it. It is a "SIEM" (Security Information and Event Management) tool, which means it pulls in data from your firewalls, your servers, your cloud accounts, and even your badge-in scanners at the office. It is effectively a giant search engine for everything happening in your company, allowing you to find the "needle in the haystack."
- Customizable Security Dashboards: You can build visual screens that show your company's health in real time, with green lights for "all clear" and red flashing lights for "urgent attack," tailored specifically to your business needs.
- Splunk Processing Language (SPL): This is a powerful search language that lets your experts write complex queries to find very specific patterns, like "Show me every user who logged in from two different countries in less than one hour."
- Incident Review & Workflow: When a threat is found, Splunk creates a digital "case file" that tracks every step of the investigation, ensuring that your team follows the correct legal and technical steps to fix the problem.
- Asset & Identity Correlation: It automatically links a weird IP address to a specific employee and their specific laptop, saving your security team hours of manual work trying to figure out "who belongs to this device."
- Extensive App Ecosystem: With over 2,000 pre-built apps, you can connect Splunk to almost any software on earth, from Microsoft Office 365 to your Amazon Web Services (AWS) cloud hosting.
Pricing: Splunk uses a "Workload" or "Ingestion" model. Ingestion pricing for small volumes typically starts around $1,800 to $2,000 per year for 1GB of data per day, but most enterprises negotiate custom contracts in the five or six-figure range.
Why it matters: It provides the "Big Picture." Most breaches happen because small, boring events in different parts of the company aren't connected. Splunk connects those dots so you see the forest, not just the trees.
4. Wiz
Best for: Cloud infrastructure security and "Agentless" monitoring.
Wiz has taken the security world by storm because it doesn't require you to install software on every single server. Instead, it connects directly to your cloud providers like AWS, Google Cloud, or Azure. It scans your entire cloud "architecture" in minutes and tells you exactly where you are vulnerable. It is the go-to tool for startups and tech companies that live entirely in the cloud.
- Agentless Scanning: Because it connects to the cloud API rather than the server itself, it can find vulnerabilities without slowing down your website or requiring your developers to manage complex software updates.
- The Wiz Security Graph: It visualizes your cloud environment to show "attack paths," which are the specific routes a hacker could take from a public-facing website all the way into your private customer database.
- Cloud Detection and Response (CDR): It monitors your cloud logs in real time to catch active attacks, such as someone trying to create a new "Admin" user without permission or trying to download your entire database.
- Compliance Reporting: It automatically checks your setup against legal standards like SOC2 or GDPR, giving you a ready-to-go report that you can show to auditors or big clients to prove you are safe.
- Vulnerability Management: It identifies every piece of outdated software in your cloud and ranks them by "Risk Score," so your team knows exactly which 3 things to fix today instead of staring at a list of 3,000 errors.
Pricing: Wiz does not publish flat rates, as pricing is based on "Workload" volume. Typical entry-level contracts for mid-sized companies start in the $20,000 to $40,000 range per year, with large enterprise deals reaching mid-six figures.
Why it matters: It removes the "blind spots." In the cloud, it is very easy for a developer to accidentally leave a door open. Wiz finds that open door before a hacker does, without needing a single install.
5. Check Point Harmony Endpoint
Best for: Remote workforces and preventing phishing attacks.
Check Point has been around since the early days of the internet, and its Harmony Endpoint tool is built for the modern "work from anywhere" world. It focuses heavily on the web browser, which is where most people spend their workday. It is designed to stop people from clicking on bad links in emails or downloading "infected" PDFs, which remains the number one way companies get hacked.
- Anti-Phishing Engine: It inspects websites in real time as you visit them, blocking "fake" login pages that look like Gmail or Outlook but are actually designed to steal your password.
- Threat Extraction (File Sanitization): When you download a PDF or Word document, Harmony "cleans" it by removing any hidden code or macros before giving you a safe version of the file to read.
- Automatic Forensic Analysis: Every time it blocks a threat, it automatically generates a detailed report explaining where the threat came from and what it tried to do, which is invaluable for legal compliance.
- Zero-Phishing Protection: It prevents employees from reusing their corporate passwords on non-work websites, which stops hackers from using a "leaked" Netflix password to get into a company's financial systems.
- Capsule Docs: It allows you to encrypt specific files so that even if they are stolen or sent to the wrong person, they can only be opened by someone with the correct authorization.
Pricing: Pricing starts at approximately $38 to $50 per device per year, depending on the volume and the specific modules selected.
Why it matters: It protects the human element. You can have the best firewalls in the world, but if an employee clicks a bad link, those firewalls don't matter. Check Point acts as a safety net for human error.
6. Palo Alto Networks Cortex XDR
Best for: Companies already using Palo Alto firewalls who want total integration.
Cortex XDR is unique because it is designed to "stitch" together data from your network, your endpoints, and your cloud. If you are already using Palo Alto firewalls at your office, Cortex is the logical next step because it allows those firewalls to talk to your laptops and servers. It is built for "Extended Detection and Response," which means it looks at the entire journey of a digital packet from the internet to your hard drive.
- Behavioral Analytics: It learns what "normal" looks like for your company, so if a quiet accountant suddenly starts downloading 50GB of data at 3 AM, it triggers an alarm immediately.
- Stitched Data Telemetry: It combines data from different sources into a single timeline, so you don't have to manually match a "firewall block" with a "laptop alert" to understand what happened.
- Managed Detection and Response (MDR): Palo Alto offers a service where their own elite "Unit 42" threat researchers can take over the monitoring of your network, giving you access to world-class experts.
- Automated Playbooks: You can set up "If This, Then That" rules, like "If a laptop is infected with malware, automatically disconnect it from the Wi-Fi and lock the user's account."
- Smart Search: It allows security teams to search through months of history in seconds to see if a newly discovered global threat has ever been seen inside their own network in the past.
Pricing: Cortex XDR typically ranges from $40 to $100 per endpoint per year, with significant discounts available for companies that already have Palo Alto hardware contracts.
Why it matters: It stops "Siloed" security. By forcing your network and your computers to talk to each other, you catch hackers who try to hide in the gaps between different security products.
7. Datadog Cloud Security Management
Best for: Developers and DevOps teams who need security built into their monitoring.
Datadog started as a tool for developers to watch their website's performance, but it has evolved into a powerful security platform. It is perfect for "DevSecOps," which is a fancy way of saying security is part of the development process. If your website goes down or gets slow because of a hacker, Datadog will show you the security alert right next to the performance graph.
- Real-Time Threat Detection: It monitors your server logs and cloud traffic for known attack patterns, such as "SQL Injection" or "Cross-Site Scripting" (XSS) attacks on your website.
- Cloud Security Posture Management (CSPM): It constantly audits your AWS or Azure settings to make sure you haven't accidentally turned off a password requirement or made a private folder public.
- Workload Security: It watches the "heartbeat" of your servers, flagging any weird processes that start running, which could indicate that a hacker has gained control of your system.
- Application Security Management (ASM): It protects the actual code of your website, identifying "bugs" that a hacker could exploit and blocking them before they can be used.
- Unified Observability: It puts security data, performance data, and cost data in one place, so the entire company, from the CEO to the junior developer, is looking at the same reality.
Pricing: Datadog is modular. Cloud Security Management starts at $10 per host per month for the Pro plan and $25 per host per month for the Enterprise plan (billed annually).
Why it matters: It speaks the language of developers. When security is built into the tools that developers already use every day, they are much more likely to fix problems quickly.
Which one should you choose?
Selecting the right tool depends entirely on your business structure. If you are a large corporation with thousands of laptops and a dedicated security team, CrowdStrike Falcon or Palo Alto Cortex XDR are the industry leaders for a reason: they offer the deepest visibility and integration.
If you are a smaller team or a fast-growing startup that lives entirely on the web, Wiz is likely your best bet because it’s "agentless" and won't slow down your growth. For those who are terrified of ransomware and want an "undo" button, SentinelOne is the winner. If you already use Datadog to watch your website’s uptime, simply adding their Cloud Security module is the most efficient way to get protected without learning a whole new system.
How does this connect to building a strong career or portfolio?
Understanding these tools isn't just for "security nerds, "it's a massive career advantage for anyone in tech. Companies aren't just hiring people who can "code" or "manage projects" anymore; they are hiring people who understand how to keep the company's assets safe while doing so.
When you build your portfolio on Fueler, you can showcase your knowledge of these systems by documenting projects where you implemented security best practices. Whether it’s a report on how you configured a secure cloud environment or a case study on improving a team's phishing awareness, showing proof of your work is what gets you hired. High-growth companies look for professionals who think about risk, and having a portfolio that demonstrates "Security-First" thinking is a major competitive edge in 2026.
Final Thoughts
The "perfect" security setup doesn't exist, but a "proactive" one does. Real-time monitoring is about reducing the time a hacker spends inside your system from months to seconds. By choosing a tool that fits your team's workflow, whether that’s a deep-data tool like Splunk or a browser-focused shield like Check Point, you are moving from a "hope for the best" strategy to a "ready for anything" reality. Stay curious, keep your software updated, and always prove your skills with real work.
FAQs
1. What are the best free security monitoring tools for small businesses in 2026?
While the enterprise tools listed above are paid, small businesses can start with open-source options like Wazuh or Snort. However, keep in mind that free tools often require much more manual setup and technical expertise than "plug-and-play" options like CrowdStrike.
2. Is real-time security monitoring worth the cost for a startup?
Absolutely. The average cost of a data breach for a small business is now over $100,000, which can be a death sentence for a startup. Investing in a tool like Wiz or SentinelOne early on is significantly cheaper than dealing with a single ransomware attack.
3. Do I need a dedicated security team to use these tools?
Not necessarily. Tools like SentinelOne and Check Point are designed with heavy automation so that a general IT manager or even a tech-savvy founder can manage them. For more complex tools like Splunk, you might need a specialist or a "Managed Service Provider" (MSP).
4. How does real-time monitoring differ from traditional antivirus?
Traditional antivirus software only looks for "known" viruses (like a digital wanted poster). Real-time monitoring (EDR/XDR) looks at behavior. It doesn't care if it recognizes the file; it cares if that file is acting like a thief by trying to access things it shouldn't.
5. How often should a business audit its security tools?
At a minimum, you should do a deep audit once a year. However, with the speed of tech in 2026, many companies now perform "Continuous Auditing" using tools like Wiz or Datadog that flag misconfigurations the second they happen.
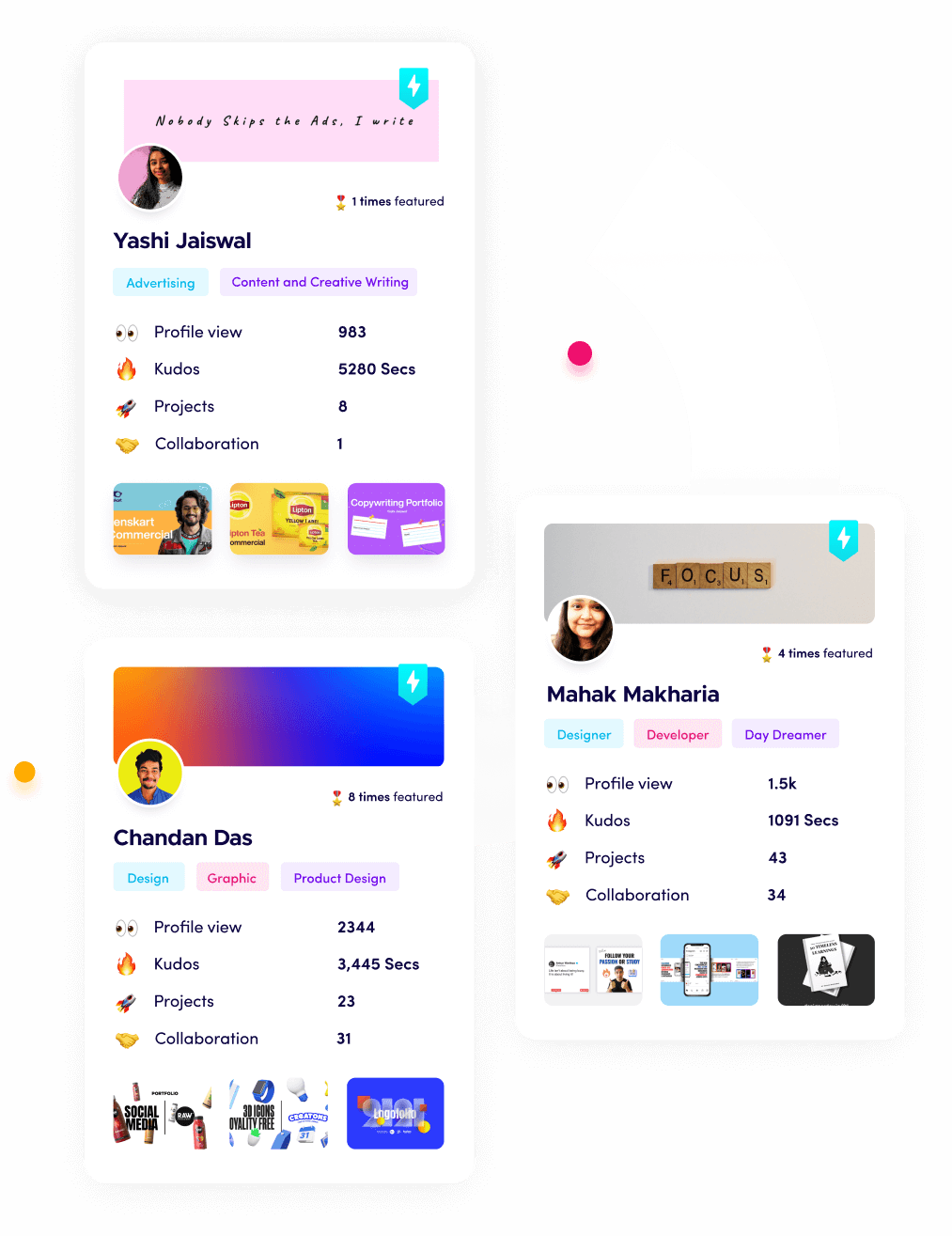
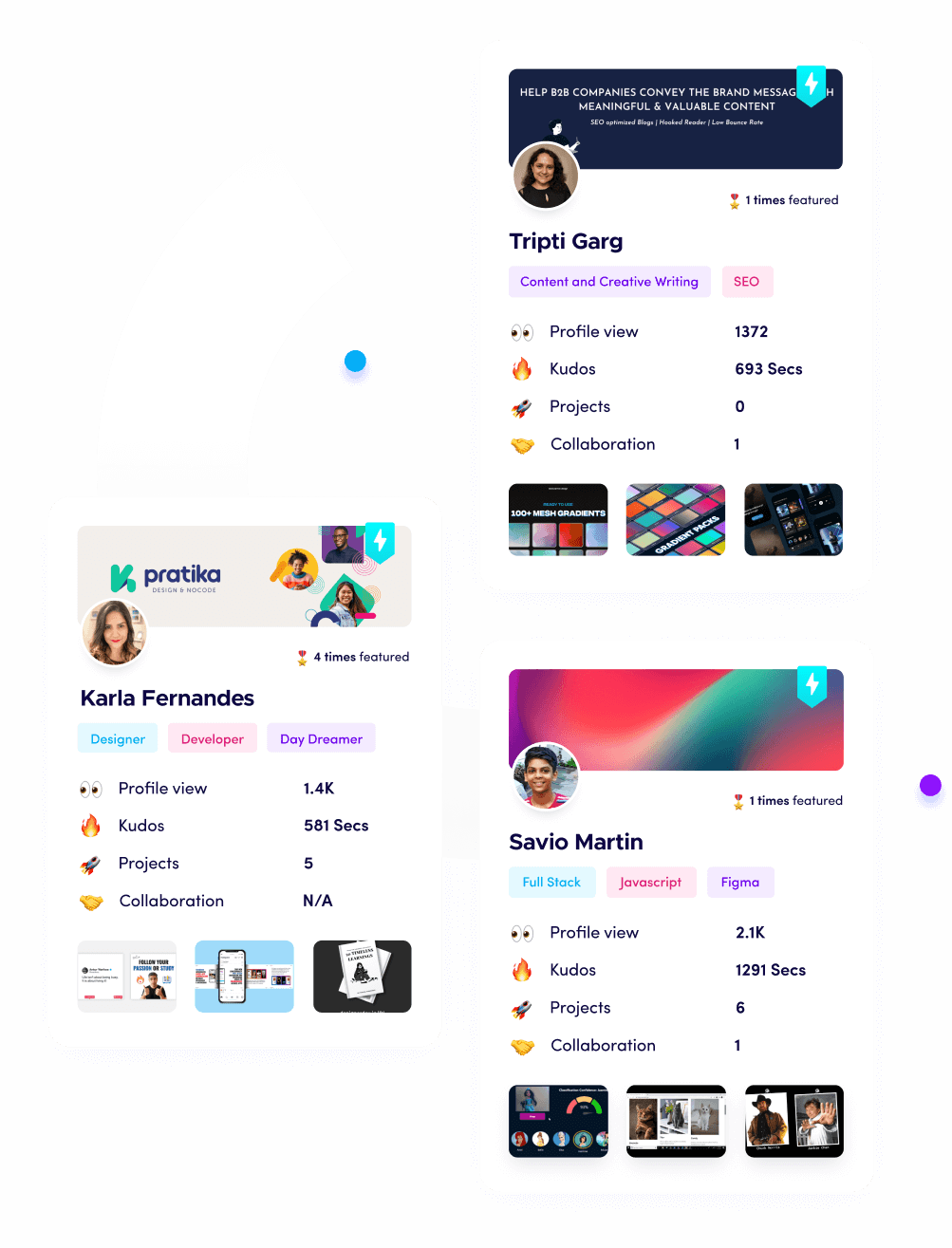
What is Fueler Portfolio?
Fueler is a career portfolio platform that helps companies find the best talent for their organization based on their proof of work. You can create your portfolio on Fueler. Thousands of freelancers around the world use Fueler to create their professional-looking portfolios and become financially independent. Discover inspiration for your portfolio
Sign up for free on Fueler or get in touch to learn more.