9 AI Cybersecurity Agents Detecting Threats in Real Time

Riten Debnath
27 Feb, 2026

If you think hackers are still just teenagers in hoodies eating pizza in a basement, you’re living in 2010. Today, cyberattacks are launched by high-speed AI bots that can scan your entire network for a single open port faster than you can refresh your Twitter feed. It’s a digital arms race, and if you’re still relying on manual firewalls and "strong passwords," you’re essentially bringing a toothpick to a laser fight. Fortunately, we now have autonomous AI cybersecurity agents that act as digital bouncers; they never sleep, they don't get bored, and they can spot a threat before it even touches your data.
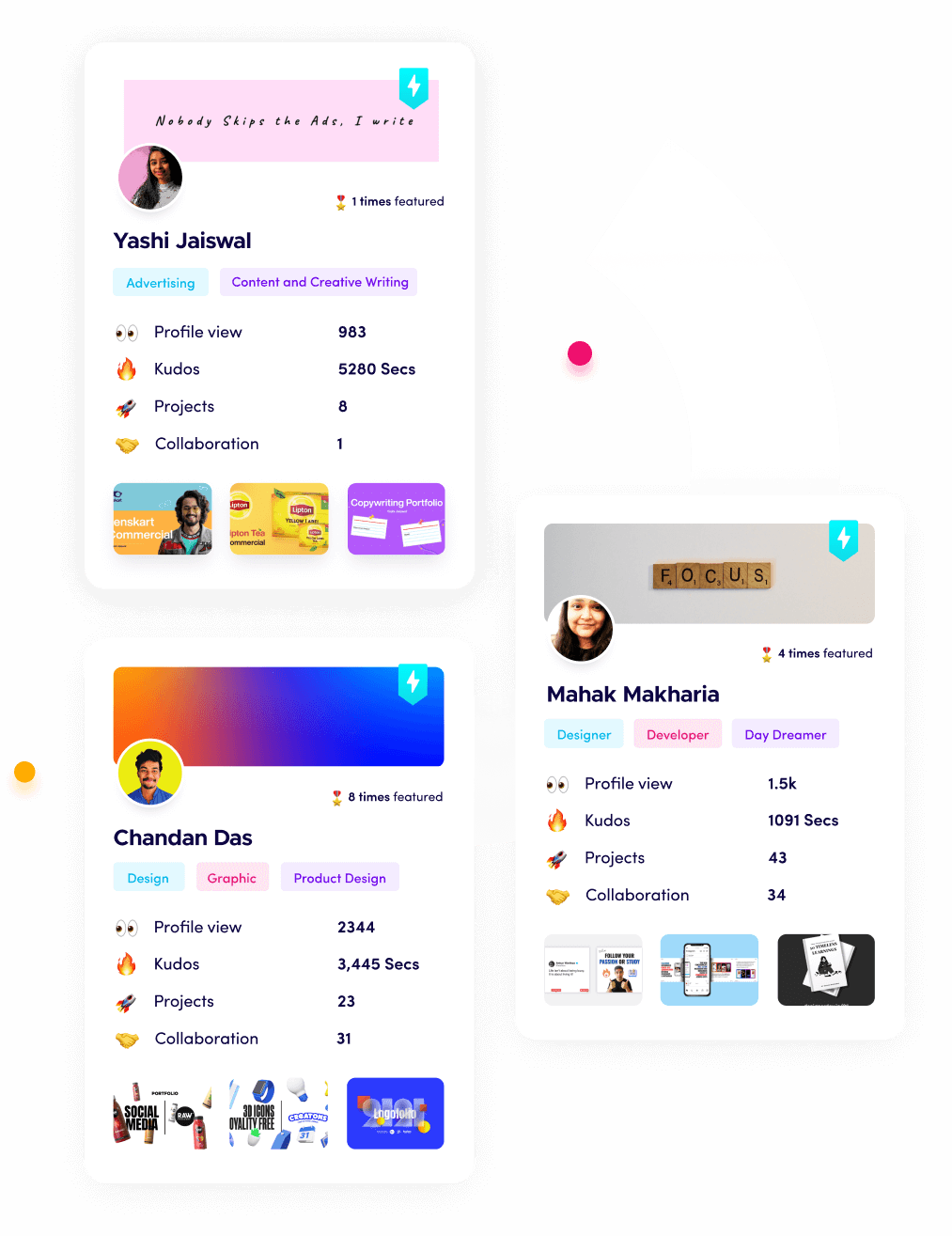
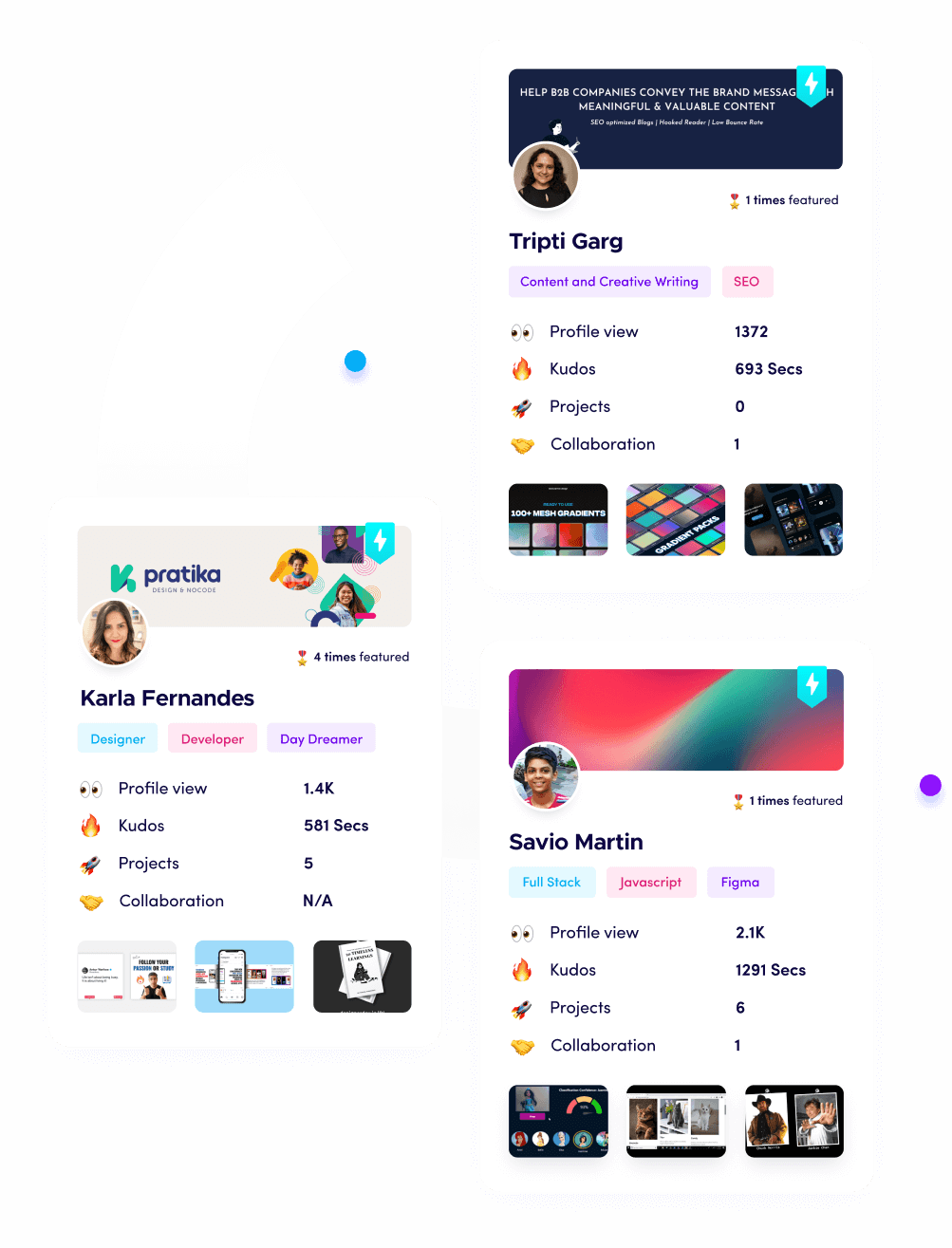
I’m Riten, founder of Fueler, a skills-first portfolio platform that connects talented individuals with companies through assignments, portfolios, and projects, not just resumes/CVs. Think Dribbble/Behance for work samples + AngelList for hiring infrastructure.
1. CrowdStrike Charlotte AI
Charlotte AI is the digital equivalent of a super-genius detective who has memorized every crime ever committed in history. Built directly into the Falcon platform, this agent uses massive amounts of global data to understand the context of an attack, distinguishing between a developer doing a late-night update and a hacker trying to move sideways through your network. It doesn't just bark at every shadow; it explains exactly what is happening in plain English, allowing you to stop breaches at a speed that feels like you're cheating at life.
- Real-time Adversary Tracking and Intelligence: This agent monitors the behavior of known hacking groups across the entire globe and cross-references their patterns with your network activity to catch "living-off-the-land" attacks that traditional antivirus software would completely miss. It is constantly updated with new threat data, meaning that as soon as a new hacking technique is discovered in one part of the world, your system is already immunized against it before the news even breaks.
- Natural Language Security Queries for Faster Insight: Instead of writing complex scripts to find out who accessed a sensitive database, you can literally just ask Charlotte, "Has anyone from an unrecognized IP looked at our customer data today?" and get an instant, accurate answer. This removes the technical barrier for security managers, allowing them to investigate potential leaks in seconds rather than waiting for a specialized analyst to dig through millions of lines of raw server logs.
- Automated Incident Summarization and Reporting: When a potential threat is detected, the AI generates a detailed narrative of exactly how the attacker tried to get in, what they touched, and how to kick them out, saving your security team hours of manual investigation. These reports are written in clear, non-technical language, making it easy to share critical updates with stakeholders who need to know the business risk without getting bogged down in the bits and bytes.
- Predictive Threat Hunting and Discovery: It doesn't wait for a virus to trigger an alarm, it proactively searches for tiny inconsistencies in your system's behavior that might indicate a sophisticated attacker is currently hiding in your environment and waiting for the right moment. By identifying these "weak signals" early, the agent can neutralize a threat during the reconnaissance phase, long before any data is actually encrypted or stolen from your company's private servers.
- One-Click Remediation Scripts and Execution: Once a threat is confirmed, the agent can automatically generate and execute the exact code needed to isolate the infected device and close the security hole, preventing the attack from spreading to the rest of the company. This instant response is critical in the world of modern ransomware, where a delay of even five minutes can be the difference between a minor blip and a company-wide digital catastrophe.
Pricing: * Falcon Go: $59.99 per device annually.
- Falcon Pro: $99.99 per device annually.
- Falcon Enterprise: $184.99 per device annually.
2. Darktrace HEAL
Darktrace HEAL is like having a medical team for your network that can perform surgery while the patient is still running a marathon. It specializes in "Self-Healing" technology, which means when an attack like ransomware strikes, the agent doesn't just cut off the internet and hope for the best. Instead, it surgically neutralizes the malicious activity while allowing your normal business operations to continue as if nothing happened. It is the ultimate tool for businesses that literally cannot afford a single minute of downtime.
- Autonomous Response and Surgical Containment: When the agent detects an active threat, it takes targeted action to stop the specific malicious behavior without shutting down the entire server or disrupting the work of innocent employees. This precision allows your company to stay operational even during a high-stakes cyberattack, preventing the massive financial losses that typically come from having to take your entire infrastructure offline for emergency "cleaning."
- AI-Generated Incident Playbooks: In the heat of an attack, HEAL creates a bespoke step-by-step guide for your security team, telling them exactly what to do based on the unique way the hacker is behaving in your specific network. These playbooks are updated in real-time as the situation evolves, ensuring that your human defenders are always equipped with the most relevant and effective strategies to counter the attacker's latest moves.
- Simulated Cyber Incident Readiness: You can use the agent to run "shadow" attacks on your own network to see how your systems and your team would react to a real-world disaster without any actual risk to your data. This "digital fire drill" helps you find the weak spots in your armor during a peaceful time, so you aren't trying to figure out your emergency procedures for the first time while your files are being deleted.
- Rapid Recovery and Forensic Reporting: After a threat has been neutralized, the agent helps you roll back affected files to their original state and provides a comprehensive forensic audit of exactly what the attacker tried to accomplish. This speeds up the recovery process from days to minutes, allowing your IT team to focus on long-term improvements rather than spending weeks manually restoring backups and trying to piece together what happened.
- Evolving Learning Model for Unique Networks: Unlike traditional security tools that look for "known bad" signatures, this agent learns what "normal" looks like for your specific business and alerts you to anything that deviates from that baseline. This means it can catch "Zero-Day" attacks that have never been seen before, simply because the behavior of the software doesn't match the unique digital heartbeat of your organization's daily activities.
Pricing: * Subscription-based, typically starting around $30,000 per year for mid-sized environments.
- Prices vary based on the number of protected devices and network complexity.
3. SentinelOne Purple AI
Purple AI is the "Iron Man suit" for your security operations center, designed to turn a junior analyst into a seasoned veteran overnight. It lives inside the Singularity platform and acts as a tireless partner that sifts through billions of logs to find the "needle in the haystack" that represents a real threat. It’s built for teams that are tired of "alert fatigue" and want an agent that can actually think for itself, making decisions about what is dangerous and what is just noise.
- Autonomous Threat Hunting and Storyline Tracking: The agent constantly runs background "stories" on every process in your system, building a timeline of events so it can instantly recognize when a normal application starts behaving like a piece of malicious ransomware. It connects the dots between seemingly unrelated events, like a file being downloaded and a system setting being changed, to uncover the hidden narrative of a sophisticated, multi-stage cyberattack.
- Semantic Search for Massive Security Logs: You can search through months of complicated server data using simple, conversational questions, allowing you to find the root cause of a security issue in seconds rather than spending a whole weekend digging through spreadsheets. This allows your team to perform deep investigative work at the speed of thought, uncovering hidden patterns and historical threats that would otherwise remain buried under a mountain of irrelevant digital noise.
- Automated Defense Playbook Execution: When a specific type of attack is detected, Purple AI can automatically trigger a sequence of defensive moves, like locking down user accounts or cutting off internet access for a specific server, without waiting for a human. These pre-programmed responses ensure that your company's defense is always active, even at 4:00 AM on a Sunday when your human security team might be out of reach or fast asleep.
- Risk-Based Alert Prioritization and Triage: It uses machine learning to rank alerts based on their actual risk to your specific business operations, ensuring that your team spends their time fixing the critical hole in your database rather than a false alarm. By cutting out the clutter, the agent reduces the mental load on your employees, preventing burnout and ensuring that the most dangerous threats never get ignored or lost in the shuffle.
- Binary Analysis and Advanced Sandboxing: The agent can "explode" suspicious files in a safe, isolated environment to see exactly what they do before they are ever allowed to run on your main network. This proactive testing stops "Zero-Day" threats and malicious software from ever gaining a foothold in your system, providing a high-tech "quarantine zone" that protects your most valuable data from being infected by unknown or experimental viruses.
Pricing: * Singularity Core: $179.99 per endpoint per year.
- Singularity Control: $209.99 per endpoint per year.
- Singularity Complete: $269.99 per endpoint per year.
4. Palo Alto Networks Precision AI
If you are running a massive enterprise with thousands of employees, Palo Alto Networks Precision AI is the heavy-duty security engine you need to keep the gears turning. This agent is built into their famous firewalls and cloud security tools, using a "Zero Trust" approach where it trusts absolutely no one until they've been verified by the AI. It is designed to secure everything from your office laptops to your complex cloud databases, acting as a unified shield that covers every possible inch of your digital territory.
- Inline Deep Learning Threat Prevention: This agent sits directly in the path of your internet traffic, using deep learning models to inspect every single packet of data as it passes through your firewall in real-time. It can identify and block malicious code hidden inside encrypted traffic without slowing down your connection, providing a "bulletproof" layer of security that catches threats before they even reach your internal network or your employees' devices.
- Automated Cloud Security Posture Management: It constantly scans your cloud environments (like AWS or Azure) to make sure you haven't accidentally left a "digital window" open, such as an unencrypted database or an overly permissive user account. By automatically fixing these misconfigurations, the agent prevents the most common cause of cloud data breaches, ensuring that your infrastructure remains secure even as your developers are constantly changing and updating the code.
- Zero Trust Identity Verification: The agent strictly enforces the rule that every person and every device must be constantly verified before they are allowed to access sensitive company data. It looks at the user's location, their device health, and their current behavior to decide if they are actually who they say they are, effectively neutralizing the threat of stolen passwords and hijacked employee accounts in one fell swoop.
- Advanced URL Filtering and Phishing Protection: It uses AI to analyze new websites the moment they are created, identifying "fake" login pages and malicious domains before your employees have a chance to click on them and give away their credentials. This real-time protection is essential for stopping modern phishing campaigns, which often use "disposable" websites that only stay active for a few hours to avoid being caught by traditional security blacklists.
- IoT and Unmanaged Device Security: The agent identifies every single "smart" device on your networkfrom office cameras to smart lightbulbsand monitors them for unusual behavior that might indicate they've been hacked and turned into a botnet. This closes a massive security hole that most companies ignore, ensuring that even your non-computer hardware isn't being used as a secret "backdoor" for hackers to enter your main corporate network.
Pricing: * Next-Gen Firewalls: Hardware starts at $1,000; Security subscriptions (Precision AI) typically cost $500 - $2,000+ per year.
- Prisma Cloud: $9,000 per 100 credits annually.
5. Check Point Infinity AI Copilot
Check Point Infinity AI Copilot is the ultimate "security secretary" that helps you manage your entire company's defense from a single, simple chat interface. Instead of clicking through a thousand different menus to change a firewall rule, you just tell the Copilot what you want to do and it handles the technical configuration for you. It’s perfect for companies that have a lot of different security tools and want a centralized "brain" to coordinate all of them and make sure they are working together.
- Conversational Policy Management and Updates: You can create or update complex security policies by simply typing instructions like "Block all traffic from high-risk countries to our accounting server" into the chat interface. This automation removes the risk of human error when configuring firewalls, ensuring that your security rules are always precise, effective, and easy to understand for everyone on the IT team, regardless of their skill level.
- AI-Guided Incident Investigation and Triage: When something suspicious happens, the Copilot analyzes the logs and tells you exactly what the problem is, how serious it is, and what steps you should take to fix it. This acts as a "second pair of eyes" that never gets tired, helping your team filter through the noise of daily operations to find the real threats that require immediate attention and professional remediation.
- Automated Threat Hunting at Scale: The agent proactively searches across your entire network, cloud, and mobile devices to find hidden threats that might have bypassed your initial defenses. It uses collaborative intelligence from thousands of other companies to stay updated on the latest hacking trends, ensuring that your business is protected by the collective knowledge of the entire global security community in real-time.
- Instantly Applied Controls and Detection Rules: When a new cyber-vulnerability is discovered (like a "Log4j" style crisis), the Copilot can instantly apply the necessary patches and detection rules across your whole company with a single command. This "zero-day" response capability is what keeps your business safe during global digital outbreaks, allowing you to shield your systems in seconds while other companies are still reading the news.
- Integrated Training and User Safety Education: The agent can identify when an employee is repeatedly making risky security choices and automatically provide them with targeted training to help them stay safe. By turning your employees from "security risks" into "security assets," the AI helps build a stronger culture of safety within your company, reducing the likelihood of a successful attack caused by simple human mistakes.
Pricing: * Part of the Check Point Infinity Platform; estimated at around $5,000 - $10,000 per year for standard enterprise modules.
- Direct quotes are required for the full AI Copilot suite based on user count.
6. Vectra AI Platform
Vectra AI is like having a private investigator who specializes in "lateral movement," which is how hackers move from one part of your network to another after they get inside. While other tools focus on the "front door," Vectra focuses on what happens after someone has broken in, watching for the tiny, subtle signs of an attacker trying to steal your most sensitive data. It is the gold standard for detecting "insider threats" and advanced persistent threats (APTs) that are designed to stay hidden for months.
- Attack Signal Intelligence and Noise Reduction: This agent uses patented AI to separate "malicious intent" from "normal network noise," reducing your daily alert volume by up to 99% so you only see the threats that actually matter. By focusing only on high-fidelity signals, your security team can stop wasting time on "false alarms" caused by legitimate software and spend their energy hunting down real hackers who are trying to hide.
- Multi-Domain Attack Chain Visualization: It creates a visual "storyboard" of an attack as it happens, showing you exactly where the hacker started, what accounts they've hijacked, and which servers they are currently targeting. This clear picture allows your team to understand the "big picture" of a breach instantly, making it much easier to decide where to place your defenses and how to cut off the attacker's path forward.
- Agentless Cloud and Identity Detection: The agent can monitor your cloud environments (AWS, Azure, M365) without requiring you to install any software on your individual servers, making it incredibly easy and fast to deploy. It watches how your users are interacting with your cloud apps and alerts you the moment someone starts downloading an unusual amount of data or trying to access files they shouldn't have permission to see.
- Automated Triage and Threat Prioritization: It automatically ranks every detected threat on a scale of 1 to 10, ensuring that your team always knows exactly which fire to put out first during a busy day. This data-driven approach to security ensures that your most valuable assets, like customer credit card data or intellectual property, are always the first things the AI acts to protect when a breach is detected.
- Seamless Integration with EDR and SIEM: It works perfectly with your existing security tools, feeding them high-quality data and "triggering" them to take action, like isolating a laptop or blocking a user account. This makes Vectra the "brain" of your security operation, coordinating all your different defenses to make sure they are working in perfect harmony to stop an attacker from reaching their final goal.
Pricing: * Standard Platform: $499 per month.
- Complete Platform (including MDR): $1,299 per month.
- Custom enterprise quotes available for very large networks.
7. Sophos Managed Detection and Response (MDR)
Sophos MDR is the perfect "hybrid" solution, combining a 24/7 team of human elite threat hunters with a high-powered AI agent that manages your defenses around the clock. The AI handles the "heavy lifting" of scanning millions of events every second, and when it finds something truly suspicious, it hands it off to a human expert to finish the job. It’s like having a security system that doesn't just call the police, but actually has the SWAT team already sitting in your parking lot ready to jump into action.
- 24/7 Human-Led and AI-Powered Threat Hunting: You get the best of both worlds: a tireless AI agent that watches your network every second of every day, and a team of human experts who can step in to handle the most complex and creative attacks. This ensures that you are protected against both automated bot attacks and "hands-on-keyboard" hackers who are actively trying to find a clever way around your specific company's security settings.
- Deep Learning Malware Detection and Prevention: The agent uses an advanced "deep learning" neural network to identify new types of malware that haven't even been named yet, stopping them before they can encrypt a single file. This technology is far more effective than traditional antivirus software because it looks at the "DNA" of a file rather than just its name or its history, allowing it to catch even the most experimental and modern digital threats.
- Synchronized Security for Instant Response: When the agent detects a threat on one laptop, it can instantly tell your firewall to block that device from the rest of the network, preventing the "infection" from spreading to other employees. This "teamwork" between your hardware and software is handled entirely by the AI, ensuring that your company's defense is always faster and more coordinated than the attacker's attempts to move through your system.
- Managed Risk and Compliance Reporting: The agent provides regular reports on your company's "health," pointing out where you have security holes and providing a clear path to fix them before a hacker finds them first. This constant improvement process helps your business stay compliant with insurance requirements and legal regulations, making it much easier to prove to your customers that their data is safe and well-protected under your care.
- Flexible Deployment for Any Infrastructure: Whether your company is entirely in the cloud, entirely in an office, or a mix of both, the agent can be deployed easily to cover all your devices and servers. This "universal" protection means you don't have to buy five different tools for five different types of hardware, simplifying your life and ensuring that there are no "blind spots" where a hacker could hide and wait.
Pricing: * Intercept X Advanced (Endpoint): $28 per user per year.
- Advanced with XDR: $48 per user per year.
- Sophos MDR (Full Service): Starts at $79 per user per year.
8. Trellix XDR Platform (Trellix Wise)
Trellix XDR is an AI-powered engine built for organizations that need a "living" security ecosystem that evolves as fast as the threats do. Their GenAI feature, Trellix Wise, acts as a brilliant consultant that sits inside your security operations center, summarizing complex evidence from diverse sources and suggesting the most effective ways to investigate a breach. It is designed to reduce the "noise" of modern security by prioritizing alerts that represent a true danger to your business while ignoring the harmless background chatter.
- Adaptive Threat Investigation and Response: This agent uses machine learning to analyze telemetry data from your entire network and adjust its defenses in real-time based on the specific behavior of an incoming threat. This means your security posture isn't a static set of rules, but a dynamic, moving target that is constantly changing to block the latest tactics being used by hackers, effectively making your company a much harder target to hit.
- Trellix Wise Generative AI Assistance: This specialized AI feature automatically summarizes complex security incidents into plain English and suggests hypotheses for how an attacker might have entered your system. It saves your senior analysts hours of time by doing the initial "detective work," allowing them to focus on the high-level strategy of containment and recovery rather than being buried under mountains of raw, undeciphered data.
- Behavior-Based Endpoint Detection and MITRE Mapping: The agent uses advanced classification modules to determine if a file is malicious based on how it behaves, rather than just what it is named. It then maps these behaviors directly to the global MITRE ATT&CK framework, giving your team a standardized and professional language to describe the threat and coordinate a response with other global security experts and law enforcement agencies.
- Predictive Vulnerability Management and Prioritization: Instead of trying to patch every single security hole at once, the agent uses predictive analytics to tell you which vulnerabilities are most likely to be exploited by hackers in the next 24 hours. This allows your IT team to work with surgical precision, fixing the most dangerous problems first and ensuring that your limited time and resources are always focused on the areas of highest risk.
- Hyperautomation for Phishing and Credential Theft: You can integrate almost any tool into the Trellix platform to trigger automated responses to common attacks like phishing or credential theft. This means when an employee accidentally clicks a bad link, the agent can instantly reset their password and isolate their account before the hacker has a chance to log in, effectively neutralizing the threat before it can cause any real harm.
Pricing: * Subscription-based tiers tailored to enterprise size.
- Estimated starting price: $10,000 - $25,000 per year for basic XDR modules.
9. Cynet All-in-One Security
Cynet is the "Swiss Army Knife" of AI security, designed specifically for small to mid-sized businesses that need elite protection without the enterprise-level price tag. It combines endpoint protection, network monitoring, and user behavior analytics into a single, lightweight agent that is incredibly easy to deploy. It is famous for its "CyOps" 24/7 team of experts who are included in the price, giving smaller companies the kind of protection that used to be reserved only for the world's largest banks and tech firms.
- Unified Threat Prevention across Multiple Vectors: This agent covers all the base endpoints, networks, and user accounts from a single dashboard, ensuring that there are no "gaps" in your defense. It prevents hackers from finding an unprotected entry point into your business, providing a solid wall of defense that is much more effective than trying to manage five different, disconnected security tools from five different vendors.
- Automated Investigation and Remediation Playbooks: When a threat is detected, the agent automatically runs a series of investigation steps to determine the scope of the problem and then executes a pre-approved fix. This means that even if you don't have a dedicated security expert on staff, the AI is working in the background to clean up infections and close security holes, giving you professional-grade protection on a small-business budget.
- Lightweight Agent for Maximum Performance: Unlike some security tools that make your laptop run like a computer from the 1990s, the Cynet agent is designed to be invisible to the user. It uses very few system resources, ensuring that your employees can stay productive and your servers remain fast while the AI is busy scanning for threats and monitoring for unusual activity in the background.
- 24/7 CyOps Managed Detection and Response: Every Cynet package comes with access to their elite "CyOps" team, who monitor your alerts 24/7 and step in to help if things get too complex for the AI to handle. This gives you the peace of mind of having a professional "911" service for your business, ensuring that expert help is only a click away if you ever find yourself in the middle of a serious cyberattack.
- Deception Technology and "Honeypots": The agent can set up digital "traps" (honeypots) that look like valuable servers or databases to a hacker but are actually fake environments monitored by the AI. When a hacker tries to touch one of these traps, the agent instantly alerts you to their presence, allowing you to catch them red-handed before they ever get near your company's real data or sensitive financial information.
Pricing: * Elite Tier: Starting at $7 per month per endpoint.
- All-in-One Tier: Starting at $10 per month per endpoint.
Showcase Your Skills on Fueler
While these AI cybersecurity agents are busy guarding your data and fighting off invisible hackers, you should be busy proving to the world what you’re capable of building. At Fueler, we know that in the modern tech world, a boring PDF resume isn't enough to get you the job of your dreams. Whether you are a security researcher, a developer, or a creative professional, you can use Fueler to build a dynamic portfolio that showcases your actual work samples, projects, and assignments. It’s the easiest way to show potential employers that you don't just "know" about technology, you know how to use it to create real value.
Final Thoughts
The reality of 2026 is that you can't win a digital war with manual tools. These AI cybersecurity agents are no longer a luxury; they are the essential backbone of any business that wants to survive the current landscape of high-speed, automated attacks. By deploying these autonomous guardians, you can finally stop worrying about every single alert and start focusing on growing your business with the peace of mind that your data is safe. The future of security is autonomous, and the companies that embrace it today will be the ones standing tall tomorrow.
FAQs
1. What are the best free AI cybersecurity tools for small businesses in 2026?
While most enterprise-grade AI agents are paid, many companies like Sophos and SentinelOne offer free trials or "community editions" that provide basic protection. For small teams, focusing on the free "Cloud Security Posture" tools provided by AWS and Google Cloud is a great way to start automating your security without a massive initial investment.
2. Can AI agents actually stop a ransomware attack before it starts?
Yes, agents like Darktrace and CrowdStrike are specifically designed to catch the "pre-attack" behavior, such as a hacker trying to steal passwords or scanning your servers. By neutralizing the threat during these early stages, the AI prevents the ransomware from ever being downloaded or activated in the first place.
3. Do I still need an IT team if I have an AI security agent?
Absolutely. AI agents are incredibly powerful, but they still need a human to set the overall security strategy and make high-level decisions during a complex crisis. Think of the AI as your 24/7 security guard and your IT team as the Chief of Police who manages the whole operation.
4. How do these AI tools handle my company's private data?
Most modern AI cybersecurity agents are built with "Privacy by Design," meaning they analyze the patterns of your data rather than reading the actual content of your private emails or documents. They are designed to meet strict global standards like GDPR to ensure that your security doesn't come at the cost of your privacy.
5. How much does a typical AI cybersecurity agent cost for a small team?
For a small team of 10-20 people, you can expect to pay anywhere from $500 to $2,000 per year for high-quality endpoint protection like CrowdStrike or Sophos. While it might seem like a high cost, it is much cheaper than the average $4 million cost of a single data breach.